Documentos de Académico
Documentos de Profesional
Documentos de Cultura
Iso 27001 Cobit and Itil Self Assessment Tools
Cargado por
corvdDerechos de autor
Formatos disponibles
Compartir este documento
Compartir o incrustar documentos
¿Le pareció útil este documento?
¿Este contenido es inapropiado?
Denunciar este documentoCopyright:
Formatos disponibles
Iso 27001 Cobit and Itil Self Assessment Tools
Cargado por
corvdCopyright:
Formatos disponibles
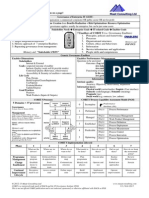
Primary Security Domain
COBIT 4.0 Control Objective
ISO 27001/17799
ISO 20000/ITIL Reference
Question Number
Question (Control Objective) Business Staff
Question Number 1
I. Security Policy
PO6 Communicate Management Aims and Direction PO4.14 Contracted Staff Policies and Procedures
3.1 Information Security Policy 6.6 Information Security Management 1 4.1 Information Security Infrastructure 6.6.1 General (See ISO Mapping for additional details) 6.6.6 Controls c) 3.1 Information Security Policy 6.6 Information Security Management 2 4.1 Information Security Infrastructure 6.6.1 General (See ISO Mapping for additional details) 6.6.6 Controls c) 12.2 Reviews of Security Policy and Technical Compliance 6.6 Information Security Management 3 6.6.1 General (See ISO Mapping for additional details) 6.6.6 Controls (a,c,e)
Are you and members of your department aware of information security policies and have you been provided with any type of awareness training or ongoing communications? For policies that have been provided, are the supported and enforced by your department's leadership?
I. Security Policy
PO6 Communicate Management Aims and Direction PO4.14 Contracted Staff Policies and Procedures
I. Security Policy
M1 Monitor the Processes 1.1 Collecting Monitoring Data 1.2 Assessing Performance 1.3 Assessing Customer Satisfaction 1.4 Management Reporting M2 Assess Control Adequacy 2.1 Internal Control Monitoring M1 Monitor the Processes 1.1 Collecting Monitoring Data 1.2 Assessing Performance 1.3 Assessing Customer Satisfaction 1.4 Management Reporting M2 Assess Control Adequacy M1 Monitor the Processes 1.1 Collecting Monitoring Data 1.2 Assessing Performance 1.3 Assessing Customer Satisfaction 1.4 Management Reporting M2 Assess Control Adequacy 2.1 Internal Control Monitoring M1 Monitor the Processes 1.1 Collecting Monitoring Data 1.2 Assessing Performance 1.3 Assessing Customer Satisfaction 1.4 Management Reporting M2 Assess Control Adequacy 2.1 Internal Control Monitoring 11.18 Protection of Disposed Sensitive Information, 11.26 Archiving
Is there a process in place to review employee compliance with organizational policies?
I. Security Policy
12.2 Reviews of Security Policy and Technical Compliance
6.6 Information Security Management 6.6.1 General (See ISO Mapping for additional details) 6.6.6 Controls (a,c,e)
3.1
I. Security Policy
12.2 Reviews of Security Policy and Technical Compliance
6.6 Information Security Management 4 6.6.1 General (See ISO Mapping for additional details) 6.6.6 Controls (a,c,e)
Has your department or employees ever requested an exception 4 from policy items?
I. Security Policy
12.2 Reviews of Security Policy and Technical Compliance
6.6 Information Security Management 4.1 6.6.1 General (See ISO Mapping for additional details) 6.6.6 Controls (a,c,e)
Are you familiar with the University's Risk Acceptance Process? 4.1
I. Security Policy
5.2.2 Information labeling and handling 6.6 Information Security Management 5 6.6.1 General (See ISO Mapping for additional details)
Do policies and procedures exist for the handling of paper copy documents?
I. Security Policy
11.27 Protection of Sensitive Messages
3 Security Policy 6.2.1 Information security education and training
6.6 Information Security Management 6.6.6 Controls (a,c,e)
Are you aware of email and Internet acceptable usage policies?
II. Organizational Security
PO1 Define a Strategic IT Plan PO4.11 IT Staffing
4.1 Information Security Infrastructure 4 Planning and Implementing Service Management
Does your department collaborate with the IT department for purposes of strategic planning?
II. Organizational Security
4.2 Organizational Placement of the IT Function 4.4 Roles and Responsibilities 4.6 Responsibility for Logical and Physical Security
4.1 Information Security Infrastructure 6.11 Including Security in Responsibilities 8.1 Operational procedures and responsibilities
6.6 Information Security Management 8 6.6.1 General (See ISO Mapping for additional details) 6.6.6 Controls (a,c,d)
Are members of your department assigned responsibilities for 6 information security and if so do they have specific directives for protecting critical information?
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 1
Primary Security Domain
COBIT 4.0 Control Objective
ISO 27001/17799
ISO 20000/ITIL Reference
Question Number 9
Question (Control Objective) Business Staff
Question Number 7
II. Organizational Security
II. Organizational Security
PO7 Manage Human Resources 7.1 Personnel Recruitment and Promotion 7.2 Personnel Qualifications 7.5 Cross-training or Staff Backup 7.6 Personnel Clearance Procedures PO7 Manage Human Resources 7.1 Personnel Recruitment and Promotion 7.2 Personnel Qualifications 7.5 Cross-training or Staff Backup 7.6 Personnel Clearance Procedures PO7 Manage Human Resources 7.1 Personnel Recruitment and Promotion 7.2 Personnel Qualifications 7.5 Cross-training or StaffServices DS2 Manage Third-party Backup 2.4 Third-party Qualifications 2.5 Outsourcing Contracts DS2 Manage Third-party Services 2.6 Continuity of Services 2.7 Security Relationships DS5 Ensure Systems Security 5.13 Counterparty Trust PO2.3 Data Classification Scheme PO4.7 Ownership and Custodianship PO4.8 Data and System Ownership PO2.3 Data Classification Scheme
6.1 Personnel Security
3.3.2 Professional Development a) Recruitment
Are background and reference checks performed and verified during the recruiting hiring and processes?
6.1 Personnel Security
3.3 Competence, Awareness, and Training
II. Organizational Security
6.1 Personnel Security
II. Organizational Security
4.3 Outsourcing 4.3.1 Security requirements in outsourcing contracts 4.3 Outsourcing 4.3.1 Security requirements in outsourcing contracts 4.2, 4.3, 6.1, 6.3, 8.1, 8.7, 10.5 4.2.2 Security requirements in third party contracts 4.3 Outsourcing 4.3.1 Security requirements in 5.2 Information Classification
6.6 Information Security Management 6.6.1 General (See ISO Mapping for additional details) 7.3 Supplier Management (See ISO 27001 mapping for additional details)
10
II. Organizational Security
7.3 Supplier Management 6.6.3 Security Risk Assessment Practices
10
Does your department include information security requirements 11 in contracts with third parties that handle or change sensitive data or systems? 12
II. Organizational Security
7 Relationship Process 7.3 Supplier Management 7.3.2 Contract Management 6.62 Identifying and Classifying Information Assets 11
III. Asset Classification and Control
Do you know which of the data items in your department need 13 protected? Do you have a way of identifying this data that is different than the words and vocabulary you use to identify data that does not need secured? Do you know which computer systems in your department are 14 used to process or store critical or private data? Are you aware of any mechanism to document any such systems? Have you worked with members of the IT department to map out 15 information flows into and out of the organization?
III. Asset Classification and Control III. Asset Classification and Control
5.2 Information Classification
6.62 Identifying and Classifying Information Assets
12
PO4.8 Data and System Ownership
3 Security Policy 7.2.5 Security of equipment offpremises 8.7.2 Security of media in transit 9.8.1 Mobile computing 3 Security Policy 7.2.5 Security of equipment offpremises 8.7.2 Security of media in transit 9.8.1 Mobile computing 7.2.5 Security of equipment offpremises 8.7.2 Security of media in transit 9.8.1 Mobile computing
6.6 Information Security Management 13 6.6.1 General (See ISO Mapping for additional details)
III. Asset Classification and Control
PO8 Ensure Compliance with External Requirements 8.4 Privacy, Intellectual Property and Data Flow
6.6 Information Security Management 13.1 6.6.1 General (See ISO Mapping for additional details)
Have you worked with members of the IT department to map out 15.1 systems movement (such as mobile devices) into and out of the organization?
