Documentos de Académico
Documentos de Profesional
Documentos de Cultura
CMGT441 Course Syllabus
Cargado por
Arsalan LariDescripción original:
Título original
Derechos de autor
Formatos disponibles
Compartir este documento
Compartir o incrustar documentos
¿Le pareció útil este documento?
¿Este contenido es inapropiado?
Denunciar este documentoCopyright:
Formatos disponibles
CMGT441 Course Syllabus
Cargado por
Arsalan LariCopyright:
Formatos disponibles
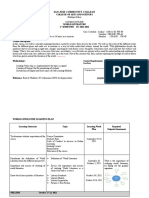
Course Syllabus CMGT/441 Version 2
Course Syllabus
College of Information Systems & Technology CMGT/441 Version 2 Introduction to Information Systems Security Management
Copyright 2010, 2009 by University of Phoenix. All rights reserved.
Course Description This course introduces security principles and management issues that IT professionals must consider. The course surveys current and emerging security practices and processes as they relate to; information system, systems development, operating systems and programming, database development and management, networking and telecommunications, and the Internet. Policies Faculty and students/learners will be held responsible for understanding and adhering to all policies contained within the following two documents: University policies: You must be logged into the student website to view this document. Instructor policies: This document is posted in the Course Materials forum.
University policies are subject to change. Be sure to read the policies at the beginning of each class. Policies may be slightly different depending on the modality in which you attend class. If you have recently changed modalities, read the policies governing your current class modality. Course Materials Stallings, W., & Brown, L. (2008). Computer security principles and practice. Pearson Education, Inc. Article References Barr, J. G. (2011). Business continuity for web sites. Faulkner Information Services, 1-9. Barr, J. G. (2011). Identity management market trends. Faulkner Information Services, 1-10. Spring, K. (2009). IBM tivoli security event management. Faulkner Information Services, 1-9. Barr, J. G. (2009). Common criteria overview. Faulkner Information Services, 1-10. Vosevich, K. A. (2011). Risk management software market trends. Faulkner Information Services, 1-9. Barr, J. G. (2011). Biometrics market trends. Faulkner Information Services, 1-7. All electronic materials are available on the student website.
Week One: IT Security Overview
Details
Objectives 1.1 Recognize the importance of IT security implementation.
Due
Points
Course Syllabus CMGT/441 Version 2
1.2 Identify major security issues associated with physical and operating system security. 1.3 Describe basic advantages and disadvantages among the various security implementations. Course Preparation Read the course description and objectives. Review the Learning Team Toolkit. NOTE: TestOut LabSims are available for this course. See Week One, Course Materials Page. Read Ch. 1, Overview, of Computer Security Principles and Practice. Read Ch. 2, Cryptographic Tools, of Computer Security Principles and Practice. Read Ch. 3, User Authentication, of Computer Security Principles and Practice. Read Ch. 4, Access Control, of Computer Security Principles and Practice. Read Ch. 5, Database Security, of Computer Security Principles and Practice. Read the Week One Read Me First. Read this weeks Electronic Reserve Readings. Participate in class discussion. Respond to weekly discussion questions. DQ #1 DQ #2 Post weekly summary. Complete the Learning Team Charter. The Learning Team project for this course, due in Week Five, is in the form of a Service Request from Riordan Manufacturing. It will be necessary for the Learning Team to access Service Request: SR-rm013, Information Systems Security Review. 05/23/2012 05/26/2012 05/28/2012 2 1 1 1
Readings
Participation Discussion Questions Weekly Summary Learning Team Instructions
Week Two: Computer and Network Security Issues and Considerations
Details
Objectives 2.1 Recognize major elements of network and workstation security. 2.2 Recall methods of securing networks and workstations. 2.3 Give examples of various security methodologies. Read Ch. 6, Intrusion Detection, of Computer Security Principles and Practice. Read Ch. 7, Malicious Software, of Computer Security Principles and Practice.
