Documentos de Académico
Documentos de Profesional
Documentos de Cultura
University Questions
Cargado por
Vasantha KumariDescripción original:
Derechos de autor
Formatos disponibles
Compartir este documento
Compartir o incrustar documentos
¿Le pareció útil este documento?
¿Este contenido es inapropiado?
Denunciar este documentoCopyright:
Formatos disponibles
University Questions
Cargado por
Vasantha KumariCopyright:
Formatos disponibles
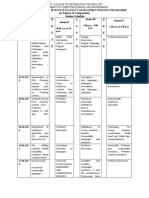
Cryptography and Network Security Appendix B - University Question Papers
B.E./B.TECH. DEGREE EXAMINATION, NOVEMBER/DECEMBER 2014
SEVENTH SEMESTER - COMPUTER SCIENCE AND ENGINEERING
IT2352/IT 62 CRYPTOGRAPHY AND NETWORK SECURITY
(Common to Information Technology – Sixth Semester)
(Regulation 2008)
Part A
1. Decipher the following cipher text using brute force attack:
CMTMROOEOORW (Hint: Algorithm – Railfence)
2. What are the two basic functions used in encryption algorithms?
3. Point out the types of cryptanalytic attacks.
4. What are the performance differences between MD5, SHA-512 and RIPEMD-160?
5. Is it possible to use the DES algorithm, to generate message authentication code? Justify.
6. What are the protocols used to provide IP security?
7. List the difference between stream and block cipher.
8. What are the security services provided by Digital Signature?
9. Differentiate macro virus and boot virus.
10. Sketch the general format for PGP message.
Part B
11. (a) Encrypt the message “PAY” using Hill cipher with the following key matrix and show
the decryption to get the original plain text.
17 17 5
K= 21 18 21
2 2 19
(OR)
(b) Write short notes on:
(i) Fermat and Euler’s Theorem
(ii) Chinese Remainder Theorem
12. (a) Brief out the encryption and decryption process of DES and depict the general
structures. List out the strengths and weaknesses of the same.
(OR)
Prepared by P.Vasantha Kumari 303
Cryptography and Network Security Appendix B - University Question Papers
(b) Describe the mathematical foundations of RSA algorithm. Perform encryption and
decryption for the following:
p = 17, q = 7, e = 5, n = 119, message = “6”
Use Extended Euclid’s algorithm to find out the private key.
13. (a) Explain the process of deriving eighty 64-bit words from the 1024-bits for
processing of a single block and also discuss single round function in SHA-521 algorithm.
Show the values of W16, W17, W18, and W19.
(OR)
(b) Explain Diffie-Hellman Key exchange algorithm with an example. Consider a Diffie-
Hellman scheme with a common prime q = 353, and a primitive root α = 3. Users A and B
have private keys XA = 17, XB = 21 respectively. What is the shared secret key K1 and K2?
14. (a) Alice chooses Q = 101 and P = 7879. Assume (q, p, g and y): Alice’s Public Key. Alice
selects h = 3 and calculates g. Alice chooses x =75 as the private key and calculates y. Now,
Alice can send a message to Bob. Assume that H(M) = 22 and Alice choose secret no K = 50.
Verify the Signature.
(OR)
(b) For what purpose Zimmerman developed PGP? Brief the various services provided
by PGP. Discuss the threats faced by an e-mail and explain its security requirements to
provide a secure e-mail service.
15. (a) Explain NIST and VISA International Security Models and list the evaluation criteria
set by it.
(OR)
(b) Discuss the architecture of distributed intrusion detection system with the
necessary diagrams. Illustrate the three common types of firewalls with diagram.
Prepared by P.Vasantha Kumari 304
Cryptography and Network Security Appendix B - University Question Papers
B.E./B.TECH. DEGREE EXAMINATION, MAY/JUNE 2014
SEVENTH SEMESTER - COMPUTER SCIENCE AND ENGINEERING
IT2352/IT 62 CRYPTOGRAPHY AND NETWORK SECURITY
(Common to Information Technology – Sixth Semester)
(Regulation 2008)
Part A
1. What are active and passive attacks that compromise information security?
2. Why random numbers are used in network security?
3. State Euler’s theorem.
4. What is Optimal Asymmetric Encryption Padding?
5. What is Discrete logarithm problem?
6. State whether symmetric and asymmetric cryptographic algorithms need key Exchange.
7. List the authentication requirements.
8. What are birthday attacks?
9. Differentiate spyware and virus.
10. What are zombies?
Part B
11. (a) Explain any two classical ciphers and also describe their security limitations.
(OR)
(b) Describe Linear Feedback Shift Registers Sequences and Finite Fields with their
applications in cryptography.
12. (a) Describe the working principle of Simple DES with an example.