III. Asset Classification and Control
PO7 Manage Human Resources 7.8 Job Change and Termination PO4.8 Data and System Ownership DS9 Manage the Configuration 9.1 Configuration Recording 9.3 Status Accounting 9.4 Configuration Control 9.8 Software Accountability DS5 Ensure Systems Security 5.3 Security of Online Access to Data 5.4 User Account Management DS5 Ensure Systems Security 5.4 User Account Management 5.5 Management Review of User Accounts 5.21 Protection of Electronic Value
6.6 Information Security Management 14 6.6.1 General (See ISO Mapping for additional details)
Do you have the ability to track information, mobile or storage devices in the possession of employees and ensure safe return of those items upon employee termination? 16
III. Asset Classification and Control
10.4.1 Control of operational software 9.1 Configuration Management 10.5.2 Technical review of operating 9.1.4 Configuration Status Accounting and system changes Reporting 7.2 Equipment Security 9.1 BUSINESS REQUIREMENT FOR ACCESS CONTROL 9.1 Business Requirement for Access Control 9.2 User Access Management 9.2.1 User registration 9.2.4 Review of user access rights 6.6 Information Security Management 15 6.6.7 Documents and Records d) control over access to information, assets, and systems 6.6 Information Security Management 16 6.6.7 Documents and Records d) control over access to information, assets, and systems
IX. Access Control
Do you provide IT with access requirements to information, data, 17 and applications in use by your department? Is a new employee or terminated employee process in place to add or remove employees access to key systems and data? 18
IX. Access Control
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 2
Primary Security Domain
COBIT 4.0 Control Objective
ISO 27001/17799
ISO 20000/ITIL Reference
Question Number
Question (Control Objective) Business Staff
Question Number
IX. Access Control
DS5 Ensure Systems Security 5.2 Identification, Authentication and Access 5.4 User Account Management 5.5 Management Review of User Accounts 5.6 User Control of User Accounts DS5 Ensure Systems Security 5.2 Identification, Authentication and Access 5.4 User Account Management 5.5 Management Review of User Accounts 5.6 User Control of User Accounts DS5 Ensure Systems Security 5.2 Identification, Authentication and Access 5.4 User Account Management 5.5 Management Review of User Accounts 5.6 User Control of User Accounts DS5 Ensure Systems Security 5.2 Identification, Authentication and Access 5.4 User Account Management 5.5 Management Review of User Accounts 5.6 User Control of User Accounts
9.2.3 User password management
6.6 Information Security Management 17 6.6.1 General (See ISO Mapping for additional details) 6.6.7 Documents and Records d) control over access to information, assets, and systems 6.6 Information Security Management 18 6.6.1 General (See ISO Mapping for additional details) 6.6.7 Documents and Records d) control over access to information, assets, and systems
Are you aware of requirements for the complexity or length of your password?
IX. Access Control
9.2.3 User password management
Do you change you password often?
IX. Access Control
IX. Access Control
5.2.2 Information labeling and handling 6.6 Information Security Management 19 9.2 User Access Management 6.6.1 General (See ISO Mapping for additional details) 6.6.7 Documents and Records d) control over access to information, 5.2.2 Information labeling and handling 6.6 Information Security Management 20 9.2 User Access Management 6.6.1 General (See ISO Mapping for additional details) 6.6.7 Documents and Records d) control over access to information, assets, and systems 7.1 Secure Areas 7.2 Equipment Security 6.6 Information Security Management 21 6.6.1 General (See ISO Mapping for additional details) 6.6 Information Security Management 22 6.6.1 General (See ISO Mapping for additional details)
Do you ever utilize a password or userID that is shared between multiple employees?
Use accounts that have system administrator rights only in special situations, such as when installing software or configuring your system?
V. Physical and Environmental Security
DS12 Manage Facilities 12.1 Physical Security
Is access controlled, monitored, and recorded to your work areas 19 or facilities?
VI. Equipment Security
PO6 Communicate Management Aims and Direction 6.3 Communication of Organization Policies 6.6 Compliance with Policies, Procedures and Standards 6.11 Communication of IT Security Awareness PO8 Ensure Compliance with External Requirements 8.4 Privacy, Intellectual Property and Data Flow DS7 Educate and Train Users PO9 Assess Risks 9.1 Business Risk Assessment 9.3 Risk Identification DS5 Ensure Systems Security 5.8 Data Classification PO9 Assess Risks 9.5 Risk Action Plan AI1 Identify Automated Solutions 1.9 Cost-effective Security Controls DS7 Educate and TrainSolutions AI1 Identify Automated Users 1.1 Definition of Information Requirements
9.8.1 Mobile computing
Do employees in your department understand requirements to protect mobile devices that contain sensitive or critical data?
20
VII. General Controls
4.2.1 Identification of risks from third party access 12.3 System Audit Considerations 12.3.1 System audit controls 4.2.1 Identification of risks from third party access 12.3 System Audit Considerations 12.3.1 System audit controls No direct mapping (See COBIT mapping for additional details)
6.6.3 Security Risk Assessment Practices 6.6.4 Risks to Information Assets
23
Has your department worked with the IT or Information Security 21 department to identify risks to key systems and data for your department?
VII. General Controls
6.6.3 Security Risk Assessment Practices 6.6.4 Risks to Information Assets
22
VII. General Controls
6.6 Information Security Management 6.6.1 General (See COBIT Mapping for additional details) 9.1.3 Configuration Control 10.1.5 Design, Build and Configure Release b) ensure the integrity is maintained during build, installation, packaging, and delivery 24 Are automated or manual processes in place to ensure the accuracy, validity, and non-repudiation of transactions in your department?
23
VII. General Controls
DS11 Manage Data 8.7.3 Electronic commerce security 11.1 Data Preparation Procedures 10.2 Security in Application Systems 11.2 Source Document Authorization Procedures 10.3 Cryptographic Controls 11.3 Source Document Data Collection 11.4 Source Document Error Handling 11.7 Accuracy, Completeness and Authorization Checks 11.8 Data Input Error Handling 11.9 Data Processing Integrity 11.10 Data Processing Validation and Editing 11.11 Data Processing Error Handling 11.14 Output Balancing and Reconciliation 11.15 Output Review and Error Handling 11.27 Protection of Sensitive Messages 11.29 Electronic Transaction Integrity
24
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 3
Primary Security Domain
COBIT 4.0 Control Objective
ISO 27001/17799
ISO 20000/ITIL Reference
Question Number
Question (Control Objective) Business Staff
Question Number 25
VII. General Controls
VII. General Controls
M1 Monitor the Processes 12.2 Reviews of Security Policy and 1.1 Collecting Monitoring Data Technical Compliance 1.2 Assessing Performance 1.3 Assessing Customer Satisfaction 1.4 Management Reporting M2 Assess Control Adequacy 2.1 Internal Control Monitoring M3 Obtain Independent Assurance No relevant mapping 3.3 Independent Effectiveness Evaluation of IT Services 3.4 Independent Effectiveness Evaluation of Third-party Service Providers 3.5 Independent Assurance of Compliance with Laws and Regulatory Requirements and Contractual Commitments 3.6 Independent Assurance of Compliance with Laws and Regulatory Requirements by Third-party Service Providers 3.7 Competence of Independent Assurance Function 11.18 Protection of Disposed Sensitive Information
6.6 Information Security Management 6.6.1 General (See ISO Mapping for additional details) 6.6.3 Security Risk Assessment Practices
6.6 Information Security Management 6.6.1 General (See ISO Mapping for additional details) 6.6.6 Controls f) Expert help on risk assessment and control implementation
26
VII. General Controls
5.2.2 Information labeling and handling 6.6 Information Security Management 25 6.6.1 General (See ISO Mapping for additional details)
Does your organization have a secure disposal process for dispose of paper copy documents containing sensitive information? Have you ever had to disclose a loss or leak of sensitive information to a student?
27
VII. General Controls
11.18 Protection of Disposed Sensitive Information
VII. General Controls
5.2.2 Information labeling and handling 6.6 Information Security Management 26 6.6.1 General (See ISO Mapping for additional details) 6.6.5 Security and Availability of Information a) disclosure of sensitive information to unauthorized parties 6.6.6 Controls f) Expert help on risk assessment and control implementation 11.26 Archiving, 11.27 Protection of Sensitive Messages 8.7.4 Security of electronic mail 6.6 Information Security Management 27 6.6.1 General (See ISO Mapping for additional details) 11.26 Archiving, 11.27 Protection of Sensitive Messages 8.7.4 Security of electronic mail 6.6 Information Security Management 28 6.6.1 General (See ISO Mapping for additional details) 6.6 Information Security Management 6.6.1 General (See ISO Mapping for additional details) 3.3 Competence, Awareness, and Training 3.3.1 General 3.3.2 Professional Development 29
28
Do you know how long your email is retained?
VII. General Controls
Do you archive email and if so, where do you store the archive?
VIII. Communications & Operations Management
PO9 Assess Risks AI3-3.6 Acquire and Maintain Technology Infrastructure PO11 Manage Quality AI4 Develop and Maintain Procedures 4.2 User Procedures Manual 4.3 Operations Manual 4.4 Training Materials DS7 Educate and Train Users 7.1 Identification of Training Needs DS5 Ensure Systems Security 5.19 Malicious Software Prevention, Detection and Correction DS5 Ensure Systems Security 5.19 Malicious Software Prevention, Detection and Correction AI3 Acquire and Maintain Technology Infrastructure 3.1 Assessment of New Hardware and Software DS8 Assist and Advise Customers PO11 Manage Quality 11.9 Acquisition and Maintenance Framework for the Technology Infrastructure
10 Systems Development and Maintenance 8.1.5 Separation of development and operational facilities 6.2 User Training
29
VIII. Communications & Operations Management
Are information security related procedures integrated into work 30 procedures and are employees in your department provided any security awareness training?
