DocumentoHacking - CEH Cheat Sheet Exercisescargado por
DocumentoHacking - CEH Cheat Sheet Exercisescargado por rgolfnut1
rgolfnut1 DocumentoRapsodo Mobile Launch Monitor Review The Breakfast Ballcargado por
DocumentoRapsodo Mobile Launch Monitor Review The Breakfast Ballcargado por rgolfnut1
rgolfnut1 DocumentoSheriff's Sale No. 2018-13893cargado por
DocumentoSheriff's Sale No. 2018-13893cargado por rgolfnut1
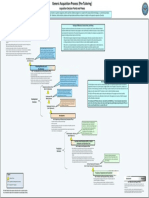
rgolfnut1 DocumentoDefense Acquisition Process Waterfall Methodcargado por
DocumentoDefense Acquisition Process Waterfall Methodcargado por rgolfnut1
rgolfnut1 DocumentoFundamentals of System Acquisition Mgmt Part2cargado por
DocumentoFundamentals of System Acquisition Mgmt Part2cargado por rgolfnut1
rgolfnut1 DocumentoATTACKS by OSI model Layers DDoS Quick Guide.pdfcargado por
DocumentoATTACKS by OSI model Layers DDoS Quick Guide.pdfcargado por rgolfnut1
rgolfnut1 DocumentoSteganographic Embedding Undetectable by JPEG Compatibility Steganalysis Newman etal2002.pdfcargado por
DocumentoSteganographic Embedding Undetectable by JPEG Compatibility Steganalysis Newman etal2002.pdfcargado por rgolfnut1
rgolfnut1 DocumentoSteganographic Embedding Undetectable by JPEG Compatibility Steganalysis Newman Etal2002cargado por
DocumentoSteganographic Embedding Undetectable by JPEG Compatibility Steganalysis Newman Etal2002cargado por rgolfnut1
rgolfnut1 DocumentoShavlik Patch User Guidecargado por
DocumentoShavlik Patch User Guidecargado por rgolfnut1
rgolfnut1 DocumentoRegistryDecoder Offline Analysis Instructions v1.1 (1)cargado por
DocumentoRegistryDecoder Offline Analysis Instructions v1.1 (1)cargado por rgolfnut1
rgolfnut1 DocumentoFundamental Computer Investigation Guide for Windowscargado por
DocumentoFundamental Computer Investigation Guide for Windowscargado por rgolfnut1
rgolfnut1 DocumentoGolf Swing Speed Training Logcargado por
DocumentoGolf Swing Speed Training Logcargado por rgolfnut1
rgolfnut1 DocumentoRotator Cuff and AB Exercisescargado por
DocumentoRotator Cuff and AB Exercisescargado por rgolfnut1
rgolfnut1 DocumentoLinear Codes - cryptographycargado por
DocumentoLinear Codes - cryptographycargado por rgolfnut1
rgolfnut1 DocumentoCryptography - Lecture1cargado por
DocumentoCryptography - Lecture1cargado por rgolfnut1
rgolfnut1 DocumentoOrthogonal Matricescargado por
DocumentoOrthogonal Matricescargado por rgolfnut1
rgolfnut1 DocumentoLouisian Private Investigator Lawscargado por
DocumentoLouisian Private Investigator Lawscargado por rgolfnut1
rgolfnut1 DocumentoInstallShield AdminStudio ConfiguringRepackage PHrcargado por
DocumentoInstallShield AdminStudio ConfiguringRepackage PHrcargado por rgolfnut1
rgolfnut1 DocumentoInstallShield AdminStudio ConfiguringRepackage PHrcargado por
DocumentoInstallShield AdminStudio ConfiguringRepackage PHrcargado por rgolfnut1
rgolfnut1 DocumentoInstallShield AdminStudio ConfiguringRepackage PHrcargado por
DocumentoInstallShield AdminStudio ConfiguringRepackage PHrcargado por rgolfnut1
rgolfnut1 DocumentoTypes of Forgeriescargado por
DocumentoTypes of Forgeriescargado por rgolfnut1
rgolfnut1 DocumentoStat Formulascargado por
DocumentoStat Formulascargado por rgolfnut1
rgolfnut1 DocumentoEcryptfs Enterprise Linuxcargado por
DocumentoEcryptfs Enterprise Linuxcargado por rgolfnut1
rgolfnut1 DocumentoFatness to Fitness Digital Versioncargado por
DocumentoFatness to Fitness Digital Versioncargado por rgolfnut1
rgolfnut1 DocumentoFEMA ICS200_Student Manualcargado por
DocumentoFEMA ICS200_Student Manualcargado por rgolfnut1
rgolfnut1 DocumentoMold_remediation Instructions Univ South Carolinacargado por
DocumentoMold_remediation Instructions Univ South Carolinacargado por rgolfnut1
rgolfnut1 Documento09.02.10.HashingPasswords Class.csci4621cargado por
Documento09.02.10.HashingPasswords Class.csci4621cargado por rgolfnut1
rgolfnut1 Documento09.02.10.BirthdayParadox.CSC4621cargado por
Documento09.02.10.BirthdayParadox.CSC4621cargado por rgolfnut1
rgolfnut1 Documento9.23.10.Polyinstantiation PDFcargado por
Documento9.23.10.Polyinstantiation PDFcargado por rgolfnut1
rgolfnut1 DocumentoSocket Programmingcargado por
DocumentoSocket Programmingcargado por rgolfnut1
rgolfnut1 Documento47349048 Malware Detection Using OWA Measurecargado por
Documento47349048 Malware Detection Using OWA Measurecargado por rgolfnut1
rgolfnut1 DocumentoGeologic Conditions Beneath New Orleanscargado por
DocumentoGeologic Conditions Beneath New Orleanscargado por rgolfnut1
rgolfnut1 DocumentoAbsolute Value Inequalitiescargado por
DocumentoAbsolute Value Inequalitiescargado por rgolfnut1
rgolfnut1 DocumentoPenetration Testing Sample Reportcargado por
DocumentoPenetration Testing Sample Reportcargado por rgolfnut1
rgolfnut1 DocumentoLinux Security Quick Reference Guidecargado por
DocumentoLinux Security Quick Reference Guidecargado por rgolfnut1
rgolfnut1 DocumentoLimits of Steganographycargado por
DocumentoLimits of Steganographycargado por rgolfnut1
rgolfnut1 Documentogdb-refcardcargado por
Documentogdb-refcardcargado por rgolfnut1
rgolfnut1 DocumentoEmacs Referencecargado por
DocumentoEmacs Referencecargado por rgolfnut1
rgolfnut1 DocumentoArray List ADT'scargado por
DocumentoArray List ADT'scargado por rgolfnut1
rgolfnut1 DocumentoComplex Networkscargado por
DocumentoComplex Networkscargado por rgolfnut1
rgolfnut1 DocumentoSet Theory Functionscargado por
DocumentoSet Theory Functionscargado por rgolfnut1
rgolfnut1
Documentos de Académico
Documentos de Profesional
Documentos de Cultura