Documentos de Académico
Documentos de Profesional
Documentos de Cultura
Ad-Hoc Network Routing and TCP: Class - 2
Cargado por
Vishnu KumarTítulo original
Derechos de autor
Formatos disponibles
Compartir este documento
Compartir o incrustar documentos
¿Le pareció útil este documento?
¿Este contenido es inapropiado?
Denunciar este documentoCopyright:
Formatos disponibles
Ad-Hoc Network Routing and TCP: Class - 2
Cargado por
Vishnu KumarCopyright:
Formatos disponibles
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Ad-hoc Network Routing and TCP
Class -2
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Introduction
Routing protocols used in wired networks cannot be directly applied to ad hoc wireless networks Highly dynamic topology No infrastructure for centralized administration Bandwidth constrained Bandwidth constrained Energy constrained For the above reasons, we need to design new routing protocols for ad hoc networks
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
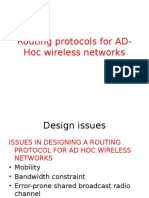
Issues in Designing a Routing Protocol
Mobility: Ad hoc is highly dynamic due to the movement of nodes Node movement causes frequent path breaks The path repair in wired network has slow convergence Bandwidth Constraint: Wireless has less bandwidth due to the limited radio band: Less data rate and difficult to maintain topology information Frequent change of topology causes more overhead of topology maintenance Target: Bandwidth optimization and design topology update mechanism with less overhead
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Issues in Designing a Routing Protocol
Error-prone shared broadcast radio channel: Wireless links have time varying characteristics in terms of link capacity and link-error probability Target: Interact with MAC layer to find better-quality link Hidden terminal problem causes packet collision Target: Find routes through better quality links and find path with less congestion Hidden and exposed terminal problems: RTS-CTS control packet cannot ensure collision free, see Fig. 7.2 Resource Constraints: Limited battery life and limited processing power Target: optimally manage these resources
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Hidden terminal problem with RTSCTS-Data-ACK scheme
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Characteristics of an Ideal Routing Protocol for Ad Hoc
Fully distributed Adaptive to frequent topology changes Minimum connection setup time is desired Localized global maintenance involves a huge state propagation control overhead Loop free and free from stale routes Packet collision must seldom happen
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Characteristics of an Ideal Routing Protocol for Ad Hoc (cont.)
Converge to optimal route quickly Optimally use scarce resource Bandwidth, computing power, memory, and battery Remote parts of the network must not cause updates in the topology information maintained by this node Provide quality of service and support for time sensitive traffic
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Classifications of Routing Protocols
Routing protocol can be broadly classified into four categories : Routing information update mechanism Use of temporal information for routing Routing topology (topology information) Utilization of specific resource These classification is not mutually exclusive
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Based on the Routing Information Update Mechanism
Proactive or table-driven routing protocols Maintain routing information in the routing table Routing information is flooded in the whole network Runs path-finding algorithm with the routing table Reactive or on-demand routing protocols Obtain the necessary path while required Hybrid routing protocols In the zone of given node : use table-driven Out of the zone of given node : use on-demand
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Based on the Use of Temporal Information for Routing
Using past temporal information Past status of the links or the status of links at the time of routing to make routing decision Using future temporal information Expected future status of the links to make decision Node lifetime is also included Ex: remaining battery charge, prediction of location, and link availability
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
10
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Based on the Routing Topology
Flat topology routing protocols Flat addressing scheme similar to IEEE 802.3 LANs Globally unique addressing mechanism for nodes Hierarchical topology routing protocols Logical hierarchy Associated addressing scheme May based on geographical information or hop distance
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
11
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Based on the Utilization of Specific Resource
Power-aware routing Minimize consumption of resource Ex: Battery power Geographical information assisted routing Improve the routing performance Reduce control overhead
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
12
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Classifications of Routing Protocol:
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
13
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Hierarchical Routing Protocols
Using routing hierarchy. Reducing the size of routing table. Having better scalability.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
14
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Hierarchical State Routing Protocol (HSR)
HSR operates by classifying different levels of clusters. Elected leaders at every level from the members at the immediate higher level. The physical clustering is done among the nodes that are reachable in a single wireless hop. Nodes are classified as Cluster leaders Gateway nodes belonging to multiple clusters Normal member nodes
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
15
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Example of HSR multi-level clustering
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
16
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Hierarchical State Routing Protocol (HSR)
Cluster leaders must be responsible for slot/frequency/code allocation call admission control scheduling of packet transmissions exchange of routing information handling route breaks Every node maintains information about neighbors and link states to each of them. This information is broadcast within the cluster at regular intervals. The clustering is done recursively to the higher levels At any level, the cluster leaders exchange topology information with its peers. After obtaining information from its peers, it floods the information to the lower levels.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
17
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Hierarchical State Routing Protocol (HSR)
Hierarchical addressing can help in operation with reducing routing information exchanges. The storage required is O(n x m) compared to O(nm) that is required for a flat topology link state routing protocol. n is the average number of nodes in a cluster. m is the number of levels. In military applications of ad hoc networks, the hierarchy of routing assumes significance where devices with higher capabilities of communication can act as the cluster leaders.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
18
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Fisheye State Routing Protocol (FSR)
FSR uses the fisheye technique to reduce routing overhead and graphical data. FSR maintains the topology of the network at every node and computes the shortest paths. Periodically, every node exchanges topology information with sequence numbers only with its neighbors. The accuracy decreases with an increase in the distance from the center of the focal point. Scope: the set of nodes that can be reached in a specific numbers of hops.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
19
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Fisheye state routing
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
20
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
An illustration of routing tables in FSR
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
21
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Fisheye State Routing Protocol (FSR)
The frequency of exchanges decrease with an increase in scope. The path information for far-away nodes may be inaccurate. FSR is suitable for large and highly mobile ad hoc wireless networks. The number of hops with each scope level has significant influence on the performance.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
22
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Power-Aware Routing Protocols
In ad hoc networks, the routers are also equally power-constrained just as the nodes are. The use of routing metrics that consider the capabilities of the power source of nodes contributes to efficient utilization of energy and increases the lifetime of the networks.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
23
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Power-Aware Routing Metrics
Minimal Energy Consumption per Packet Minimize the power consumed by a packet in traversing from the source node to the destination node Maximize Network Connectivity Balance the routing load among the cut-set Minimum Variance in Node Power Levels Distribute the load among all nodes in the network Remain uniform power consumption pattern across all nodes Minimum Cost per Packet Maximize the life of every node in the network Minimize Maximum Node Cost Minimize the maximum cost per node for a packet after routing a number of packets or after a specific period
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
24
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Multicast Routing In Ad Hoc wireless networks
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
25
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Introduction
Multicast routing
Communication among a given set of nodes Better than multiple unicast
Multicast routing in wired network
DVMRP, MOSPF, CBT, PIM Establish a routing tree for a multicast session Packets are sent to all nodes in the tree Not appropriate for ad hoc, why?