(OR)
(b) (i) Explain RSA algorithm.
(ii) Demonstrate encryption and decryption for the RSA algorithm parameters: p =
3, q = 11, e = 7, d = ?, M = 5.
13. (a) Explain Digital Signature Standard.
(OR)
Prepared by P.Vasantha Kumari 305
Cryptography and Network Security Appendix B - University Question Papers
(b) (i) Briefly explain Diffie-Hellman Key Exchange.
(ii) Users A and B use the Diffie-Hellman key exchange technique with a common
prime q = 71 and a primitive root α = 7. If user A has private key X A = 5, what is A’s public
key YA?
14. (a) Elaborately explain Kerberos authentication mechanism with suitable diagrams.
(OR)
(b) Explain Pretty Good Privacy in detail.
15. (a) Explain statistical anomaly detection and rule based intrusion detection.
(OR)
(b) Describe any two advanced anti-virus techniques in detail.
Prepared by P.Vasantha Kumari 306
Cryptography and Network Security Appendix B - University Question Papers
B.E./B.TECH. DEGREE EXAMINATION, NOVEMBER/DECEMBER 2013
SEVENTH SEMESTER - COMPUTER SCIENCE AND ENGINEERING
IT2352/IT 62 CRYPTOGRAPHY AND NETWORK SECURITY
(Common to Information Technology – Sixth Semester)
(Regulation 2008)
Part A
1. Give an example each for substitution and transposition ciphers.
2. Why modular arithmetic has been used in cryptography?
3. What are the modes of DES?
4. List the uses of RC4.
5. Write any two differences between MD4 and secure hash algorithm.
6. How digital signature is different from conventional? Give any two.
7. Define: SET.
8. What do you mean by PGP?
9. What are the effects of malicious software? Write any two.
10. What is Worm?
Part B
11. (a) (i) What are the different types of attacks? Explain. (8)
(ii) State and explain Chinese remainder Theorem with example. (8)
(OR)
(b) (i) State Fermat’s Theorem. (4)
(ii) Find 321 mod 11 using Fermat’s theorem. (6)
(iii) State Euler’s theorem to find gcd with example. (6)
12. (a) Write down the Triple DES algorithm and explain with neat diagram.
(OR)
(b) Explain about the RSA algorithm with example as:
p = 11, q = 5, e = 3 and PT = 9.
Prepared by P.Vasantha Kumari 307
Cryptography and Network Security Appendix B - University Question Papers
13. (a) (i) Define a hashing function. (2)
(ii) What are the properties of hashing function in cryptography? (6)
(iii) Explain Secure Hashing Algorithm (SHA). (8)
(OR)
(b) (i) Illustrate about the Birthday attacks. (8)
(ii) Explain digital signature with ElGamal public key cryptosystem. (8)
14. (a) Write short notes about
(i) Web Security (8)
(ii) SSL (8)
(OR)
(b) Explain about the PKI.
15. (a) Explain about the Security standards.
(OR)
(b) Write short notes on
(i) Firewalls
(ii) Viruses
Prepared by P.Vasantha Kumari 308
Cryptography and Network Security Appendix B - University Question Papers
B.E./B.TECH. DEGREE EXAMINATION, MAY/JUNE 2013
SEVENTH SEMESTER - COMPUTER SCIENCE AND ENGINEERING
IT2352/IT 62 CRYPTOGRAPHY AND NETWORK SECURITY
(Common to Information Technology – Sixth Semester)
(Regulation 2008)
Part A
1. Convert the given text “anna university” into cipher text using rail fence technique.
2. Define steganography.
3. What is the disadvantage with ECB mode of operation?
4. Find GCD(21, 300) using Euclid’s algorithm.
5. Define discrete logarithm.
6. What is weak collision resistance? What is the use of it?
7. List out the services provided by PGP.
8. Expand and define SPI.
9. Mention the two levels of hackers.
10. What is logic bomb?
Part B
11. (a) Write about any two classical crypto systems (substitution and transposition) with
suitable example.
(OR)
(b) Write about Fermat’s and Euler’s Theorem in detail.
12. (a) Explain briefly about DES in detail.
(OR)
(b) Explain about RSA with one suitable example.
13. (a) Explain about secure hash algorithm (SHA) in detail.
Prepared by P.Vasantha Kumari 309
Cryptography and Network Security Appendix B - University Question Papers
(OR)
(b) Explain about Diffie-Hellman Key exchange algorithm with one suitable example.
14. (a) Discuss about X.509 authentication service in detail.
(OR)
(b) Explain about S/MIME in detail.
15. (a) Write about virus and related threats in detail.
(OR)
(b) Explain briefly about trusted system.