VIII. Communications & Operations Management VIII. Communications & Operations Management X. Systems Development and Maintenance
8.3 Protection against Malicious Software 8.3 Protection against Malicious Software 10.1 Security Requirements of Systems 10.1.1 Security requirements analysis and specification
6.6 Information Security Management 30 6.6.1 General (See ISO Mapping for additional details) 6.6 Information Security Management 30.1 6.6.1 General (See ISO Mapping for additional details) 7.3 Supplier Management
Do your systems all have antivirus and antispyware software and 31 do employees ever disable or remove the software? If you answered yes to question 30, do employees ever disable or 31.1 remove the software? 32
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 4
Primary Security Domain
COBIT 4.0 Control Objective
ISO 27001/17799
ISO 20000/ITIL Reference
Question Number
Question (Control Objective) Business Staff
Question Number 33
X. Systems Development and Maintenance
PO9 Assess Risks 9.1 Business Risk Assessment 9.3 Risk Identification AI3-3.6 Acquire and Maintain Technology Infrastructure 11.9 Acquisition and Maintenance Framework for the Technology Infrastructure PO9 Assess Risks AI3-3.6 Acquire and Maintain Technology Infrastructure PO11 Manage Quality AI5 Install and Accredit Systems 5.7 Testing of Changes 5.11 Operational Test 5.12 Promotion to Production AI5 Install and Accredit Systems 5.9 Final Acceptance Test 5.13 Evaluation of Meeting User Requirements 5.14 Managements Post-implementation Review AI5 Install and Accredit Systems 5.7 Testing of Changes AI6 Manage Changes 6.4 Emergency Changes
X. Systems Development and Maintenance X. Systems Development and Maintenance
8.1.2 Operational change control 6.6.3 Security Risk Assessment Practices 10.5.1 Change control procedures 10.1 Security Requirements of Systems 10.1.1 Security requirements analysis and specification 12.3.1 System audit controls 10 Systems Development and 6.6 Information Security Management Maintenance 6.6.1 General (See ISO Mapping for additional details) 8.2 System Planning and Acceptance 10 Release Process 8.1.5 Separation of development and 10.1.2 Release Policy c) authority of release operational facilities into acceptance test and production environments 8.2.2 System acceptance 10 Release Process 10.1.2 Release Policy g) verification and acceptance of release 10 Release Process 10.1.2 Release Policy c) authority of release into acceptance test and production environments g) verification and acceptance of release 9.2 Change Management 32
34
35
X. Systems Development and Maintenance
Does you department review and accept new technology system 36 functionality and is information security a component of the review and acceptance process? Do you review or test any changes to your systems and applications prior to the IT department implementing those changes? 37
X. Systems Development and Maintenance
8.1.2 Operational change control 10.5 Security in Development and Support Processes 10.5.1 Change control procedures 10.5.2 Technical review of operating system changes 10.5.3 Restrictions on changes to software packages 8.1.2 Operational change control 10.5 Security in Development and Support Processes 10.5.1 Change control procedures 10.5.2 Technical review of operating system changes 10.5.3 Restrictions on changes to software packages
33
X. Systems Development and Maintenance
AI5 Install and Accredit Systems 5.7 Testing of Changes AI6 Manage Changes 6.4 Emergency Changes
9.2 Change Management 9.2.4 Change management reporting, analysis, and actions
38
XI. Business Continuity
XI. Business Continuity
XI. Business Continuity
XI. Business Continuity
DS4 Ensure Continuous Service 4.2 IT Continuity Plan Strategy and Philosophy 4.4 Minimizing IT Continuity Requirements 4.10 Critical IT Resources DS10 Manage Problems and Incidents 10.1 Problem Management System 10.2 Problem Escalation DS12 Manage Facilities 12.6 Uninterruptible Power Supply DS4 Ensure Continuous Service 4.2 IT Continuity Plan Strategy and Philosophy 4.4 Minimizing IT Continuity Requirements 4.10 Critical IT Resources DS10 Manage Problems and Incidents 10.1 Problem Management System 10.2 Problem Escalation DS12 Manage Facilities 12.6 Uninterruptible Power Supply DS4 Ensure Continuous Service 4.3 IT Continuity Plan Contents 4.9 User Department Alternative Processing Backup Procedures DS4 Ensure Continuous Service 4.2 IT Continuity Plan Strategy and Philosophy 4.10 Critical IT Resources DS10 Manage Problems and Incidents 10.1 Problem Management System 10.2 Problem Escalation
11 Business Continuity Management 6.3 Service Continuity and Availability 34 11.1.2 Business continuity and impact Management analysis 6.3.4 Service Continuity Planning and Testing
Has your department worked with the IT or Information Security 39 department to identify the core systems, applications, and information in order to determine the impact to the department in the event of un-availability, loss, theft, or disclosure?
11 Business Continuity Management 11.1.3 Writing and implementing continuity plans 11.1.4 Business continuity planning framework
6.3 Service Continuity and Availability Management 6.3.4 Service Continuity Planning and Testing
40
11 Business Continuity Management 11.1.3 Writing and implementing continuity plans 11.1 Aspects of Business Continuity Management 11.1.3 Writing and implementing continuity plans
6.3 Service Continuity and Availability 35 Management 6.3.3 Service Continuity Strategy a) maximum acceptable period of lost service 6.3 Service Continuity and Availability 36 Management 6.3.4 Service Continuity Planning and Testing
Does your department have requirements for timeframes to recover each of the core systems, applications, or information that affect the departments operations?
41
Are you aware of procedures or contact listings in the event of a 42 disaster involving your facility and IT systems?
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 5
Primary Security Domain
COBIT 4.0 Control Objective
ISO 27001/17799
ISO 20000/ITIL Reference
Question Number
Question (Control Objective) Business Staff
Question Number 43
XI. Business Continuity
XI. Business Continuity
XII. Compliance
XII. Compliance
DS4 Ensure Continuous Service 4.3 IT Continuity Plan Contents 4.9 User Department Alternative Processing Backup Procedures DS4 Ensure Continuous Service 4.6 Testing the IT Continuity Plan 4.12 Offsite Backup Storage DS11 Manage Data 11.23 Backup and Restoration 11.24 Backup Jobs 11.25 Backup Storage PO8 Ensure Compliance with External Requirements 8.1 External Requirements Review 8.2 Practices and Procedures for Complying with External Requirements 8.3 Safety and Ergonomic Compliance 8.4 Privacy, Intellectual Property and Data Flow 8.5 Electronic Commerce 8.6 Compliance With Insurance Contracts DS5 Ensure Systems Security 5.7 Security Surveillance 5.11 Incident Handling
11.1 Aspects of Business Continuity Management 11.1.5 Testing, maintaining and reassessing business continuity plans 8.4 Housekeeping 8.4.1 Information back-up 11.1 Aspects of Business Continuity Management
6.3 Service Continuity and Availability 37 Management 6.3.4 Service Continuity Planning and Testing 6.3 Service Continuity and Availability 38 Management 6.3.4 Service Continuity Planning and Testing
Has your department been involved with any testing of disaster plans?
Do employees in your department have access to store files on network folders that are backed up on a daily basis? If so, have you been able to successfully restore data when required?
44
12.1 Compliance With Legal Requirements
6.6.5 Security and Availability of Information
39
Are any regulatory requirements relevant to information your 45 department creates or stores? Examples of potential legal or regulatory requirements are; PCI Compliance (Visa, MasterCard), HIPAA (Healthcare), GLB (Insurance, Financial), software licensing, intellectual property rights, contractual obligations, etc.
12.1 Compliance with Legal 6.6.6 Controls c) See ISO 27001 mapping for 40 Requirements additional detail 12.3 System Audit Considerations 9.7 Monitoring System Access and Use 12.2.1 Compliance with security policy 12.2.2 Technical compliance checking 6.3 Responding to Security Incidents and Malfunctions
Does your department have the ability to monitor employee behavior with regard to compliance to organizational policies and/or identify illegal activities?
46
XII. Compliance
DS9 Manage the Configuration 9.5 Unauthorized Software 9.8 Software Accountability DS11 Manage Data 11.5 Source Document Retention 11.19 Storage Management 11.20 Retention Periods and Storage Terms 11.26 Archiving
XII. Compliance
5.1.1 Inventory of assets 12.1 Compliance with Legal Requirements 12.1.2 Intellectual property rights 8.6 Media Handling and Security 12 Compliance 12.1.3 Safeguarding of organizational records 12.1.4 Data protection and privacy of personal information
9.1 Configuration Management 9.1.2 Configuration Identification e) licenses 9.1.4 Configuration Status Accounting and Reporting 6.6 Information Security Management 41 6.6.1 General (See ISO Mapping for additional details)
47
Are you aware of legal or organization policy or requirements to 48 retain data? (note: Examples could include financial, health, or
transaction history / information)
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 6
Question (Control Objective) IT Staff
Has an information security policy framework been developed including who is responsible for development, review, and approval of policies?
Has the policy framework been implemented resulting in creation of information security policies that are supported in the highest levels of the organization?
Does internal staff regularly monitor security controls to measure performance and adequacy?
If you answered yes to question 3, is effectiveness measured against security policy, regulatory/contract compliance?
Is there a current process for defining and ongoing review of policy exceptions?
Are you familiar with the University's Risk Acceptance Process?
Is strategic IT planning performed to determine business requirements that could have an impact on technologies, staffing, and information security requirements?
Has a security organizational structure been created that defines information security roles and responsibilities?
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 7
Question (Control Objective) IT Staff
Are background and reference checks performed and verified during the recruiting and hiring and processes?
Are security skill requirements reviewed and mapped to current security staff capabilities and evaluated against organizational security requirements?
Are security skills redundant within staff members so that no critical security functions are dependent on a single employee? Are there specific criteria that a business partner or vendor must meet for security requirements?
When partnering with a third party or contracting services, is a risk review performed to determine risks such as handling sensitive data and sharing proprietary information or intellectual property? Are business associate agreements or similar contracts required for third party partners that contain expected levels of security? Are those contracts typically included and signed for all partner access to systems? Has a data and/or asset classification scheme been developed and implemented and does it map handling requirements to the classification levels?