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
26
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Constraints in Ad Hoc
Dynamically changing topology Low bandwidth Less reliable links
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
27
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Issues
Challenges
Limited bandwidth Error-prone shared broadcast channel Mobility of nodes Limited energy Hidden terminal problem Limited security
Targets
Robustness Efficiency QoS
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
28
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Classification of Multicast routing protocols
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
29
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree Based Bandwidth efficient multicast protocol
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
30
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree initialization Phase
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
31
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
R3 floods Join control packet
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
32
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
S,I1,R2 sends back reply
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
33
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
R3 join the Group through the nearest forwarding node (I1)
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
34
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree Maintenance Phase
Broadcast-multicast scheme
Upstream node floods broadcast-multicast packet Isolated node receives this packet and rejoin the group
Local rejoin scheme
Isolated node floods Join control packet Upstream nodes send back reply packet Isolated node receives this reply and rejoin the group
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
35
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Broadcast-multicast scheme
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
36
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Broadcast-multicast scheme
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
37
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Rout Optimization phase
Prune unwanted tree nodes By Quit message
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
38
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Advantages and Disadvantages
Advantages
Bandwidth efficient
Disadvantages
Long distance between source and receiver High probability of path breaks High delay
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
39
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Multicast Zone Routing Protocol (MZRP)
Abstract
Each node is associated with a routing zone Attempt to combine on-demand and table-driven routing Two phases
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
40
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree Initialization Phase
Create a multicast delivery tree Two-stage process
Multicast tree creation inside a zone
Tree-Create message Tree-Create-ACK message
Multicast tree extension
Tree-Propagate
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
41
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Multicast tree creation inside a zone
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
42
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Multicast tree extension
Border node unicasts a TREECREATE-ACK to the multicast source to create a link between the border node and the source This sequence continues until every node in the network receives a TREE-CREATE message Routes in MZR are updated through the use of TREEREFRESH packets If a node on the multicast tree fails to receive a TREEREFRESH message after a certain time, it deletes its multicast entry TREE-REFRESH packets could be piggybacked on multicast data whenever possible
MZR creates a source specific, on-demand multicast tree with a minimal amount of routing overhead Hierarchical approach of MZR does not conserve bandwidth during the initial TREE-CREATE flood
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
43
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree Maintenance Phase
Source node send the Tree-Refresh packet periodically If tree node does not receive this packet for a special period, it is isolated Downstream nodes are responsible for rejoining the group (similar to local rejoin scheme)
Join packet JoinAck packet
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
44
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Advantages and Disadvantages
Advantages
Reduce control overhead because it runs over Zone routing protocol
Disadvantages
Long wait for the far node because of the TreePropagate message
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
45
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Multicast tree maintenance in MZRP
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
46
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
The Join Protocol
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
47
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Multicast Core-Extraction Distributed Ad Hoc Routing (MCEDAR)
Abstract
Use the underlying infrastructure mgraph fro forwarding packets Form the minimum dominating set (MDS) with core nodes Node who wants to join a group sends a JoinReq packet Node join the group by receiving JoinAck packet While isolated, node issues a JoinReq again
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
48
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Join protocol
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
49
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Decoupling of control and data paths
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
50
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Advantages and Disadvantages
Advantages
Robust As efficient as other Tree-Based protocols
Disadvantages
Complex Increasing control overhead
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
51
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Associativity based as hoc multicast routing (ABAM)
Tree Initialization Phase
Source node initiate the multicast tree construction phase. Joining a group achieved by Three process
Flooding by the source Replies along the stable path by the receivers Path setup by the source
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
52
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Associativity based as hoc multicast routing (ABAM)
This is an on-demand source-initiated multicast routing protocol A multicast tree is built for each multicast group based on association stability The link status of each node is monitored by its neighbors ABAM deals with the network mobility on different levels according to varying mobility effects: branch repair when the receiver moves, sub-tree repair when a branching node moves, and full tree level repair when the source node moves
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
53
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree Initialization Phase Cntd
Source broadcast the multicast Query (MBQ) packet. The intermediate node appends the ID with QoS information. The destination replies with MBQ Reply packet. The source sends MC-Setup packets to all receivers to establish the multicast tree
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
54
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
55
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree maintenance phase
Due to movement the link failure occurs ABAM procedure to maintain and repair the multicast tree.
If the node move to another location, new route is established by sending LocalQuery packet. Once the LocalQuery packet is received then it replies by sending LocalQuery-reply.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
56
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Advantages and Disadvantages
The path between source and destination is stable when compared to other protocols.
High packet delivery ratio
Control packet overhead is less due to fewer link failure. Increase hop count between sender and receiver.
Results in congestion Increase in delay Low Packet delivery ration Not scalable for scalability load balancing is needed
57
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Differential destination multicast routing protocol
Maintain distributed group membership management and distributed multicast routing state maintenance policies. Stateless multicasting avoids maintaining multicast states in the nodes. Applicable for small group size.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
58
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree initialization Phase
To join a particular multicast session
Interested destination node unicasts a join control packet to the source. Source receives join packet
Checks for validity and sends an ACK control packet to the destination. Stores the destination address in its member list (ML). Each destination periodically sends join control packets to the source to show its interest in the multicast session. These join control packets refresh the ML table at the source. The removes the unwanted member if it does not receives any join message.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
59
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree maintenance phase
DDM can operate in both stateless mode and soft state mode. Stateless mode
Straightforward mode
Source inserts the destination address in the field called DDM block. The inter node forwards to next hop by checking the DDM block.