Prepared by P.Vasantha Kumari 310
Cryptography and Network Security Appendix B - University Question Papers
B.E./B.Tech. DEGREE EXAMINATION, NOVEMBER/DECEMBER 2012
SEVENTH SEMESTER - COMPUTER SCIENCE AND ENGINEERING
IT2352/IT 62 CRYPTOGRAPHY AND NETWORK SECURITY
(Common to Information Technology – Sixth Semester)
(Regulation 2008)
Part A
1. What is the difference between a mono alphabetic and a poly alphabetic cipher?
2. What is an avalanche effect?
3. What are the disadvantages of double DES?
4. Define primitive root.
5. What is one-way property?
6. What are the two approaches of digital signatures?
7. What are the different types of MIME?
8. What protocols comprise SSL?
9. What is an Intruder?
10. Give few examples for worms.
Part B
11. (a) Explain briefly about Fermat’s and Euler’s theorems.
(OR)
(b) Explain the following with suitable examples.
12. (a) Discuss about DES in detail.
(OR)
Prepared by P.Vasantha Kumari 311
Cryptography and Network Security Appendix B - University Question Papers
(b) Explain briefly about RSA and discuss its merit.
13. (a) Explain briefly about Diffie Hellman key exchange algorithm with its pros and cons.
(OR)
(b) Describe about Hash functions.
14. (a) Write about PGP in detail.
(OR)
(b) Explain in detail about SET.
15. (a) Explain about viruses in detail.
(OR)
(b) Explain in detail about firewalls.
Prepared by P.Vasantha Kumari 312
Cryptography and Network Security Appendix B - University Question Papers
B.E/B.TECH DEGREE EXAMINATION, MAY/JUNE 2012
SIXTH SEMESTER
INFORMATION TECHNOLOGY
IT2352 – CRYPTOGRAPHY AND NETWORK SECURITY
(Regulation 2008)
Time: 3 Hours Maximum Marks: 100
Answer All Questions
Part – A
1. Define LFSR sequence.
2. Define finite field.
3. What do you mean by differential cryptanalysis?
4. Define factoring.
5. Distinguish between differential and linear cryptanalysis.
6. Write down the difference between the public key and private key cryptosystems.
7. Define TLS.
8. What do you mean by S/MIME?
9. Write down the system security standards.
10. Define Intrusion.
Part-B (5 × 16 = 80)
11. (a) Explain about Chinese Remainder Theorem. (16)
(OR)
Prepared by P.Vasantha Kumari 313
Cryptography and Network Security Appendix B - University Question Papers
(b) Explain any two types of Cipher Techniques in detail. (16)
12. (a) Explain about Triple DES with an example. (6)
(OR)
(b) Explain about RC4 algorithm. (16)
13. (a) Write notes on Birthday attack. (16)
(OR)
(b) Write the algorithm of MD5 and explain. (16)
14. (a) Describe about IP security. (8)
(OR)
(b) List out the participants of SET system and explain in detail. (16)
15. (a) Explain the various types of firewalls. (16)
(OR)
(b) Explain about the malicious software. (16)
Prepared by P.Vasantha Kumari 314
Cryptography and Network Security Appendix B - University Question Papers
B.E / B.Tech. DEGREE EXAMINATION, MAY/JUNE 2012
EIGHTH SEMESTER - INFORMATION TECHNOLOGY
080250057 – CRYPTOGRAPHY AND NETWORK SECURITY
( Regulation 2008 )
Time : Three Hours Maximum : 100 Marks
Answer ALL Questions
PART A – ( 10 * 2 = 20 Marks )
1. What do you mean by cryptanalysis?
2. What is difference between a block cipher and a stream cipher?
3. What is key distribution center?
4. Mention the application of public key cryptography.
5. Specify the requirements for message authentication.
6. What are the two important key issues related to authenticated key exchange?
7. What entities constitute a full-service Kerberos environment?
8. Why does ESP include a padding field?
9. What are the two types of audit records?
10. What is an access control matrix? What are its elements?
PART B – ( 5 * 16 = 80 marks )
11. (a) Explain about substitution and transposition techniques with two examples for
each.
Prepared by P.Vasantha Kumari 315
Cryptography and Network Security Appendix B - University Question Papers
(OR)
(b) What is the need for triple DES? Write the disadvantages of double DES and explain
triple DES.
12. (a) Explain how the elliptic curves are useful for cryptography?
(OR)
(b) In a public key system using RSA, you intercept the cipher text C=10 sent to a user
whose public key is e=5, n=35. What is the plain text? Explain the above problem with an
algorithm description.
13. (a) Write about the basic uses of MAC and list out the applications.
(OR)
(b) With a neat sketch, explain signing and verifying functions of DSA.
14. (a) Describe briefly about X.509 authentication procedures. And also list out the
drawbacks of X.509 version 2.