Has an asset inventory system been implemented that includes asset criticality and/or classification ratings? Have information flows and systems moves into and out of systems and facilities been identified? Is there a policy that defines this flow of data, systems, and information?
Is there a policy that defines acceptable flow of data, systems, and information between third parties?
Is there a document or system that contains hardware, software, application, or operating system configurations for your department?
Are there defined procedures for granting access levels to staff and third parties based on there job requirement to access the information? Have employees been identified that add/remove user accounts and is account creation/removal logged so that information can be audited or reviewed?
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 8
Question (Control Objective) IT Staff
Are physical security controls implemented for key IT systems such as the data center and has a third party assessed those controls for the level of effectiveness? Has a policy been defined and implemented that outlines security for mobile devices such as laptops and PDA's, and mobile storage such as flash drives?
Have you worked with departments in the organization to assess risks to critical data or systems and the resulting impact to the business should those risks be realized?
Have high risk areas identified through risk assessment activities been prioritized and a plan to prioritize the remediation of these risks been developed? Does automation of businesses processes through IT systems cause additional risk to the security of information and have you worked to the identify automated processes that might contain those risks? Have integrity controls been implemented in systems that process transactions to verify accuracy, validity, and non-repudiation?
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 9
Question (Control Objective) IT Staff
Is regular security assessment and testing performed that includes things such as penetration testing, vulnerability scanning, policy and configuration review?
Does your organization provision the services of a trusted advisor to assess information security controls and provide guidance for areas of weakness or vulnerability?
If you answered yes to question 17, do you prioritize patches and perform testing to determine suitability to be implemented on production systems?
Are specific work procedures either documented or provided verbally? If so, is security integrated into the procedures?
Do all systems in your department have current anti-virus software installed and are definition files updated on a regular basis (preferably every day)? If you answered yes to question 32, are definition files updated on a regular basis (preferably every day)? Is security an integrated component of the evaluation and selection of Information Technology solutions?
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 10
Question (Control Objective) IT Staff
Is a risk review performed prior to the implementation of new infrastructure (routers, switches, servers, firewalls, etc)?
Is there a defined process for monitoring vendors for software patches or vulnerabilities that impact the infrastructure systems in production? Are changes to existing systems or new implementations performed in a test environment separate from production systems?
Is acceptance testing a part of the pre-production testing process and does acceptance include both key IT and Business personnel?
Is a formal or informal change management function practiced for changes to systems? Does it include changes to configuration including patching and functionality.
Is there a log or document that outlines all changes including who reviewed the changes, testing performed, back out plans, acceptance/denial, and who performed the changes?
Has a business impact analysis been performed with regard to identifying critical or sensitive information?
If you answered yes to question 26, have provisions been made to ensure critical information is available for mission critical business processes in the event of a security incident?
Does your department have the ability to identify and resolve such incidents in a timeframe consistent with business operational requirements?
Has your department developed business continuity or disaster recovery plans that include maintaining or restoring basic IT resources during a disaster or outage?
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 11
Question (Control Objective) IT Staff
Are these plans tested on a recurring basis and updated as required depending on the outcome of tests?
Has the IT staff collaborated with key business users to make sure that business critical information is backed up and available offsite? If so, have restore operations been tested successfully?
Does an employee responsible for information security review requirements for regulatory compliance and legal obligations and collaborate with executive leadership and legal counsel to determine which issues are relevant to the organization? Examples include PCI Compliance (Visa, MasterCard), HIPAA (Healthcare), GLB
(Insurance, Financial), software licensing, intellectual property rights, contractual obligations, etc.
Have you deployed processes and/or automated alerts so that policy violations and intrusive behavior can be identified? This includes things such as account lockout alerts, intrusion detections systems, virus alerting, intellectual property violations, etc.
Is there a software licensing inventory that provides the ability to effectively review and manage for license compliance and is there an ongoing process to review licenses? Is there a policy and/or standard that defines data retention requirements?
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 12
Answer Describe Existing Key Security Yes/No/Somewhat/N Controls Supporting This ot Applicable Question
Describe Key Weaknesses Relative to This Question
Describe any Current Projects Relative to This Question
Current Maturity Rating (Please read FAQ for definitions) 0 - Non Existent 1 - Initial / Ad-Hoc 2 - Repeatable but Intuitive
Primary Security Domain
Not Applicable
I. Security Policy
1
I. Security Policy I. Security Policy
I. Security Policy
I. Security Policy
I. Security Policy
I. Security Policy
I. Security Policy
II. Organizational Security
II. Organizational Security
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 13
Answer Describe Existing Key Security Yes/No/Somewhat/N Controls Supporting This ot Applicable Question
Describe Key Weaknesses Relative to This Question
Describe any Current Projects Relative to This Question
Current Maturity Rating (Please read FAQ for definitions) 0 - Non Existent 1 - Initial / Ad-Hoc 2 - Repeatable but Intuitive
Primary Security Domain
II. Organizational Security
II. Organizational Security
II. Organizational Security
II. Organizational Security
II. Organizational Security
II. Organizational Security
III. Asset Classification and Control
III. Asset Classification and Control III. Asset Classification and Control
III. Asset Classification and Control
III. Asset Classification and Control
III. Asset Classification and Control
IX. Access Control
IX. Access Control
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 14
Answer Describe Existing Key Security Yes/No/Somewhat/N Controls Supporting This ot Applicable Question
Describe Key Weaknesses Relative to This Question
Describe any Current Projects Relative to This Question
Current Maturity Rating (Please read FAQ for definitions) 0 - Non Existent 1 - Initial / Ad-Hoc 2 - Repeatable but Intuitive
Primary Security Domain
IX. Access Control
IX. Access Control
IX. Access Control
IX. Access Control
V. Physical and Environmental Security
VI. Equipment Security
VII. General Controls
VII. General Controls
VII. General Controls
VII. General Controls
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 15
Answer Describe Existing Key Security Yes/No/Somewhat/N Controls Supporting This ot Applicable Question
Describe Key Weaknesses Relative to This Question
Describe any Current Projects Relative to This Question
Current Maturity Rating (Please read FAQ for definitions) 0 - Non Existent 1 - Initial / Ad-Hoc 2 - Repeatable but Intuitive
Primary Security Domain
VII. General Controls
VII. General Controls
VII. General Controls
VII. General Controls
VII. General Controls
VII. General Controls
VIII. Communications & Operations Management
VIII. Communications & Operations Management
VIII. Communications & Operations Management VIII. Communications & Operations Management X. Systems Development and Maintenance
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 16
Answer Describe Existing Key Security Yes/No/Somewhat/N Controls Supporting This ot Applicable Question
Describe Key Weaknesses Relative to This Question
Describe any Current Projects Relative to This Question
Current Maturity Rating (Please read FAQ for definitions) 0 - Non Existent 1 - Initial / Ad-Hoc 2 - Repeatable but Intuitive
Primary Security Domain
X. Systems Development and Maintenance
X. Systems Development and Maintenance X. Systems Development and Maintenance
X. Systems Development and Maintenance
X. Systems Development and Maintenance
X. Systems Development and Maintenance
XI. Business Continuity
XI. Business Continuity
XI. Business Continuity
XI. Business Continuity
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 17
Answer Describe Existing Key Security Yes/No/Somewhat/N Controls Supporting This ot Applicable Question
Describe Key Weaknesses Relative to This Question
Describe any Current Projects Relative to This Question
Current Maturity Rating (Please read FAQ for definitions) 0 - Non Existent 1 - Initial / Ad-Hoc 2 - Repeatable but Intuitive
Primary Security Domain
XI. Business Continuity
XI. Business Continuity
XII. Compliance
XII. Compliance
XII. Compliance
XII. Compliance
Fusion Alliance, Inc. , University of Cincinnati Confidential
4/26/2012
Page 18
Security Control Maturity Rating Information Security Domains 0 - Non Existent I. Security Policy II. Organizational Security III. Asset Classification and Control IV. Personnel Security V. Physical and Environmental Security VI. Equipment Security VII. General Controls VIII. Communications & Operations Management IX. Access Control X. Systems Development and Maintenance XI. Business Continuity XII. Compliance 1 - Initial / Ad-Hoc 2 - Repeatable but Intuitive 3 - Defined Process 4 - Managed and Measurable 5 - Optimized
0 - Non-existent
Complete lack of any recognizable processes. The enterprise has not even recognized that there is an issue to be addressed.
1 - Initial
There is evidence that the enterprise has recognized that the issues exist and need to be addressed. There are, however, no standardized processes; instead there are ad hoc approaches that tend to be applied on an individual or case-by-case basis. The overall approach to management is disorganized.
2 - Repeatable
Processes have developed to the stage where similar procedures are followed by different people undertaking the same task. There is no formal training or communication of standard procedures, and responsibility is left to the individual. There is a high degree of reliance on the knowledge of individuals and, therefore, errors are likely.
3 - Defined
Procedures have been standardized and documented, and communicated through training. It is, however, left to the individual to follow these processes, and it is unlikely that deviations will be detected. The procedures themselves are not sophisticated but are the formalization of existing practices.
4 - Managed
It is possible to monitor and measure compliance with procedures and to take action where processes appear not to be working effectively. Processes are under constant improvement and provide good practice. Automation and tools are used in a limited or fragmented way.