Soft state mode
Each node along the forwarding path remembers the destination node by storing it in the forwarding set. When change occurs the upstream node inform to downstream node about the difference through a D-type DDM block.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
60
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Advantages and disadvantages
DDM does not maintain the multicast state
It uses minimum memory source
Centralized admission policy security is assured. Automatic rerouting is possible if the node changes the location. Scalability is not assured for large networks. DDM involves in periodic control packets
Results in consuming more bandwidth
Hence DDM suitable for small group size.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
61
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Weighted based multicast (WBM) protocol
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
62
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Weighted based multicast (WBM) protocol
Protocol follows the weight when deciding upon the entry point in the multicast group. Node checks for the distance between source and destination in the multicast tree. It provides flexibility for a receiver to join wither the nearest node in the multicast tree.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
63
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree initialization phase
A node desires to join the multicast group. The aim here is to find the best point of entry into the multicast group. The approach we have taken for this is a receiver-initiated approach. When a new receiver R5 decides to join the group, it broadcasts a JoinReq packet with a certain time to live(TTL) entry. These JoinReq packets are forward until they are received by a tree node. Upon receiving a JoinReq packet, a tree node say I1, send a Replay packet.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
64
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cntd
The Replay packet initially contains the distance of the node I1 from the source S. Upon the reply packet receipt at node R5 will have the hop distance of the node R5 from node I1 and the hop distance of node I from the source S.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
65
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cntd.
The best replay minimizes the following quantity:
Q = (1-joinWeight)* ((hop distance of R5 from I1)-1)
+
joinWeight* (*(hop distance of R5 from I1 + hop distance of I1 from S)
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
66
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree Maintenance Phase
Tree maintenance phase is executed for TriggerHandoff time period before the link is expected to break. The triggerHandoff is the time duration after which the downstream tree node starts the handoff procedure to reconfigure the multicast tree before the link breaks(link between downstream node and its parent node).
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
67
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree Maintenance Phase
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
68
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cntd
In this scheme, each node maintains a Neighbor Multicast Tree table(NMT). A node refreshes the NMTExistence timer when it receives data packets from tree node.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
69
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cntd
When the downstream tree node receives data packets from its parent node, the node can predict the time duration for which the parent node would remain within its transmission range. After receiving the data packets if the link life period is less than the TriggerHandoff time period , then the downstream node transmits the data packet after setting InitiateHandoff bit.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
70
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cntd
When a neighbor node promiscuously receives a data packet with InitateHandoff bit set,it sends Handoff control packet if the following two conditions are satisfied. 1.the neighbor node has tree node inforation for that particular multicast group in NMT table. 2.the NodeDistance value of the corresponding tree node entry in NMT be less than the distance of the node which requests for handoff procedure.
If the above two conditions are satisfied , then the neighbor node sends Handoff control packet to the interested tree node.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
71
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cntd
When the tree node receives many Handoff control packets,it chooses the Handoff control packet with least NodeDistance value and immediately sends back a HandoffConf control packet to the neighbor node. After receiving the HandoffConf control packet,the neighbor node forwards it to the tree node to rejoin the multicast tree. There may be more than one neighbor which satisfy the above two conditions. They are also eligible to send Handoff control packets to the interested tree node to reconfigure the multicast tree. Due to this reason, there is a chance that these Handoff packets collide and not reach the destination node.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
72
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cntd
Sending Handoff control packets by many neighbor nodes may lead to increased control overhead. If any neighbor node hears a HandoffConf control packet,just before sending the Handoff control packet,then it discards its Handoff control packet. There is no neighbor node satisfying the two conditions. Hence the downstream node in this case does not get any Handoff control packet from any neighbor nod,resulting in a link break. When such a situation arises, the downstream node of the broken link has to take measures to rejoin the multicast group.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
73
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cntd
To find the new route to any forwarding node in the multicast tree, the downstream node floods JoinReq with certain TTL value.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
74
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Advantages and disadvantages
Decision taken by newly joining node maintain the balance in number of additional nodes to be added to the existing multicast tree. Hop distance to the source node result in high efficiency. The prediction based preventive route repair mechanism avoids path breaks. Disadvantages
Localized prediction scheme may not work consistently. Probability of prediction may not be accurate. Resulting in unnecessary handoff. joinWeight parameters depends on several factors such as network load and the size of the multicast grouping.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
75
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Preferred link based multicast protocol (PLBM)
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
76
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Preferred link based multicast protocol
Uses a preferred link approach for forwarding joinQuerry packets. The main concept is selection of a set of selection links to neighbor nodes called preferred links and the use of only those links for forwarding to joinQuerry packets.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
77
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree Initialization Phase
Tree base receiver initiated protocol. Each node maintains the two neighbor topology information and multicast tree in two tables
Neighbors neighbors table (NNT) Connect table (CT)
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
78
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cntd
Every node send a beacon periodically. On receiving of beacon the information is updated in NNT. If new node need to connect
it will check for the NNT list If so node sends joinconfirm packet. If not node sends joinQuery packet.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
79
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cntd
The first K eligible nodes from the NNT care called preferred nodes. Only these nodes are eligible for further processing of the received joinQuery packets. The JoinQuery packets then send as a unicast packets to the preferred nodes.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
80
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cntd
On receiving
Check its eligibility for forwarding packets If not it discards packet. If yes node is connected to multicast tree
Sends back joinreply(JR) packets to the node that originated the joinQuery(JQ) packets. Otherwise it forwards JQ using the same procedure as above. JR packet follows the route by JQ packet in reverse order. Any proceeded JR identified through the multicast group ID , multicast source ID, and sequence number fields on the packet is discarded. The unprocessed JR packets are forwarded.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
81
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cntd
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
82
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree maintenance phase
Link break can detected in two ways
Detect by not receiving the beacon (TckBcon) TckBcon selection period is important.
If it is too long then the link break period is delayed. Resulting in loss of data packets. If it is too short it results in detection of false link breaks.
Other mechanism is based on RTS-CTS control packets.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
83
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Advantages and Disadvantages
Advantages
Uses two-hop local topology information for efficient multicast routing. Provides better flexibility and adaptability
Disadvantages
Uses periodic beacons
Significant control overhead.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
84
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Multicast Ad Hoc On Demand Distance Vector Routing
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
85
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
MAODV Advantages
Discovers Multicast routes on demand and purposely used by mobile nodes in an ad hoc network. It offers quick adaptation to dynamic link conditions, low processing and memory overhead and low network utilization. Moreover, MAODV creates bi-directional shared multicast trees connecting multicast sources and receivers.