Due
Points
Readings
Course Syllabus CMGT/441 Version 2
Read Ch. 8, Denial of Service, of Computer Security Principles and Practice. Read Ch. 9, Firewalls and Intrusion Prevention Systems, of Computer Security Principles and Practice. Read Ch. 10, Trusted Computing and Multilevel Security, of Computer Security Principles and Practice. Read the Week Two Read Me First. Read this weeks Electronic Reserve Readings. Participation Discussion Questions Weekly Summary Learning Team Instructions Individual Participate in class discussion. Respond to weekly discussion questions. DQ #3 DQ #4 Post weekly summary. Draft a 2-3 page description of the physical and network security issues and concerns at each Riordan plant. Using various Internet sources, find an article or website on an information security topic that is of interest to you. Prepare a 1-2 page paper evaluating the article or website. Refer to the note on Evaluative Writing below. Evaluative Writingrequires students to take a stand on the quality of the material being evaluated. Provide an introduction, and select various aspects of the article or website. Describe each aspect, providing comments on the usefulness, validity or appropriateness of the article or website. The evaluation should provide details, examples and/or reasons for your viewpoint. 05/30/2012 06/02/2012 06/04/2012 06/04/2012 06/04/2012 2 1 1 1 5 15
Week Three: Data Security Issues and Considerations
Details
Objectives 3.1 Identify components of data security. 3.2 Distinguish the differences among the various data security methodologies. 3.3 Begin to apply data security methodologies in situational cases. Read Ch. 11, Buffer Overflow, of Computer Security Principles and Practice. Read Ch. 12, Software Security, of Computer Security Principles and Practice. Read Ch. 19, Symmetric Encryption and Message Confidentiality, of Computer Security Principles and Practice. Read Ch. 20, Public-key Cryptography and Message Authentication, of Computer Security Principles and Practice. Read the Week Three Read Me First. Read this weeks Electronic Reserve Readings.
Due
Points
Readings
Course Syllabus CMGT/441 Version 2
Participation Discussion Questions Weekly Summary Learning Team Instructions Individual
Participate in class discussion. Respond to weekly discussion questions. DQ #5 DQ #6 Post weekly summary. Draft a 2-3 page description on the data security issues and concerns present at each Riordan plant. Using various Internet sources, find an article or website on attack prevention. Prepare a 2-3 page paper evaluating the article and information provided. 06/06/2012 06/09/2012 06/11/2012 06/11/2012 06/11/2012
2 1 1 1 5 15
Week Four: Web Security Issues and Concerns
Details
Objectives 4.1 Identify components of web security. 4.2 Distinguish the differences among the various web security methodologies. 4.3 Begin to apply web security methodologies in situational cases. Read Ch. 21, Internet Security Protocols and Standards, of Computer Security Principles and Practice. Read Ch. 22, Internet Authentication Applications, of Computer Security Principles and Practice. Read Ch. 23, Operating System Security, of Computer Security Principles and Practice. Read Ch. 24, Windows and Windows Vista Security, of Computer Security Principles and Practice. Read the Week Four Read Me First. Read this weeks Electronic Reserve Readings. Participate in class discussion. Respond to weekly discussion questions. DQ #7 DQ #8 Post weekly summary. Draft a 2-3 page description on the web security issues and concerns present at each Riordan plant. Create and submit a 2-3 page security policy for McBride Financial Services, located in the Virtual Organizations. Develop a policy based on perceived needs associated within the loan department and issues in implementing online loan applications. 06/13/2012 06/16/2012 06/18/2012 06/18/2012 06/18/2012 2 1 1 1 5 20
Due
Points
Readings
Participation Discussion Questions Weekly Summary Learning Team Instructions Individual
Course Syllabus CMGT/441 Version 2
Week Five: Organization Security Issues and Concerns
Details