5 - Optimized
Processes have been refined to a level of best practice, based on the results of continuous improvement and maturity modeling with other enterprises. IT is used in an integrated way to automate the workflow, providing tools to improve quality and effectiveness, making the enterprise quick to adapt .
PO1 Define a Strategic IT Plan 1.1 IT as Part of the Organizations Long and Short Range Plan 1.2 IT Long-range Plan 1.3 IT Long-range PlanningApproach and Structure 1.4 IT Long-range Plan Changes 1.5 Short-range Planning for the IT Function 1.6 Communication of IT Plans 1.7 Monitoring and Evaluating of IT Plans 1.8 Assessment of Existing Systems PO2 Define the Information Architecture 2.1 Information Architecture Model 2.2 Corporate Data Dictionary and Data Syntax Rules 2.3 Data Classification Scheme 2.4 Security Levels PO3 Determine Technological Direction 3.1 Technological Infrastructure Planning 3.2 Monitor Future Trends and Regulations 3.3 Technological Infrastructure Contingency 3.4 Hardware and Software Acquisition Plan 3.5 Technology Standards PO4 Define the IT Organization and Relationships 4.1 IT Planning or Steering Committee 4.2 Organizational Placement of the IT Function 4.3 Review of Organizational Achievements 4.4 Roles and Responsibilities 4.5 Responsibility for Quality Assurance 4.6 Responsibility for Logical and Physical Security 4.7 Ownership and Custodianship 4.8 Data and System Ownership 4.9 Supervision 4.10 Segregation of Duties 4.11 IT Staffing 4.12 Job or Position Descriptions for IT Staff 4.13 Key IT Personnel 4.14 Contracted Staff Policies and Procedures 4.15 Relationships PO5 Manage the IT Investment 5.1 Annual IT Operating Budget 5.2 Cost and Benefit Monitoring 5.3 Cost and Benefit Justification PO6 Communicate Management Aims and Direction 6.1 Positive Information Control Environment 6.2 Managements Responsibility for Policies 6.3 Communication of Organization Policies 6.4 Policy Implementation Resources 6.5 Maintenance of Policies 6.6 Compliance with Policies, Procedures and Standards 6.7 Quality Commitment 6.8 Security and Internal Control Framework Policy 6.9 Intellectual Property Rights 6.10 Issue-specific Policies 6.11 Communication of IT Security Awareness PO7 Manage Human Resources 7.1 Personnel Recruitment and Promotion 7.2 Personnel Qualifications 7.3 Roles and Responsibilities 7.4 Personnel Training 7.5 Cross-training or Staff Backup 7.6 Personnel Clearance Procedures 7.7 Employee Job Performance Evaluation 7.8 Job Change and Termination PO8 Ensure Compliance with External Requirements 8.1 External Requirements Review 8.2 Practices and Procedures for Complying with External Requirements 8.3 Safety and Ergonomic Compliance 8.4 Privacy, Intellectual Property and Data Flow 8.5 Electronic Commerce 8.6 Compliance With Insurance Contracts PO9 Assess Risks
9.1 Business Risk Assessment 9.2 Risk Assessment Approach 9.3 Risk Identification 9.4 Risk Measurement 9.5 Risk Action Plan 9.6 Risk Acceptance 9.7 Safeguard Selection 9.8 Risk Assessment Commitment PO10 Manage Projects 10.1 Project Management Framework 10.3 Project Team Membership and Responsibilities 10.4 Project Definition 10.5 Project Approval 10.6 Project Phase Approval 10.7 Project Master Plan 10.8 System Quality Assurance Plan 10.9 Planning of Assurance Methods 10.10 Formal Project Risk Management 10.11 Test Plan 10.12 Training Plan 10.13 Post-implementation Review Plan PO11 Manage Quality 11.1 General Quality Plan 11.2 Quality Assurance Approach 11.3 Quality Assurance Planning 11.4 Quality Assurance Review of Adherence to IT Standards and Procedures 11.5 System Development Life Cycle Methodology 11.6 System Development Life Cycle Methodology for Major Changes to Existing Technology 11.7 Updating of the System Development Life Cycle Methodology 11.8 Coordination and Communication 11.9 Acquisition and Maintenance Framework for the Technology Infrastructure 11.10 Third-party Implementer Relationships 11.11 Program Documentation Standards 11.12 Program Testing Standards 11.13 System Testing Standards 11.14 Parallel/Pilot Testing 11.15 System Testing Documentation 11.16 Quality Assurance Evaluation of Adherence to Development Standards 11.17 Quality Assurance Review of the Achievement of IT Objectives 11.18 Quality Metrics 11.19 Reports of Quality Assurance Reviews AI1 Identify Automated Solutions 1.1 Definition of Information Requirements 1.2 Formulation of Alternative Courses of Action 1.3 Formulation of Acquisition Strategy 1.4 Third-party Service Requirements 1.5 Technological Feasibility Study 1.6 Economic Feasibility Study 1.7 Information Architecture 1.8 Risk Analysis Report 1.9 Cost-effective Security Controls 1.10 Audit Trails Design 1.11 Ergonomics 1.12 Selection of System Software 1.13 Procurement Control 1.14 Software Product Acquisition 1.15 Third-party Software Maintenance 1.16 Contract Application Programming 1.17 Acceptance of Facilities 1.18 Acceptance of Technology AI2 Acquire and Maintain Application Software 2.1 Design Methods 2.2 Major Changes to Existing Systems 2.3 Design Approval 2.4 File Requirements Definition and Documentation 2.5 Program Specifications 2.6 Source Data Collection Design 2.7 Input Requirements Definition and Documentation 2.8 Definition of Interfaces
2.9 User-machine Interface 2.10 Processing Requirements Definition and Documentation 2.11 Output Requirements Definition and Documentation 2.12 Controllability 2.13 Availability as a Key Design Factor 2.14 IT Integrity Provisions in Application Program Software 2.15 Application Software Testing 2.16 User Reference and Support Materials 2.17 Reassessment of System Design AI3 Acquire and Maintain Technology Infrastructure 3.1 Assessment of New Hardware and Software 3.2 Preventive Maintenance for Hardware 3.3 System Software Security 3.4 System Software Installation 3.5 System Software Maintenance 3.6 System Software Change Controls 3.7 Use and Monitoring of System Utilities AI4 Develop and Maintain Procedures 4.1 Operational Requirements and Service Levels 4.2 User Procedures Manual 4.3 Operations Manual 4.4 Training Materials AI5 Install and Accredit Systems 5.1 Training 5.2 Application Software Performance Sizing 5.3 Implementation Plan 5.4 System Conversion 5.5 Data Conversion 5.6 Testing Strategies and Plans 5.7 Testing of Changes 5.8 Parallel/Pilot Testing Criteria and Performance 5.9 Final Acceptance Test 5.10 Security Testing and Accreditation 5.11 Operational Test 5.12 Promotion to Production 5.13 Evaluation of Meeting User Requirements 5.14 Managements Post-implementation Review AI6 Manage Changes 6.1 Change Request Initiation and Control 6.2 Impact Assessment 6.3 Control of Changes 6.4 Emergency Changes 6.5 Documentation and Procedures 6.6 Authorized Maintenance 6.7 Software Release Policy 6.8 Distribution of Software DS1 Define and Manage Service Levels 1.1 Service Level Agreement Framework 1.2 Aspects of Service Level Agreements 1.3 Performance Procedures 1.4 Monitoring and Reporting 1.5 Review of Service Level Agreements and Contracts 1.6 Chargeable Items 1.7 Service Improvement Program DS2 Manage Third-party Services 2.1 Supplier Interfaces 2.2 Owner Relationships 2.3 Third-party Contracts 2.4 Third-party Qualifications 2.5 Outsourcing Contracts 2.6 Continuity of Services 2.7 Security Relationships 2.8 Monitoring DS3 Manage Performance Capacity 3.1 Availability and Performance Requirements 3.2 Availability Plan 3.3 Monitoring and Reporting 3.4 Modeling Tools 3.5 Proactive Performance Management