Can move forward or backward or duplex communication system where a system composed of two connected parties or devices that can communicate with one another in both directions.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
86
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Intro to its Messages
Exploits four types of messages. The Route Requests (RREQs) Route Replies (RREPs) Multicast Activation (MACTs) Group Hellos (GRPHs)
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
87
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Sending a RREQ
o Consult its Group Leader Table, based on entry o Set J if node wishes to join the multicast group o If nodes not know leader, Dest. address = Address of Multicast Group & broadcast RREQ without MGLEx o If nodes knows leader, place group leaders address in MGLEx & unicast to next hop to the destination
MGLEx = Multicast Group Leader Extension
= Node issuing request to join
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
88
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Receiving a RREQ
o Node checks J flag, if set o Node can only respond if it is a member of Multicast tree of MG or nodes MGSN > MGSN in RREQ o If J flag not set o Node can only respond if it has unexpired route to MG and nodes MGSN > MGSN in RREQ
MGL = Multicast Group Leader Node issuing request to join
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
89
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Waiting for a RREP
o Node waits for RREP o May resend RREQ up to RREQ_RETRIES additional times o If no RREP within RREP_WAIT_TIME of unicast RREQ to leader, node broadcast subsequent RREQs for MG. o If RREP not received after RREQ_RETRIES, assume no other members in group , so it then becomes MGL (if wanting to join group) or drop packet and abort session.
MGL = Multicast Group Leader Node issuing request to join
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
90
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Control Route Request Broadcast
Prevent unnecessary broadcast of RREQs
Source node use expanding ring search technique
After RREP received, Hop Count to group leader in RREP packet is remembered as the Last Hop Count, LHC in that nodes routing table When require new route to this Multicast Group, RREQ IP headers TTL = initially set to LHC + TTL_INCREMENT Thus, TTL incremented by TTL_INCREMENT until TTL_THRESHOLD reached.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
91
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Brief Summary Operation of MAODV
http://code.google.com/p/typecast-routing/wiki/MAODVOverView
The core of the MAODV protocol is about how to form the tree, repair the tree when a link is broken, and how to merge two previously disconnected tree into a new tree. All members of a multicast group are formed into a tree The root of the tree is the group leader. Multicast data packets are propagated among the tree. There are four types of packets in MAODV: RREQ, RREP, MACT and GRPH.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
92
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
o A node broadcasts a RREQ when o it is a member node and want to join the tree o it is a non-member node and has a data packet targeted to the group. o When a node in the tree received RREQ, it responses with RREP using unicast. o Since RREQ is broadcasted, there may be multiple RREPs received by the originating node. o The originating node should select one RREP that has the shortest distance to the tree and unicast a MCAT along the path to set up a new branch to the tree. o GRPH is the group hello packet, it is periodically broadcasted by group leader to let the nodes in the tree to update its distance to the group leader.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
93
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Parameter Metrics
1. Packet Delivery Ratio: The fraction of packets sent by the multicast application that are received by the multicast receivers. 2. Control Packet Overhead: The total number of control packets originated and forwarded by the protocol. 3. Normalized Packet Overhead: The number of control and data
transmissions performed by the protocol per successfully delivered data
packet. 4. End-To-End Delay: The time between the transmission of a data packet from a multicast source and the time of its reception by a multicast receiver, averaged over all packets.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
94
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Ad hoc multicast routing protocol utilizing increasing ID-numbers
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
95
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
AMRIS
AMRIS is an on-demand protocol which constructs a shared delivery tree to support multiple senders and receivers within a multicast session. The key idea that differentiates AMRIS from other multicast routing protocols is that each participant in the multicast session has a session-specific multicast session member id (herein known as msm-id).
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
96
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree Initialization Phase
Tree initialization begins with Sid broadcasting a NEWSESSION message to its neighbours. The NEW-SESSION will contain, among other things, Sid's msm-id, multicast session id, and routing metrics. All nodes that receive the NEWSESSION message generate their own msm-id by computing a value that is larger and not consecutive. A receiver then replaces the msm-id in the message with their own, as well as various routing metrics, before broadcasting the message again.
Information derived from the NEWSESSION message is kept in the Neighbour-Status table for up to T1 seconds.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
97
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cntd
A random jitter is introduced between the receipt of a NEW-SESSION message and its subsequent rebroadcast to prevent broadcast storms. A node may receive multiple NEW-SESSION messages from different nodes. If it has not rebroadcast any messages yet, it will keep the message that has the best routing metrics and calculate its msm-id based on the values from that message. Otherwise the messages received are dropped
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
98
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Tree Maintenance Phase
The tree maintenance mechanism operates continuously in the background to ensure that a node remains connected to the multicast session delivery tree. When a link between two nodes breaks, the node with the larger msm-id (a.k.a. the child node) is responsible for rejoining. A node attempts to rejoin the tree by executing the Branch Reconstruction (BR), which has two main subroutines, BR1 and BR2. BR1 is executed when the node has neighboring potential parent nodes that it can attempt to join to; BR2 is executed when the node does not have any neighboring nodes that can be potential parents
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
99
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Advantages and Disadvantages
Advantages AMRIS uses MSM-ID so it avoids loop formation and link breaks are repaired locally.
Hence the control overhead is less.
AMRIS is Simple when compare to other multicast protocols. Disadvantages Wastage of bandwidth
Due to beacons Collision with beacons
Hard state maintenance scheme
Node cut off due to path breaks. End to end delay.
Increase the hop length between source as receivers.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
100
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Adaptive shared tree multicast routing protocol
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
101
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Shared tree multicast protocol
Chosen to provide low overhead and adequate stability in the presence of fast moving source. Supports many-to-many casting, with several senders and receivers. The source tree is rooted at the source node, whereas a shared tree is rooted at the rendezvous point (RP) and it shared by multiple source.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
102
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cntd
Unicast sender mode
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
103
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cntd
Sender doesn't know all the receiver address It only knows the RP address. Send the packet to the group by encapsulating it and unicast to RP. The RP will forward to all the receive members.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
104
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Multicast sender mode
In unicast mode the packet travels directly to the RP and then to the members.
In the middle of transmission the packet cannot be intercept because the multicast address is hidden. The bandwidth efficiency can be increased by allowing the receiver to receive the data packets directly from the source.
In the case of packet traverse through RP a path which is much longer than the shortest path between source and receiver.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
105
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
106
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
107
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
108
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
109
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Advantages and disadvantages
Advantages Due to adaptive nature of the tree configuration
Scalable. High packet delivery ratio. Control overhead is reduced due to shared tree It allows source to send packets to receivers by shortest path, resulting in better throughput.
Disadvantages Similar to other shared tree based protocols, this scheme also carries with it the risk of single point failure of the RP.