Objectives 5.1 Comprehend organizational security issues and concerns. 5.2 Comprehend needs for risk management and corporate planning and analysis. 5.3 Apply data security methodologies in situational cases. 5.4 Solve data security issues with proper application of the various methodologies. Read Ch. 13, Physical and Infrastructure Security, of Computer Security Principles and Practice. Read Ch. 14, Human Factors, of Computer Security Principles and Practice. Read Ch. 15, Security Auditing, of Computer Security Principles and Practice. Read Ch. 16, IT Security Management and Risk Assessment, of Computer Security Principles and Practice. Read Ch. 17, IT Security Controls, Plans and Procedures, of Computer Security Principles and Practice. Read Ch. 18, Legal and Ethical Aspects, of Computer Security Principles and Practice. Read the Week Five Read Me First. Read this weeks Electronic Reserve Readings. Participate in class discussion. Respond to weekly discussion questions. DQ #9 DQ #10 Post weekly summary. Finalize and submit an 8-10 page Learning Team paper. Prepare a Microsoft PowerPoint presentation. 06/20/2012 06/23/2012 06/25/2012 06/25/2012 06/25/2012 2 1 1 1 5 5
Due
Points
Readings
Participation Discussion Questions Weekly Summary Learning Team SR-rm-013 Project Learning Team SR-rm-013 Presentation
Optional Discussion Questions Week One Discussion Questions According to chapter 1 in the Computer Security Principles and Practices, security awareness program can be one of an organizations most powerful protection strategies. Discuss what makes a successful information security awareness program and how a security awareness program can be one of an organizations most powerful protection strategies. Based on the Barr (2011) article, how will merging information technologies such as data center
Course Syllabus CMGT/441 Version 2
virtualization impact business continuity for websites? Use your workplace, or your client's workplace, or a workplace in a case study, will cloud computing or platform as a service (PaaS) that provides dynamic scalability with enhanced infrastructure security ensure business continuity for websites or is this just a new unproven panacea? Week Two Discussion Questions Why is managing technical vulnerabilities so important to an organization managing their security environment? What are some ways to mitigate those vulnerabilities? Based on the Barr (2011) article, why is identity management considered the central component of access management and security strategies? Should identity management focus on role-based access control (RBAC)? What has the greatest positive impact on enterprise data protection (EDP), identity management, or encryption?
Week Three Discussion Questions Based on the Spring (2009) article, do you think security event management (SEM), such as the IBM Tivoli products, is feasible for small- to medium-sized businesses (SMBs)? Will SEM push SMBs to SaaS to gain an acceptable cost/benefit justification for the holistic security provided by SEM? In your current or previous workplace, have you ever worked with SEM? According to Chapters 11 and 12 in our readings, what are buffer overflow attacks? What can be done to prevent these vulnerabilities? Define software security and defensive programming. How do these techniques correlate to a reduction in vulnerabilities? Week Four Discussion Questions As hackers keep thinking of new ways to attack systems, what are some of the tools and techniques that experts believe will keep government on the cutting edge of security? Based on the Barr (2011) article, how does the common criteria standardized, global set of IT security specifications impact EDP? How does the common criteria address end-to-end data encryption throughout the information life cycle (ILM) of the data? What assurance levels, if any, does your current or previous workplace employ?
Week Five Discussion Questions What are some of the challenges facing companies when trying to implement wireless security? How does this affect their security frameworks? What can be done to overcome these challenges? Discuss the principles and challenges associated with continuous data protection. Does your organization have a CDP plan? Why or why not?
Copyright
University of Phoenix is a registered trademark of Apollo Group, Inc. in the United States and/or other countries. Microsoft, Windows, and Windows NT are registered trademarks of Microsoft Corporation in the United States and/or other countries. All other company and product names are trademarks or registered trademarks of their respective companies. Use of these marks is not intended to imply endorsement, sponsorship, or affiliation. Edited in accordance with University of Phoenix editorial standards and practices.