3.6 Workload Forecasting 3.7 Capacity Management of Resources 3.8 Resources Availability 3.9 Resources Schedule DS4 Ensure Continuous Service 4.1 IT Continuity Framework 4.2 IT Continuity Plan Strategy and Philosophy 4.3 IT Continuity Plan Contents 4.4 Minimizing IT Continuity Requirements 4.5 Maintaining the IT Continuity Plan 4.6 Testing the IT Continuity Plan 4.7 IT Continuity Plan Training 4.8 IT Continuity Plan Distribution 4.9 User Department Alternative Processing Backup Procedures 4.10 Critical IT Resources 4.11 Backup Site and Hardware 4.12 Offsite Backup Storage 4.13 Wrap-up Procedures DS5 Ensure Systems Security 5.1 Manage Security Measures 5.2 Identification, Authentication and Access 5.3 Security of Online Access to Data 5.4 User Account Management 5.5 Management Review of User Accounts 5.6 User Control of User Accounts 5.7 Security Surveillance 5.8 Data Classification 5.9 Central Identification and Access Rights 5.10 Management Violation and Security Activity Reports 5.11 Incident Handling 5.12 Reaccreditation 5.13 Counterparty Trust 5.14 Transaction Authorization 5.15 Nonrepudiation 5.16 Trusted Path 5.17 Protection of Security Functions 5.18 Cryptographic Key Management 5.19 Malicious Software Prevention, Detection and Correction 5.20 Firewall Architectures and Connections with Public Networks 5.21 Protection of Electronic Value DS6 Identify and Allocate Costs 6.1 Chargeable Items 6.2 Costing Procedures 6.3 User Billing and Chargeback Procedures DS7 Educate and Train Users 7.1 Identification of Training Needs 7.2 Training Organization 7.3 Security Principles and Awareness Training DS8 Assist and Advise Customers 8.1 Help Desk 8.2 Registration of Customer Queries 8.3 Customer Query Escalation 8.4 Monitoring of Clearance 8.5 Trend Analysis and Reporting DS9 Manage the Configuration 9.1 Configuration Recording 9.2 Configuration Baseline 9.3 Status Accounting 9.4 Configuration Control 9.5 Unauthorized Software 9.6 Software Storage 9.7 Configuration Management Procedures 9.8 Software Accountability DS10 Manage Problems and Incidents 10.1 Problem Management System 10.2 Problem Escalation 10.3 Problem Tracking and Audit Trail 10.4 Emergency and Temporary Access Authorization 10.5 Emergency Processing Priorities
DS11 Manage Data 11.1 Data Preparation Procedures 11.2 Source Document Authorization Procedures 11.3 Source Document Data Collection 11.4 Source Document Error Handling 11.5 Source Document Retention 11.6 Data Input Authorization Procedures 11.7 Accuracy, Completeness and Authorization Checks 11.8 Data Input Error Handling 11.9 Data Processing Integrity 11.10 Data Processing Validation and Editing 11.11 Data Processing Error Handling 11.12 Output Handling and Retention 11.13 Output Distribution 11.14 Output Balancing and Reconciliation 11.15 Output Review and Error Handling 11.16 Security Provision for Output Reports 11.17 Protection of Sensitive Information During Transmission and Transport 11.18 Protection of Disposed Sensitive Information 11.19 Storage Management 11.20 Retention Periods and Storage Terms 11.21 Media Library Management System 11.22 Media Library Management Responsibilities 11.23 Backup and Restoration 11.24 Backup Jobs 11.25 Backup Storage 11.26 Archiving 11.27 Protection of Sensitive Messages 11.28 Authentication and Integrity 11.29 Electronic Transaction Integrity 11.30 Continued Integrity of Stored Data DS12 Manage Facilities 12.1 Physical Security 12.2 Low Profile of the IT Site 12.3 Visitor Escort 12.4 Personnel Health and Safety 12.5 Protection Against Environmental Factors 12.6 Uninterruptible Power Supply DS13 Manage Operations 13.1 Processing Operations Procedures and Instructions Manual 13.2 Start-up Process and Other Operations Documentation 13.3 Job Scheduling 13.4 Departures from Standard Job Schedules 13.5 Processing Continuity 13.6 Operations Logs 13.7 Safeguard Special Forms and Output Devices 13.8 Remote Operations M1 Monitor the Processes 1.1 Collecting Monitoring Data 1.2 Assessing Performance 1.3 Assessing Customer Satisfaction 1.4 Management Reporting M2 Assess Control Adequacy 2.1 Internal Control Monitoring 2.2 Timely Operation of Internal Controls 2.3 Internal Control Level Reporting 2.4 Operational Security and Internal Control Assurance M3 Obtain Independent Assurance 3.1 Independent Security and Internal Control Certification/Accreditation of IT Services 3.2 Independent Security and Internal Control Certification/Accreditation of Third-party Service Providers 3.3 Independent Effectiveness Evaluation of IT Services 3.4 Independent Effectiveness Evaluation of Third-party Service Providers 3.5 Independent Assurance of Compliance with Laws and Regulatory Requirements and Contractual Commitments 3.6 Independent Assurance of Compliance with Laws and Regulatory Requirements by Third-party Service Providers 3.7 Competence of Independent Assurance Function 3.8 Proactive Audit Involvement M4 Provide for Independent Audit 4.1 Audit Charter 4.2 Independence
4.3 Professional Ethics and Standards 4.4 Competence 4.5 Planning 4.6 Performance of Audit Work 4.7 Reporting 4.8 Follow-up Activities
3 SECURITY POLICY 3.1 INFORMATION SECURITY POLICY 3.1.1 Information security policy document 3.1.2 Review and evaluation 4 ORGANIZATIONAL SECURITY 4.1 INFORMATION SECURITY INFRASTRUCTURE 4.1.1 Management information security forum 4.1.2 Information security co-ordination 4.1.3 Allocation of information security responsibilities 4.1.4 Authorization process for information processing facilities 4.1.5 Specialist information security advice 4.1.6 Co-operation between organizations 4.1.7 Independent review of information security 4.2 SECURITY OF THIRD PARTY ACCESS 4.2.1 Identification of risks from third party access 4.2.2 Security requirements in third party contracts 4.3 OUTSOURCING 4.3.1 Security requirements in outsourcing contracts 5 ASSET CLASSIFICATION AND CONTROL 5.1 ACCOUNTABILITY FOR ASSETS 5.1.1 Inventory of assets 5.2 INFORMATION CLASSIFICATION 5.2.1 Classification guidelines 5.2.2 Information labelling and handling 6 PERSONNEL SECURITY 6.1 SECURITY IN JOB DEFINITION AND RESOURCING 6.1.1 Including security in job responsibilities 6.1.2 Personnel screening and policy 6.1.3 Confidentiality agreements 6.1.4 Terms and conditions of employment 6.2 USER TRAINING 6.2.1 Information security education and training 6.3 RESPONDING TO SECURITY INCIDENTS AND MALFUNCTIONS 6.3.1 Reporting security incidents 6.3.2 Reporting security weaknesses 6.3.3 Reporting software malfunctions 6.3.4 Learning from incidents 6.3.5 Disciplinary process 7 PHYSICAL AND ENVIRONMENTAL SECURITY 7.1 SECURE AREAS 7.1.1 Physical security perimeter 7.1.2 Physical entry controls 7.1.3 Securing offices, rooms and facilities 7.1.4 Working in secure areas 7.1.5 Isolated delivery and loading areas 7.2 EQUIPMENT SECURITY 7.2.1 Equipment siting and protection 7.2.2 Power supplies 7.2.3 Cabling security 7.2.4 Equipment maintenance 7.2.5 Security of equipment off-premises 7.2.6 Secure disposal or re-use of equipment
7.3 GENERAL CONTROLS 7.3.1 Clear desk and clear screen policy 7.3.2 Removal of property 8 COMMUNICATIONS AND OPERATIONS MANAGEMENT 8.1 OPERATIONAL PROCEDURES AND RESPONSIBILITIES 8.1.1 Documented operating procedures 8.1.2 Operational change control 8.1.3 Incident management procedures 8.1.4 Segregation of duties 8.1.5 Separation of development and operational facilities 8.1.6 External facilities management 8.2 SYSTEM PLANNING AND ACCEPTANCE 8.2.1 Capacity planning 8.2.2 System acceptance 8.3 PROTECTION AGAINST MALICIOUS SOFTWARE 8.3.1 Controls against malicious software 8.4 HOUSEKEEPING 8.4.1 Information back-up 8.4.2 Operator logs 8.4.3 Fault logging 8.5 NETWORK MANAGEMENT 8.5.1 Network controls 8.6 MEDIA HANDLING AND SECURITY 8.6.1 Management of removable computer media 8.6.2 Disposal of media 8.6.3 Information handling procedures 8.6.4 Security of system documentation 8.7 EXCHANGES OF INFORMAT ION AND SOFTWARE 8.7.1 Information and software exchange agreements 8.7.2 Security of media in transit 8.7.3 Electronic commerce security 8.7.4 Security of electronic mail 8.7.5 Security of electronic office systems 8.7.6 Publicly available systems 8.7.7 Other forms of information exchange 9 ACCESS CONTROL 9.1 BUSINESS REQUIREMENT FOR ACCESS CONTROL 9.1.1 Access control policy 9.2 USER ACCESS MANAGEMENT 9.2.1 User registration 9.2.2 Privilege management 9.2.3 User password management 9.2.4 Review of user access rights 9.3 USER RESPONSIBILITIES 9.3.1 Password use 9.3.2 Unattended user equipment 9.4 NETWORK ACCESS CONTROL 9.4.1 Policy on use of network services 9.4.2 Enforced path 9.4.3 User authentication for external connections 9.4.4 Node authentication 9.4.5 Remote diagnostic port protection