Results in significant packet loss
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
110
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Transport Layer and Security Protocols for Ad Hoc Wireless Networks
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
111
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Chapter 9: Transport Layer and Security Protocols for Ad Hoc Wireless Networks
Introduction Issues Design Goals Classifications TCP Over Ad Hoc Wireless Networks Other Transport Layer Protocols
112 Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
Security in Ad Hoc Wireless Networks Network Security Requirements Issues and challenges in security Network security attacks Key Management Secure Routing
112
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Introduction
The objectives of a transport layer protocol include setting up of:
End-to-end connection End-to-end delivery of data packets Flow control Congestion control
Transport layer protocols
User datagram protocol (UDP): unreliable and connection-less transport layer protocols Transmission control protocol (TCP): reliable, byte-streambased, and connection-oriented transport layer protocols
These traditional wired transport layer protocols are not suitable for ad hoc wireless networks.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
113
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Issues
Issues while designing a transport layer protocol for ad hoc wireless networks:
Induced traffic refers to the traffic at any given link due to the relay traffic through neighboring links. Induced throughput unfairness refers to the throughput unfairness at the transport layer due to the throughput/delay unfairness existing at the lower layers such as the network and MAC layers. Separation of congestion control, reliability, and flow control could improve the performance of the transport layer. Power and bandwidth constraints affects the performance of a transport layer protocol. Misinterpretation of congestion occurs in ad hoc wireless networks. Completely decoupled transport layer needs to adapt to the changing network environment. Dynamic topology affects the performance of a transport layer.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
114
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Design Goal
The protocol should maximize the throughput per connection. It should provide throughout fairness across contending flows. It should minimize connection setup and connection maintenance overheads. The protocol should have mechanisms for congestion control and flow control in the network. It should be able to provide both reliable and unreliable connections. The protocol should be able to adapt to the dynamics of the network. One of the important resources must be used efficiently. The protocol should be aware of resource constraints. The protocol should make use of information from the lower layer. It should have a well-defined cross-layer interaction framework. The protocol should maintain end-to-end semantics.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
115
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Classification of Transport Layer Solutions
Transport Layer Solutions for Ad Hoc Wireless Networks Other transport layer approach ACTP ATP Split Approach End-to-end approach TCP-ELFN TCP-F TCP-Bus ATCP
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
TCP over ad hoc wireless networks
Split-TCP
116
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
TCP over Ad Hoc Wireless Networks
TCP taking 90% of the traffic is predominant in the Internet. This chapter focuses on TCP extension in ad hoc wireless networks. Transport protocol should be independent of the network layer technology, e.g., no matter fiber or radio is used But TCP is optimized for wired network Congestion control
TCP assumes timeout is due to congestion Wireless links are not reliable, packet loss may be as high as 20% In wired network, packet loss is due to congestion slow down In wireless network, due to wireless links try harder
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
117
CS9263 AD-HOC NETWORKS
Why does TCP not perform well in Ad Hoc Wireless Networks
Vishnu Kumar Kaliappan
Misinterpretation of packet loss Frequent path breaks Effect of path length Misinterpretation of congestion window Asymmetric link behavior Uni-directional path: TCP ACK requires RTS-CTSData-ACK exchange Multipath routing Network partitioning and remerging The use of sliding-window-based transmission
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
118
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
TCP Over Ad Hoc Wireless Network
Feedback-based TCP (TCP Feedback TCP-F)
Requires the support of a reliable link layer and a routing protocol that can provide feedback to the TCP sender about the path breaks. The routing protocol is expected to repair the broken path within a reasonable time period. Advantages: Simple, permits the TCP congestion control mechanism to respond to congestion Disadvantages:
If a route to the sender is not available at the failure point (FP), then additional control packets may need to be generated for routing the route failure notification (RFN) packet. Requires modification to the existing TCP. The congestion window after a new route is obtained may not reflect the achievable transmission rate acceptable to the network and the TCP-F receiver.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
119
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
TCP Over Ad Hoc Wireless Network
TCP with explicit link failure notification (TCPELFN)
Handle explicit link failure notification Use TCP probe packets for detecting the route reestablishment. The ELFN is originated by the node detecting a path break upon detection of a link failure to the TCP sender. Advantages:
improves the TCP performance by decoupling the path break information from the congestion information by the use of ELFN. Less dependent on the routing protocol and requires only link failure notification
Disadvantages
When the network is partitioned, the path failure may last longer The congestion window after a new route is obtained may not reflect the achievable transmission rate acceptable to the network and TCP receiver.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
120
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
TCP Over Ad Hoc Wireless Network
TCP with buffering capability and sequence information (TCP-BuS)
Use feedback information from an intermediate node on detection of a path break. Use localized query (LQ) and REPLY to find a partial path Upon detection of a path break, an upstream intermediate node originates an explicit route disconnection notification (ERDN) message. Advantages Disadvantages
Performance improvement and avoidance of fast retransmission Use on-demand routing protocol
Increased dependency on the routing protocol and the buffering at the intermediate nodes The failure of intermediate nodes may lead to loss of packets. The dependency of TCP-BuS on the routing protocol many degrade its performance.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
121
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
TCP Over Ad Hoc Wireless Network
Ad Hoc TCP (ATCP)
uses a network layer feedback mechanism to make the TCP sender aware of the status of the network path Based on the feedback information received from the intermediate nodes, the TCP sender changes its state to the persist state, congestion control state, or the retransmit state. When an intermediate node finds that the network is partitioned, then the TCP sender state is changed to the persist state. The ATCP layer makes use of the explicit congestion notification (ECN) for maintenance for the states. Advantages Disadvantages
Maintain the end-to-end semantics of TCP Compatible with traditional TCP Provides a feasible and efficient solution to improve throughput of TCP
The dependency on the network layer protocol to detect the route changes and partitions The addition of a thin ATCP layer to the TCP/IP protocol changes the interface functions currently being used.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
122
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
TCP Over Ad Hoc Wireless Network
Split-TCP
provides a unique solution to the channel fairness problem by splitting the transport layer objectives into congestion control and end-to-end reliability. Splits a long TCP connection into a set of short concatenated TCP connections with a number of selected intermediate nodes as terminating points of these short connections. Advantages
Improved throughput Improved throughput fairness Lessened impact of mobility
Disadvantages
It requires modifications to TCP protocol. The end-to-end connection handling of traditional TCP is violated. The failure of proxy nodes can lead to throughput degradation.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
123
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Table-Driven Routing Protocols On-Demand Routing Protocols Hybrid Routing Protocols Routing Protocol With Efficient Flooding Mechanisms Hierarchical Routing Protocols Power-Aware Routing Protocols
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
124
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Table-Driven Routing Protocols
We introduce these routing protocols: Destination Sequenced Distance-Vector Routing Protocol (DSDV) Wireless Routing Protocol (WRP) Cluster-Head Gateway Switch Routing Protocol (CGSR) Cluster-Head Gateway Switch Routing Protocol (CGSR) Source-Tree Adaptive Routing Protocol (STAR)
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
125
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Destination Sequenced DistanceVector Routing Protocol (DSDV)
Enhanced from distributed Bellman-Ford algorithm Obtain a table that contains shortest path from this node to every node Incorporate table updates with increasing sequence number tags Prevent loops Counter the count-to-infinity problem Faster convergence
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
126
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
DSDV (Cont.)