También podría gustarte
- CMGT445 SyllabusDocumento7 páginasCMGT445 SyllabusArsalan LariAún no hay calificaciones
- UntitledDocumento1 páginaUntitledArsalan LariAún no hay calificaciones
- CMGT445 SyllabusDocumento7 páginasCMGT445 SyllabusArsalan LariAún no hay calificaciones
- UntitledDocumento1 páginaUntitledArsalan LariAún no hay calificaciones
- UntitledDocumento1 páginaUntitledArsalan LariAún no hay calificaciones
- UntitledDocumento1 páginaUntitledArsalan LariAún no hay calificaciones
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeCalificación: 4 de 5 estrellas4/5 (5794)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe EverandThe Little Book of Hygge: Danish Secrets to Happy LivingCalificación: 3.5 de 5 estrellas3.5/5 (399)
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryCalificación: 3.5 de 5 estrellas3.5/5 (231)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceCalificación: 4 de 5 estrellas4/5 (894)
- The Yellow House: A Memoir (2019 National Book Award Winner)De EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Calificación: 4 de 5 estrellas4/5 (98)
- Shoe Dog: A Memoir by the Creator of NikeDe EverandShoe Dog: A Memoir by the Creator of NikeCalificación: 4.5 de 5 estrellas4.5/5 (537)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureCalificación: 4.5 de 5 estrellas4.5/5 (474)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe EverandNever Split the Difference: Negotiating As If Your Life Depended On ItCalificación: 4.5 de 5 estrellas4.5/5 (838)
- Grit: The Power of Passion and PerseveranceDe EverandGrit: The Power of Passion and PerseveranceCalificación: 4 de 5 estrellas4/5 (587)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaCalificación: 4.5 de 5 estrellas4.5/5 (265)
- The Emperor of All Maladies: A Biography of CancerDe EverandThe Emperor of All Maladies: A Biography of CancerCalificación: 4.5 de 5 estrellas4.5/5 (271)
- On Fire: The (Burning) Case for a Green New DealDe EverandOn Fire: The (Burning) Case for a Green New DealCalificación: 4 de 5 estrellas4/5 (73)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersCalificación: 4.5 de 5 estrellas4.5/5 (344)
- Team of Rivals: The Political Genius of Abraham LincolnDe EverandTeam of Rivals: The Political Genius of Abraham LincolnCalificación: 4.5 de 5 estrellas4.5/5 (234)
- Rise of ISIS: A Threat We Can't IgnoreDe EverandRise of ISIS: A Threat We Can't IgnoreCalificación: 3.5 de 5 estrellas3.5/5 (137)
- The Unwinding: An Inner History of the New AmericaDe EverandThe Unwinding: An Inner History of the New AmericaCalificación: 4 de 5 estrellas4/5 (45)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyCalificación: 3.5 de 5 estrellas3.5/5 (2219)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreCalificación: 4 de 5 estrellas4/5 (1090)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Calificación: 4.5 de 5 estrellas4.5/5 (119)
- The Perks of Being a WallflowerDe EverandThe Perks of Being a WallflowerCalificación: 4.5 de 5 estrellas4.5/5 (2099)
- Her Body and Other Parties: StoriesDe EverandHer Body and Other Parties: StoriesCalificación: 4 de 5 estrellas4/5 (821)
- Grade 7 Kitchen Layout SymbolsDocumento3 páginasGrade 7 Kitchen Layout SymbolsJoanna Mae David88% (112)
- Grade 11 Recognition 2019 PDFDocumento12 páginasGrade 11 Recognition 2019 PDFArjhayee JaronAún no hay calificaciones
- Tema 14Documento6 páginasTema 14LaiaAún no hay calificaciones
- SteelDocumento23 páginasSteelMelinda GordonAún no hay calificaciones
- University of The Cordilleras College of Law Criminal ProcedureDocumento4 páginasUniversity of The Cordilleras College of Law Criminal ProcedureRowena DumalnosAún no hay calificaciones