9.4.6 Segregation in networks 9.4.7 Network connection control 9.4.8 Network routing control 9.4.9 Security of network services 9.5 OPERATING SYSTEM ACCE SS CONTROL 9.5.1 Automatic terminal identification 9.5.2 Terminal log-on procedures 9.5.3 User identification and authentication 9.5.4 Password management system 9.5.5 Use of system utilities 9.5.6 Duress alarm to safeguard users 9.5.7 Terminal time-out 9.5.8 Limitation of connection time 9.6 APPLICATION ACCESS CONTROL 9.6.1 Information access restriction 9.6.2 Sensitive system isolation 9.7 MONITORING SYSTEM ACCESS AND USE 9.7.1 Event logging 9.7.2 Monitoring system use 9.7.3 Clock synchronization 9.8 MOBILE COMPUTING AND TELEWORKING 9.8.1 Mobile computing 9.8.2 Teleworking 10 SYSTEMS DEVELOPMENT AND MAINTENANCE 10.1 SECURITY REQUIREMENTS OF SYSTEMS 10.1.1 Security requirements analysis and specification 10.2 SECURITY IN APPLICATION SYSTEMS 10.2.1 Input data validation 10.2.2 Control of internal processing 10.2.3 Message authentication 10.2.4 Output data validation 10.3 CRYPTOGRAPHIC CONTROLS 10.3.1 Policy on the use of cryptographic controls 10.3.2 Encryption 10.3.3 Digital signatures 10.3.4 Non-repudiation services 10.3.5 Key management 10.4 SECURITY OF SYSTEM FILES 10.4.1 Control of operational software 10.4.2 Protection of system test data 10.4.3 Access control to program source library 10.5 SECURITY IN DEVELOPMENT AND SUPPORT PROCE SSES 10.5.1 Change control procedures 10.5.2 Technical review of operating system changes 10.5.3 Restrictions on changes to software packages 10.5.4 Covert channels and Trojan code 10.5.5 Outsourced software development 11 BUSINESS CONTINUITY MANAGEMENT 11.1 ASPECTS OF BUSINESS CONTINUITY MANAGEMENT 11.1.1 Business continuity management process 11.1.2 Business continuity and impact analysis 11.1.3 Writing and implementing continuity plans
11.1.4 Business continuity planning framework 11.1.5 Testing, maintaining and re-assessing business continuity plans 12 COMPLIANCE 12.1 COMPLIANCE WITH LEGAL REQUIREMENTS 12.1.1 Identification of applicable legislation 12.1.2 Intellectual property rights (IPR) 12.1.3 Safeguarding of organizational records 12.1.4 Data protection and privacy of personal information 12.1.5 Prevention of misuse of information processing facilities 12.1.6 Regulation of cryptographic controls 12.1.7 Collection of evidence 12.2 REVIEWS OF SECURITY P OLICY AND TECHNICAL COMPLIANCE 12.2.1 Compliance with security policy 12.2.2 Technical compliance checking 12.3 SYSTEM AUDIT CONSIDERATIONS 12.3.1 System audit controls 12.3.2 Protection of system audit tools
3 The management system 3.1 Management and Responsibility 3.2 Documentation requirements 3.3 Competence, awareness and training 3.3.1 General 3.3.2 Professional development 3.3.3 Approaches to be considered 4 Planning and implementing service management 4.1 Plan service management (Plan) 4.1.1 Scope of service Management 4.1.2 Planning approaches 4.1.3 Events to be considered 4.1.4 Scope and contents of the plan 4.2 Implement service management and provide the services 4.3 Monitoring, measuring and reviewing (Check) 4.4 COntinual improvement (Act) 4.4.1 Policy 4.4.2 Planning for service improvements 5 Planning and implementing new or changed services 5.1 Topics for consideration 5.2 Change records 6 Service delivery process 6.1 Service level management 6.1.1 Service catalogue 6.1.2 Service level agreements (SLAs) 6.1.3 Service level management (SLM) process 6.1.4 Supporting service agreements 6.2 Service reporting 6.2.1 Policy 6.2.2 Purpose and quality checks on service reports 6.2.3 Service reports 6.3 Service continuity and availability management 6.3.1 General 6.3.2 Availability monitoring and activities 6.3.3 Service continuity strategy 6.3.4 Service continuity planning and testing 6.4 Budgeting and accounting for IT services 6.4.1 General 6.4.2 Policy 6.4.3 Budgeting 6.4.4 Accounting 6.5 Capacity management 6.6 Information security management 6.6.1 General 6.6.2 Identifying and classifying information assets 6.6.3 Seruciry risk assessment practices 6.6.4 Risks to information assets 6.6.5 Security and availability of information 6.6.6 Controls 6.6.7 Documents and records 7 Relationship processes 7.1 General
7.2 Business relationship management 7.2.1 Service reviews 7.2.2 Service complaints 7.2.3 Customer satisfaction measurement 7.3 Supplier management 7.3.1 Introduction 7.3.2 Contract management 7.3.3 Service definition 7.3.4 Manageing multiple suppliers 7.3.5 Contractual disputes management 7.3.6 Contract end 8 Resolution processes 8.1 Background 8.1.1 Setting priorities 8.1.2 Workarounds 8.2 Incident management 8.2.1 General 8.2.2 Major incidents 8.3 Problem management 8.3.1 Scope of problem management 8.3.2 Initiation of problem management 8.3.3 Known errors 8.3.4 Problem resolution management 8.3.5 Communication 8.3.6 Tracking and escalation 8.3.7 Incident and problem record closure 8.3.8 Problem reviews 8.3.9 Topics for reviews 8.3.10 Problem prevention 9 Control processes 9.1 Configuratin management 9.1.1 Configuration management planning and implementation 9.1.2 Configuration identification 9.1.3 Configuration control 9.1.4 Configuration status accounting and reporting 9.1.5 Configuration verification and audit 9.2 Change management 9.2.1 Planning and implementation 9.2.2 Closing and reviewing the change request 9.2.3 Emergency changes 9.2.4 Change management reporting, analysis and actions 10 Release process 10.1 Release management process 10.1.1 General 10.1.2 Release policy 10.1.3 Release and roll-out planning 10.1.4 Developing or acquiring software 10.1.5 Design, uild and configure release 10.1.6 Release verification and acceptance 10.1.7 Documentation 10.1.8 Roll-out, distribution and installation 10.1.9 Post release and roll-out
También podría gustarte
- COBIT 4 To 5 MappingDocumento22 páginasCOBIT 4 To 5 MappingSigula Galuh100% (2)
- BAI09 Manage Assets Audit Assurance Program - Icq - Eng - 1014Documento28 páginasBAI09 Manage Assets Audit Assurance Program - Icq - Eng - 1014Ferry100% (1)
- COBIT 2019 - RACI by Role - April 2020Documento295 páginasCOBIT 2019 - RACI by Role - April 2020gaston6711100% (1)
- ITIL Edition 2011 - COBIT 5 - Mapping Glenfis AG v1.2Documento1 páginaITIL Edition 2011 - COBIT 5 - Mapping Glenfis AG v1.2otnawrupAún no hay calificaciones
- Cobit 2019 Design ImplementationDocumento1 páginaCobit 2019 Design ImplementationParvez2z0% (1)
- BS EN 50128 Searchable PDFDocumento134 páginasBS EN 50128 Searchable PDFSyed Muhammad Ali Omer100% (3)
- COBIT® 2019 Governance System Design Workbook-Instructions: Terms & DefinitionsDocumento60 páginasCOBIT® 2019 Governance System Design Workbook-Instructions: Terms & DefinitionsFernando Moura25% (4)
- ISO27001 Vs ITGCDocumento13 páginasISO27001 Vs ITGCAtulOsave100% (1)
- SOC 1 GuideDocumento195 páginasSOC 1 GuideSreekar100% (2)
- Software Installation Instructions For The Carestream Image Suite V4 SoftwareDocumento18 páginasSoftware Installation Instructions For The Carestream Image Suite V4 Softwaresuny1982100% (1)
- COBIT 2019 - ISO 27001 (2013 - 14 - 15) CrossoverDocumento66 páginasCOBIT 2019 - ISO 27001 (2013 - 14 - 15) CrossoverYanto100% (1)
- Student Guide: COBIT® 2019 Design & ImplementationDocumento10 páginasStudent Guide: COBIT® 2019 Design & Implementationsamir sahliAún no hay calificaciones
- Isaca: Cobit Assessment Programme (PAM) Tool Kit: Using COBIT 5Documento2 páginasIsaca: Cobit Assessment Programme (PAM) Tool Kit: Using COBIT 5lgaleanoc0% (1)
- COBIT® 2019 Governance System Design Workbook-Instructions: Terms & DefinitionsDocumento60 páginasCOBIT® 2019 Governance System Design Workbook-Instructions: Terms & DefinitionsJani67% (3)
- Getting Started With Geit - RESDocumento52 páginasGetting Started With Geit - RESnicolepetrescu100% (2)
- IT Control Objectives For Sarbanes-OxleyDocumento12 páginasIT Control Objectives For Sarbanes-OxleyDiego VergaraAún no hay calificaciones
- COBIT 5 IntroductionDocumento6 páginasCOBIT 5 Introductiondan27090% (1)
- COBIT - 188 QuestionsDocumento64 páginasCOBIT - 188 QuestionsGuillaume-David Teboko100% (2)
- Gap Assessment Template ISO 27001 ISO 27002Documento145 páginasGap Assessment Template ISO 27001 ISO 27002santuchetu1Aún no hay calificaciones