Exchange table between neighbors at regular time interval Two types of table updates Incremental update Takes a single network data packet unit (NDPU) When no significant change in the local topology Full dumps update Takes multiple NDPUs: When local topology changes significantly Or incremental updates require more than a NDPU
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
127
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
DSDV (Cont.)
Table updates are initiated by the destination with the new sequence number which is always greater than the previous one Single link break cause propagation of table update information to the whole network With odd sequence The changed node informs neighbors about new shortest path while receiving the table update message With even sequence
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
128
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Routing Establishment in DSDV
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
129
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Route maintenance in DSDV
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
130
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
DSDV (Cont.)
Advantages: Route setup process is very fast Make the existing wired network protocol apply to ad hoc network with fewer modifications Disadvantages: Excessive control overhead during high mobility Node must wait for a table update message initiated by the destination node Cause stale routing information at nodes
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
131
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Wireless Routing Protocol (WRP)
Similar to DSDV, but it uses multiple tables for routing processes Differs from table maintenance and in the update procedure Uses a set of tables to maintain more accurate information instead of single topology information Not only updates distance for transmitted neighbor but also checks the other neighbors distance
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
132
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Wireless Routing Protocol (WRP)
Distance table Contains distance and predecessor node for a destination Routing table Contains shortest distance, predecessor node, successor node, and status of the path Link cost table Cost of relaying messages through each link Number of update periods passed since the last successful update was received (for detecting link breaks) Message retransmission table Update message that is to be retransmitted with a counter Counter decremented after every update message retransmission
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
133
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Route establishment in WRP
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
134
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Route maintenance in WRP
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
135
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Wireless Routing Protocol (WRP)
Advantages: Same as DSDV Has faster convergence and fewer table updates Disadvantages: Need large memory and greater computing power because of the multiple tables At high mobility, the control overhead for updating table entries is almost the same as DSDV Not suitable for highly dynamic and large ad hoc network
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
136
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cluster-Head Gateway Switch Routing Protocol (CGSR)
Hierarchical topology based on cluster Cluster-head is elected by a Least Cluster Change (LCC) algorithm Clustering uses CDMA to allocate bandwidth between different clusters Every cluster has its own spreading code Cluster-head coordinate channel access based on token-based polling protocol Cluster-head can reach all member nodes within a single hop
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
137
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cluster-Head Gateway Switch Routing Protocol (CGSR)
Communication passes through the cluster-head Gateway: a member in more than one clusters Listens to multiple spreading codes Becomes a bridge between cluster Becomes a bridge between cluster Gateways are capable of simultaneously communicating over two interfaces can avoid conflict Performance is influenced by: Token scheduling for cluster-head Code scheduling for gateway
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
138
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cluster-Head Gateway Switch Routing Protocol (CGSR)
Routing in CGSR is an extension of DSDV Each node maintains a routing table containing Destination cluster-head for every node The list of next-hop nodes for reaching destination cluster Route reconfiguration is necessitated by two actor: Cluster-head changes Stale entries in the cluster member table and routing table
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
139
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Route establishment in CGSR
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
140
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Cluster-Head Gateway Switch Routing Protocol (CGSR)
Advantages: Better bandwidth utilization Easy to implement priority scheduling scheme Disadvantages: Increase in path length Instability when cluster-head are high mobility Battery-draining rate at cluster-head is more than a normal node Frequent changes in the cluster-head = multiple path break
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
141
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Table-Driven Routing Protocols On-Demand Routing Protocols Hybrid Routing Protocols Routing Protocol With Efficient Flooding Mechanisms Hierarchical Routing Protocols Power-Aware Routing Protocols Summery
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
142
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
On-demand Routing Protocol
Unlike the table-driven routing protocols, ondemand routing protocols execute the path finding process and exchange routing information only when a path is required by a node to communicate with a destination.
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
143
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
On-demand Routing Protocol
Dynamic Source Routing Protocol (DSR) Ad Hoc On-demand Distance-Vector Routing Protocol (AODV) Temporally Ordered Algorithm (TORA) Location-Aided Routing (LAR) Location-Aided Routing (LAR) Associativity-Based Routing(ABR) Signal Stability-Based Adaptive Routing Protocol (SSA) Flow-Oriented Routing Protocol (FORP)
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
144
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Dynamic Source Routing Protocol (DSR)
Beacon-less: no hello packet Routing cache DSR contains two phases Route Discovery (find a path) Flooding Route Request with TTL from source Response Route Reply by destination If an forwarding node has a route to the destination in its route cache, it sends a Route Reply to the source Route Maintenance (maintain a path) Route Error
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
145
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Route establishment in DSR
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
146
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Route maintenance in DSR
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
147
CS9263 AD-HOC NETWORKS
Vishnu Kumar Kaliappan
Ref: C.Siva Ram Murthy and B.Smanoj, Ad Hoc Wireless Networks Architectures and Protocols, Pearson Education, 2004.