- Differianted Math Lesson Plan Triangular Prisms - Diego MenjivarDocumento4 páginasDifferianted Math Lesson Plan Triangular Prisms - Diego Menjivarapi-491433072Aún no hay calificaciones
- RPP Struktur AtomDocumento4 páginasRPP Struktur AtomFawnia D'Genkbellzz Ezzar FluorinAnindyaAún no hay calificaciones
- CVDocumento16 páginasCVAviwe ApleniAún no hay calificaciones
- HIP Online Reporting Template - 9 JUNEDocumento23 páginasHIP Online Reporting Template - 9 JUNEpejabatAún no hay calificaciones
- Faculty Screening J.ODocumento2 páginasFaculty Screening J.OIvy CalladaAún no hay calificaciones
- Pepsi ScreeningDocumento13 páginasPepsi Screeningapi-459936554Aún no hay calificaciones
- Practical Research 2 Quarter 4 Module 5 Lesson 1Documento2 páginasPractical Research 2 Quarter 4 Module 5 Lesson 1juvy abelleraAún no hay calificaciones
- Describing Colleagues American English Pre Intermediate GroupDocumento2 páginasDescribing Colleagues American English Pre Intermediate GroupJuliana AlzateAún no hay calificaciones
- Community Organizing Philosophies of Addams and AlinskyDocumento40 páginasCommunity Organizing Philosophies of Addams and AlinskymaadamaAún no hay calificaciones
- Lesson Plan 7e's Sea BreezeDocumento3 páginasLesson Plan 7e's Sea BreezeMark Joel Macaya GenoviaAún no hay calificaciones
- Thesis Video WatermarkingDocumento6 páginasThesis Video WatermarkingPayToWriteAPaperLubbock100% (4)
- Brief Syllabus in School Administration and SupervisionDocumento2 páginasBrief Syllabus in School Administration and SupervisionEingilbert BenoliraoAún no hay calificaciones
- Erasmus Module CatalogueDocumento9 páginasErasmus Module Catalogueelblaco87Aún no hay calificaciones
- Civitas Academica of English Education and Stakeholders’ Un-derstanding of Vision, Missions, Goals, and Targets of English Education Department at IAIN Bukittinggi in Year 2018 by : Melyann Melani, Febria Sri Artika, Ayu NoviasariDocumento7 páginasCivitas Academica of English Education and Stakeholders’ Un-derstanding of Vision, Missions, Goals, and Targets of English Education Department at IAIN Bukittinggi in Year 2018 by : Melyann Melani, Febria Sri Artika, Ayu NoviasariAyy SykesAún no hay calificaciones
- Resume PDFDocumento1 páginaResume PDFapi-581554187Aún no hay calificaciones
- Understanding the challenges and opportunities of artificial intelligenceDocumento6 páginasUnderstanding the challenges and opportunities of artificial intelligenceHương DươngAún no hay calificaciones
- STAR Interview GuideDocumento1 páginaSTAR Interview GuideLeona Mae BaylomoAún no hay calificaciones
- Entrep - Module-2Documento6 páginasEntrep - Module-2Frankenstein ParkAún no hay calificaciones
- F18Documento4 páginasF18Aayush ShahAún no hay calificaciones
- Defining Communication Through Creative PresentationsDocumento10 páginasDefining Communication Through Creative PresentationsJoseph SuperableAún no hay calificaciones
- San Jose Community College: College of Arts and SciencesDocumento5 páginasSan Jose Community College: College of Arts and SciencesSH ENAún no hay calificaciones
- Step-By-Step Analysis and Planning Guide: The Aira ApproachDocumento5 páginasStep-By-Step Analysis and Planning Guide: The Aira ApproachDaniel Osorio TorresAún no hay calificaciones
- Abm-Amethyst Chapter 2Documento12 páginasAbm-Amethyst Chapter 2ALLIYAH GRACE ADRIANOAún no hay calificaciones
- SyllabusDocumento13 páginasSyllabusKj bejidorAún no hay calificaciones
- EN5VC IIIf 3.8 - 2023 2024 - Day2Documento3 páginasEN5VC IIIf 3.8 - 2023 2024 - Day2Ma. Feliza Saligan100% (1)