- Assurance COBIT2019Documento51 páginasAssurance COBIT2019Kumar Puvanes Tharumalingam100% (1)
- IS Auditing Tools and Tech - Res - Eng - 0215 PDFDocumento46 páginasIS Auditing Tools and Tech - Res - Eng - 0215 PDFcecil_jrAún no hay calificaciones
- COBIT2019 - Foundation Course - PG - V1.1Documento17 páginasCOBIT2019 - Foundation Course - PG - V1.1moonsports100% (1)
- Courier Management System ProjectDocumento72 páginasCourier Management System ProjectMirshad Rahman100% (3)
- People and Organisational DocumentDocumento11 páginasPeople and Organisational DocumentRavi RamanAún no hay calificaciones
- The Components of The IT Audit Report - Joa - Eng - 0120 PDFDocumento4 páginasThe Components of The IT Audit Report - Joa - Eng - 0120 PDFImmanuel GiuleaAún no hay calificaciones
- COBIT 5 Implementation IntroductionDocumento6 páginasCOBIT 5 Implementation IntroductionJavier Torres Solis25% (4)
- Using COBIT and ITIL To Implement IT GovernanceDocumento58 páginasUsing COBIT and ITIL To Implement IT GovernancejlfloridodAún no hay calificaciones
- Checklist of Mandatory Documentation Required by ISO/IEC 20000-1:2018Documento18 páginasChecklist of Mandatory Documentation Required by ISO/IEC 20000-1:2018Anas Abu HijailAún no hay calificaciones
- ISO 20000 - 1 2018 Transition Checklist 1 1Documento10 páginasISO 20000 - 1 2018 Transition Checklist 1 1Carlos Arley Gonzalez Rocha100% (4)
- Cobit 2019 Design-Implementation Course Syllabus - New Look 2019 EN V1.0Documento13 páginasCobit 2019 Design-Implementation Course Syllabus - New Look 2019 EN V1.0Dipayan Chakraborty100% (1)
- COBIT 2019 Foundation ExamDocumento28 páginasCOBIT 2019 Foundation ExamVitor Suzarte100% (1)
- Developing The IT Audit Plan Using COBIT 2019Documento11 páginasDeveloping The IT Audit Plan Using COBIT 2019吴rua歌Aún no hay calificaciones
- COBIT-2019 RACI-By-role April 2020 v2Documento279 páginasCOBIT-2019 RACI-By-role April 2020 v2yi wangAún no hay calificaciones
- COBIT 2019 DESIGN-IMPLEMENTATION COURSE INHOUSEv1 PDFDocumento4 páginasCOBIT 2019 DESIGN-IMPLEMENTATION COURSE INHOUSEv1 PDFEarl RaisAún no hay calificaciones
- ISO 20000 Master List of DocumentsDocumento1 páginaISO 20000 Master List of DocumentsAditya YerunkarAún no hay calificaciones
- New Changes in ISO 20000-1:2018 Standard: Presented By: Neha MatharuDocumento12 páginasNew Changes in ISO 20000-1:2018 Standard: Presented By: Neha MatharuRaviAún no hay calificaciones
- COBIT 2019 Framework Introduction and Methodology - Res - Eng - 1118 PDFDocumento64 páginasCOBIT 2019 Framework Introduction and Methodology - Res - Eng - 1118 PDFcyberpcgtAún no hay calificaciones
- ExamDocumento16 páginasExamCarlos F. Núñez100% (1)
- COBIT 2019 Major Differences With COBIT 5Documento12 páginasCOBIT 2019 Major Differences With COBIT 5Parvez2zAún no hay calificaciones
- Assessment Report Template (Appendix D3)Documento7 páginasAssessment Report Template (Appendix D3)Laura Intan100% (1)
- COBIT 2019 - Management-Awareness-Diagnostic - v1.0Documento4 páginasCOBIT 2019 - Management-Awareness-Diagnostic - v1.0Paul Vintimilla CarrascoAún no hay calificaciones
- Enterprise GoalsDocumento5 páginasEnterprise GoalsMario ValladaresAún no hay calificaciones
- Using ITIL 4 and COBIT 2019 To Create Integrated Framework - Whpitilcb - WHP - Eng - 0621Documento10 páginasUsing ITIL 4 and COBIT 2019 To Create Integrated Framework - Whpitilcb - WHP - Eng - 0621Diego MaradeiAún no hay calificaciones
- IT Audit - FrameworkDocumento20 páginasIT Audit - FrameworkAbi SyukriAún no hay calificaciones
- Handout - IsAE 3402Documento9 páginasHandout - IsAE 3402professional.ca728Aún no hay calificaciones
- ISO 20000-1 2011 Audit ChecklistDocumento10 páginasISO 20000-1 2011 Audit Checklistjoelc5840% (1)
- COBIT 5 For Risk Laminate Res Eng 0913Documento8 páginasCOBIT 5 For Risk Laminate Res Eng 0913dandisdandisAún no hay calificaciones
- COBIT 5 Foundation Exam Revision On A PageDocumento1 páginaCOBIT 5 Foundation Exam Revision On A PageSergiö Montoya100% (1)
- COBIT 5 Process Assessment ModelDocumento18 páginasCOBIT 5 Process Assessment ModelpiermeAún no hay calificaciones
- InfoSystemsAuditChecklist (Version 1)Documento44 páginasInfoSystemsAuditChecklist (Version 1)Merrick Martin100% (1)
- NIST CSF Risk CMM-2017 EmptyDocumento19 páginasNIST CSF Risk CMM-2017 EmptyLuisAún no hay calificaciones
- Audit ChecklistDocumento14 páginasAudit ChecklistARRY WIDODOAún no hay calificaciones
- COBIT 5-Self-Assessment Templates - BAI - 25 August 2015Documento97 páginasCOBIT 5-Self-Assessment Templates - BAI - 25 August 2015sannyAún no hay calificaciones
- Cgeit NotesDocumento2 páginasCgeit NotesKaye Akin25% (4)
- ISO/IEC 38500: The IT Governance StandardDe EverandISO/IEC 38500: The IT Governance StandardCalificación: 4.5 de 5 estrellas4.5/5 (2)
- IT Governance to Drive High Performance: Lessons from AccentureDe EverandIT Governance to Drive High Performance: Lessons from AccentureAún no hay calificaciones
- Information Systems Auditing: The IS Audit Planning ProcessDe EverandInformation Systems Auditing: The IS Audit Planning ProcessCalificación: 3.5 de 5 estrellas3.5/5 (2)
- CRM Vtiger 10.36.43.2Documento4 páginasCRM Vtiger 10.36.43.2Duong KaiAún no hay calificaciones
- Nessus ScriptDocumento1 páginaNessus Scriptapi-385391462Aún no hay calificaciones
- Advertising Data AnalysisDocumento12 páginasAdvertising Data AnalysisVishal SharmaAún no hay calificaciones
- Set Up PostgreSQL 9.5 Master-Slave Replication Using Repmgr Edward Samuel's BlogDocumento5 páginasSet Up PostgreSQL 9.5 Master-Slave Replication Using Repmgr Edward Samuel's BlogAymenAún no hay calificaciones
- Bugreport Alioth - Id RKQ1.200826.002 2022 06 20 21 15 13 Dumpstate - Log 9162Documento34 páginasBugreport Alioth - Id RKQ1.200826.002 2022 06 20 21 15 13 Dumpstate - Log 9162Setyo WatiAún no hay calificaciones
- Creo 3.0 JlinkugDocumento482 páginasCreo 3.0 JlinkugyuvarajaAún no hay calificaciones
- DRAFT - IT Policies and Procedure - v4.0Documento25 páginasDRAFT - IT Policies and Procedure - v4.0norliana mananAún no hay calificaciones
- Tutorial SolidWorks (AA)Documento1039 páginasTutorial SolidWorks (AA)Abrianto Akuan100% (2)
- Bulleted Lists in Moderncv Cventry - TeX - LaTeX Stack ExchangeDocumento4 páginasBulleted Lists in Moderncv Cventry - TeX - LaTeX Stack Exchangealanpicard2303Aún no hay calificaciones
- dr-600 ManualDocumento24 páginasdr-600 ManualabhiarvindAún no hay calificaciones
- SSL CiphersDocumento4 páginasSSL CiphersJetbar Dolok SaribuAún no hay calificaciones
- MD8470A OverviewDocumento16 páginasMD8470A OverviewSuman RoyAún no hay calificaciones
- Da Test 2Documento68 páginasDa Test 2Kshitija WaruleAún no hay calificaciones
- Chap 2 - AssemblersDocumento50 páginasChap 2 - AssemblersParth Manoj Kumar100% (1)
- SI1Documento34 páginasSI1ajmainAún no hay calificaciones
- Manual MyCloudPR4100 PDFDocumento125 páginasManual MyCloudPR4100 PDFAhmad RidhoAún no hay calificaciones
- Muhammad Ezzat Bin Mohd SapianDocumento2 páginasMuhammad Ezzat Bin Mohd SapianMuhammad EzzatAún no hay calificaciones
- VitaeDocumento3 páginasVitaeHector Gomez MoralesAún no hay calificaciones
- SAS94 9CHKJ3 12001364 Win WRKSTNDocumento3 páginasSAS94 9CHKJ3 12001364 Win WRKSTNSiti DamayantiAún no hay calificaciones
- SYLLABUSDocumento2 páginasSYLLABUSManoj DhawaleAún no hay calificaciones
- Aq300 Series Flyer En1.1Documento2 páginasAq300 Series Flyer En1.1Alexandre MorenoAún no hay calificaciones
- Java Fundamentals: Activity Guide X95176GC10 Edition 1.0 - October 2016Documento170 páginasJava Fundamentals: Activity Guide X95176GC10 Edition 1.0 - October 2016Costin Davidescu100% (1)
- Madhavi NETDocumento9 páginasMadhavi NETKhader ShaikAún no hay calificaciones
- External Commands: ATTRIB CommandDocumento5 páginasExternal Commands: ATTRIB Commandrahulravi4uAún no hay calificaciones
- Designjet Universal Print Driver: System Administrator's GuideDocumento40 páginasDesignjet Universal Print Driver: System Administrator's Guidevodito86Aún no hay calificaciones
- ABAP Internal Table DeclarationDocumento21 páginasABAP Internal Table Declarationharish_inAún no hay calificaciones
- Guide To Hacking With Sub7Documento2 páginasGuide To Hacking With Sub7ReeGast BenedictAún no hay calificaciones