148
También podría gustarte
- Kpit Autosar HandbookDocumento74 páginasKpit Autosar HandbookBogdan Alin100% (1)
- 5 - LOGIC BANHA G1 p741 PDFDocumento1622 páginas5 - LOGIC BANHA G1 p741 PDFsmart_eng2009100% (2)
- Energy Management in Wireless Sensor NetworksDe EverandEnergy Management in Wireless Sensor NetworksCalificación: 4 de 5 estrellas4/5 (1)
- Optically Amplified WDM NetworksDe EverandOptically Amplified WDM NetworksJohn ZyskindAún no hay calificaciones
- Radwin R-Planner Faq Rev2.3Documento6 páginasRadwin R-Planner Faq Rev2.3marcorubinap100% (2)
- Cognitive Radio Wireless NetworksDocumento24 páginasCognitive Radio Wireless NetworksSaquib MazharAún no hay calificaciones
- Flow Networks: Analysis and Optimization of Repairable Flow Networks, Networks with Disturbed Flows, Static Flow Networks and Reliability NetworksDe EverandFlow Networks: Analysis and Optimization of Repairable Flow Networks, Networks with Disturbed Flows, Static Flow Networks and Reliability NetworksCalificación: 5 de 5 estrellas5/5 (2)
- Ad-Hoc Mac: Class - 1Documento69 páginasAd-Hoc Mac: Class - 1Vishnu KumarAún no hay calificaciones
- Routing ProtocolsDocumento20 páginasRouting ProtocolsShachi P GowdaAún no hay calificaciones
- Routing Protocols For AD-Hoc Wireless NetworksDocumento20 páginasRouting Protocols For AD-Hoc Wireless NetworksShachi P GowdaAún no hay calificaciones
- Issues in Ad Hoc Wireless NetworksDocumento25 páginasIssues in Ad Hoc Wireless NetworksRaja MadhuvanthiAún no hay calificaciones
- Ad-Hoc Network Routing & TCP IssuesDocumento84 páginasAd-Hoc Network Routing & TCP Issuespratik16892Aún no hay calificaciones
- Manet Ganz w1Documento163 páginasManet Ganz w1Khuất Duy DuyAún no hay calificaciones
- Manet Ganz w1Documento163 páginasManet Ganz w1gmpraveenkAún no hay calificaciones
- Chapter 2Documento37 páginasChapter 2Ravi TejaAún no hay calificaciones
- Chapter 2Documento37 páginasChapter 2Ravi TejaAún no hay calificaciones
- Routing Protocols To Mitigate Congestion in WSN2003Documento24 páginasRouting Protocols To Mitigate Congestion in WSN2003Neha R KrishnaAún no hay calificaciones
- Chapter 3 - Intro To Dynamic Routing ProtocolsDocumento22 páginasChapter 3 - Intro To Dynamic Routing ProtocolsMukayev DarkhanAún no hay calificaciones
- Ad Hoc Wireless NetworksDocumento16 páginasAd Hoc Wireless Networksanilshaw27Aún no hay calificaciones
- Ijnsa 050301Documento8 páginasIjnsa 050301AIRCC - IJNSAAún no hay calificaciones
- 4.1 Issues in Designing A Routing ProtocolDocumento31 páginas4.1 Issues in Designing A Routing ProtocolLikhi HossainAún no hay calificaciones
- RoutingDocumento26 páginasRoutingimen kriaaAún no hay calificaciones
- A Feedback Based Scheme For Improving TCP Performance in Ad-Hoc Wireless NetworksDocumento7 páginasA Feedback Based Scheme For Improving TCP Performance in Ad-Hoc Wireless NetworksHarish GokulAún no hay calificaciones
- A Cluster-Based Approach For Routing in Dynamic NetworksDocumento16 páginasA Cluster-Based Approach For Routing in Dynamic Networksyujay.w.linAún no hay calificaciones
- Group A CN Assignment 3Documento13 páginasGroup A CN Assignment 3Usama RaheemAún no hay calificaciones
- Issues in Ad Hoc Wireless NetworksDocumento20 páginasIssues in Ad Hoc Wireless NetworksSumeet JainAún no hay calificaciones
- Network On ChipDocumento43 páginasNetwork On ChipVivek GowdaAún no hay calificaciones
- What Is RoutingDocumento13 páginasWhat Is Routingarijitkar0x7Aún no hay calificaciones
- High Primary User Traffic PDFDocumento5 páginasHigh Primary User Traffic PDFTalib AbbasAún no hay calificaciones
- Tim 7 - Routing Protocols For Ad Hoc Wireless Networks PDFDocumento39 páginasTim 7 - Routing Protocols For Ad Hoc Wireless Networks PDFmuktirandyAún no hay calificaciones
- Singh 2017Documento16 páginasSingh 2017Nikhil VaishAún no hay calificaciones
- 04 RoutingDocumento40 páginas04 RoutinggetdevAún no hay calificaciones
- Module 1 - Wireless Adhoc and Sensor NetworksDocumento77 páginasModule 1 - Wireless Adhoc and Sensor Networkspratik16892Aún no hay calificaciones
- Network Troubleshooting - CT046-3-3: RoutingDocumento58 páginasNetwork Troubleshooting - CT046-3-3: RoutingAhamed NashathAún no hay calificaciones
- WSN Routing ProtocolsDocumento77 páginasWSN Routing Protocolsveeru3112Aún no hay calificaciones
- Ad Hoc and Wireless Sensor Networks - Ec8702: Session byDocumento26 páginasAd Hoc and Wireless Sensor Networks - Ec8702: Session byRaja MadhuvanthiAún no hay calificaciones
- 4-G Systems: High Speed Satellite Mobile CommunicationsDocumento20 páginas4-G Systems: High Speed Satellite Mobile CommunicationsJaya SreeAún no hay calificaciones
- Routing Techniques in Wireless Sensor NetworksDocumento107 páginasRouting Techniques in Wireless Sensor NetworksKesav RameshKumarAún no hay calificaciones
- Ad Hoc Wireless RoutingDocumento25 páginasAd Hoc Wireless RoutingPradeep Kumar SuriAún no hay calificaciones
- Data Communication Important TopicsDocumento64 páginasData Communication Important TopicsNagesh BhaviAún no hay calificaciones
- Unit 3Documento54 páginasUnit 3sakshamsharma7257Aún no hay calificaciones
- Autonomously Reconfiguring Failures in Wireless Mesh NetworksDocumento4 páginasAutonomously Reconfiguring Failures in Wireless Mesh NetworksJournal of Computer ApplicationsAún no hay calificaciones
- Secure Communication in Cellular and Ad Hoc EnvironmentsDocumento107 páginasSecure Communication in Cellular and Ad Hoc Environmentsquangphuong1987Aún no hay calificaciones
- Routing Protocols For Wireless Sensor Networks: Murtadha S. Al-SabbaghDocumento34 páginasRouting Protocols For Wireless Sensor Networks: Murtadha S. Al-Sabbaghlok_buzz1Aún no hay calificaciones
- Chapter 2Documento37 páginasChapter 2Antony PandiarajanAún no hay calificaciones
- Adaptive Opportunistic Routing For Wireless Ad Hoc NetworksDocumento44 páginasAdaptive Opportunistic Routing For Wireless Ad Hoc NetworksSaranKumarAún no hay calificaciones
- Đa Phương Tiện Nâng Cao (Advanced Multimedia) : Qos Architectures Supporting MultimediaDocumento34 páginasĐa Phương Tiện Nâng Cao (Advanced Multimedia) : Qos Architectures Supporting MultimediaDuc DuongAún no hay calificaciones
- Model Question Paper - Adhoc NetworksDocumento2 páginasModel Question Paper - Adhoc Networkssuresh viswamAún no hay calificaciones
- IjrsatDocumento4 páginasIjrsatSrikanth ShanmukeshAún no hay calificaciones
- ARIOR: Adaptive Ranking Based Improved Opportunistic Routing in Wireless Sensor NetworksDocumento24 páginasARIOR: Adaptive Ranking Based Improved Opportunistic Routing in Wireless Sensor Networksinformatiquehageryahoo.frAún no hay calificaciones
- Ad Hoc WirelessDocumento25 páginasAd Hoc WirelessABHISHEK TRIPATHIAún no hay calificaciones
- COE 231 540 TransportLayer 6 Shortened 2Documento56 páginasCOE 231 540 TransportLayer 6 Shortened 2Amer AbuObidahAún no hay calificaciones
- Local Area Network OverviewDocumento64 páginasLocal Area Network Overviewapi-19500872Aún no hay calificaciones
- Performance Comparison of Multihop Wireless Mobile Ah-Hoc Routing ProtocolsDocumento8 páginasPerformance Comparison of Multihop Wireless Mobile Ah-Hoc Routing ProtocolsUbiquitous Computing and Communication JournalAún no hay calificaciones
- CA Ex S2M10 Link-State Routing ProtocolDocumento29 páginasCA Ex S2M10 Link-State Routing Protocolhttp://heiserz.com/Aún no hay calificaciones
- Future Generation Computer Systems: Anil Carie Mingchu Li Chang Liu Prakasha Reddy Waseef JamalDocumento8 páginasFuture Generation Computer Systems: Anil Carie Mingchu Li Chang Liu Prakasha Reddy Waseef Jamalvenkata rao RampayAún no hay calificaciones
- 11TEDocumento21 páginas11TEBishwajit ChowdhuryAún no hay calificaciones
- CN BCA6005 - Module - V - NotesDocumento14 páginasCN BCA6005 - Module - V - Notesshatabdi mukherjeeAún no hay calificaciones
- Unit - Iii.Documento87 páginasUnit - Iii.cool dudesAún no hay calificaciones
- Dynamic Backup Routes Routing Protocol For Mobile Ad Hoc NetworksDocumento25 páginasDynamic Backup Routes Routing Protocol For Mobile Ad Hoc NetworksmohhassonaAún no hay calificaciones
- Cooperative Wireless Network: Behnaam AazhangDocumento45 páginasCooperative Wireless Network: Behnaam AazhangAminudin KhalidAún no hay calificaciones
- Ajay RawatDocumento2 páginasAjay Rawatajay_davimAún no hay calificaciones
- Traditional Data Center VDocumento5 páginasTraditional Data Center Vzionne hiladoAún no hay calificaciones
- Hardware AddressingDocumento4 páginasHardware Addressinghassan_m2222Aún no hay calificaciones
- Designing of Hydraulically Balanced Water Distribution Network Based On GIS and EPANETDocumento8 páginasDesigning of Hydraulically Balanced Water Distribution Network Based On GIS and EPANETSolomon ElumaAún no hay calificaciones
- GPLIM #2. VLAN HandbookDocumento31 páginasGPLIM #2. VLAN HandbookDenisAún no hay calificaciones
- Lab 5 Introduction To Packet Tracer and Cisco RouterDocumento26 páginasLab 5 Introduction To Packet Tracer and Cisco RouternoumanAún no hay calificaciones
- Red Hat Network Satellite-5.4-Proxy Installation Guide-En-USDocumento42 páginasRed Hat Network Satellite-5.4-Proxy Installation Guide-En-USEmadElDinEzzatAún no hay calificaciones
- Rsa Securid Access Cloud Authentication Service Quick Setup Radius Clients PDFDocumento16 páginasRsa Securid Access Cloud Authentication Service Quick Setup Radius Clients PDFPepe MartinAún no hay calificaciones
- IBwave Design Release Notes 8.1.2Documento24 páginasIBwave Design Release Notes 8.1.2Sho ShoAún no hay calificaciones
- AzureDocumento58 páginasAzurezeeshankaizerAún no hay calificaciones
- Introduction To Wireless Sensor NetworksDocumento13 páginasIntroduction To Wireless Sensor NetworksJuan Sanchez Alarcon100% (1)
- Complete System SF002 - EN - Webb2011Documento13 páginasComplete System SF002 - EN - Webb2011MAKRONAún no hay calificaciones
- Pro-Watch 55 AE Document Nov 21 2021 800-07601V26 PDFDocumento26 páginasPro-Watch 55 AE Document Nov 21 2021 800-07601V26 PDFthamer al-salekAún no hay calificaciones
- Baja White PaperDocumento10 páginasBaja White PaperJOhn Pual uyAún no hay calificaciones
- L5 - Module - 3 Develop System Infrastructure Design PlanDocumento32 páginasL5 - Module - 3 Develop System Infrastructure Design PlanDo Dothings100% (8)
- Manual Dlan 200 AVplus Liveplug HD enDocumento35 páginasManual Dlan 200 AVplus Liveplug HD endatajerzyAún no hay calificaciones
- FortiGate Rugged SeriesDocumento15 páginasFortiGate Rugged SeriesTRUNG MrAún no hay calificaciones
- Sockets IBMDocumento190 páginasSockets IBMabhijeetnayak100% (1)
- FortiClient v4.0 MR3 Patch 3 Release NotesDocumento11 páginasFortiClient v4.0 MR3 Patch 3 Release Notesjcjcjc1024Aún no hay calificaciones
- System IntegrationDocumento8 páginasSystem IntegrationMaheshSharmaAún no hay calificaciones
- Installation Guide For Omnivista 2500 Nms Enterprise Version 4.2.1.R01Documento51 páginasInstallation Guide For Omnivista 2500 Nms Enterprise Version 4.2.1.R01AadityaIcheAún no hay calificaciones
- CV - Noel Kakhobwe ME Officer PDFDocumento9 páginasCV - Noel Kakhobwe ME Officer PDFNoel Owen KakhobweAún no hay calificaciones
- BT-PON BT-191XR XPON CATV ONU ONT DatasheetDocumento4 páginasBT-PON BT-191XR XPON CATV ONU ONT Datasheetnayux ruizAún no hay calificaciones
- Os8 Specs 88r2 RevADocumento99 páginasOs8 Specs 88r2 RevAAmar HADIDIAún no hay calificaciones
- E65C Cu-Xe: Industrial and CommercialDocumento58 páginasE65C Cu-Xe: Industrial and CommercialAnonymous dH3DIEtzAún no hay calificaciones
- Link 1. Overview: 1.1. Getting StartedDocumento18 páginasLink 1. Overview: 1.1. Getting StartedAnkitAún no hay calificaciones
- ETABS Install InstructionsDocumento2 páginasETABS Install InstructionsAdrian TudoracheAún no hay calificaciones