(OR)
(b) Write about SSL and TLS.
15. (a) Explain about intrusion detection techniques in detail.
(OR)
(b) Write about trusted systems in detail.
Prepared by P.Vasantha Kumari 316
Cryptography and Network Security Appendix B - University Question Papers
B.E./B.Tech. DEGREE EXAMINATION, NOVEMBER/DECEMBER 2011.
SEVENTH SEMESTER
COMPUTER SCIENCE AND ENGINEERING
IT 2352 – CRYPTOGRAPHY AND NETWORK SECURITY
(Common to Sixth Semester Information Technology)
(Regulation 2008)
Time : Three hours Maximum : 100 marks
Answer ALL questions.
PART A — (10 × 2 = 20 marks)
1. Give the types of attack.
2. List out the problems of one time pad?
3. Write down the purpose of the S-Boxes in DES?
4. Define : Diffusion.
5. Define: Replay attack.
6. List out the parameters of AES.
7. Define : Primality test.
8. State the difference between conventional encryption and public-key encryption.
9. Define : Malicious software.
10. Name any two security standards.
Prepared by P.Vasantha Kumari 317
Cryptography and Network Security Appendix B - University Question Papers
PART B — (5 × 16 = 80 marks)
11. (a) Using play fair cipher algorithm encrypt the message using the key "MONARCHY"
and explain.
(OR)
(b) Explain the ceaser cipher and mono alphabetic cipher.
12. (a) Explain the Key Generation, Encryption and Decryption of SDES algorithm in detail.
(OR)
(b) Write the algorithm of RSA and explain with an example.
13. (a) Illustrate about the SHA algorithm and explain.
(OR)
(b) Write a detailed note on Digital signatures.
14. (a) Describe the SSL Architecture in detail.
(OR)
(b) List out the participants of SET system, and explain in detail.
15. (a) Explain the types of Intrusion Detection Systems.
(OR)
(b) Explain the different types of firewall and its configurations in detail.
Prepared by P.Vasantha Kumari 318
Cryptography and Network Security Appendix B - University Question Papers
B.E/B.TECH DEGREE EXAMINATION, APRIL/MAY 2011
SIXTH SEMESTER
INFORMATION TECHNOLOGY
IT2352 – CRYPTOGRAPHY AND NETWORK SECURITY
(Regulation 2008)
Time: 3 Hours Maximum Marks: 100
Answer All Questions
PART – A (10 × 2 = 20)
1. Differentiate passive attack from active attack with example.
2. What is the use of Fermat’s theorem?
3. What are the different modes of operation in DES?
4. Name any two methods for testing prime numbers.
5. What is discrete logarithm?
6. What do you mean by one-way property in hash function?
7. List out the requirements of Kerberos.
8. Mention four SSL protocols.
9. Define Intruders. Name three different classes of Intruders.
10. What do you mean by Trojan Horses?
Prepared by P.Vasantha Kumari 319
Cryptography and Network Security Appendix B - University Question Papers
PART-B (5 × 16 = 80)
11. (a) Discuss the classical cryptosystems and its types. (16)
(OR)
(b) Describe Euler’s and Chinese Remainder Theorem. (16)
12. (a) (i) Explain about the single round of DES algorithm. (10)
(ii) Describe key discarding process of DES. (6)
(OR)
(b) Explain RSA method in detail. (16)
13. (a) Discuss the discrete logarithm and explain Diffie-Hellman key exchange algorithm
with its merits and demerits. (16)
(OR)
(b) Explain about MD5 in detail. (16)
14. (a) Write on the following:
(i) Differentiate SSL from SET. (8)
(ii) Overview of IP security documents. (8)
(OR)
(b) Explain PGP message generation and reception. (16)
15. (a) Explain definition, phases, types of virus structures and types of viruses. (16)
(OR)
(b) Write in detail about definition, characteristics, types and limitations of firewalls.
(16)
Prepared by P.Vasantha Kumari 320
Cryptography and Network Security Appendix B - University Question Papers
B.E/B.TECH DEGREE EXAMINATION, NOV/DEC 2009
IT1352 – CRYPTOGRAPHY AND NETWORK SECURITY
Time: 3 Hours Maximum Marks: 100
Answer All Questions
PART – A (10 × 2 = 20)
1. What is cryptanalysis and cryptography?
2. Define threat and attack.
3. What is the role of session key in public key schemes?
4. What is a zero point of an elliptic curve?
5. What are the functions used to produce an authenticator?
6. List the properties a digital signature should possess?
7. Mention the scenario where Kerberos scheme is preferred.
8. What are the technical deficiencies in the Kerberos version 4 protocol?
9. List the classes of intruders.
10. Give the types of viruses.
Prepared by P.Vasantha Kumari 321
Cryptography and Network Security Appendix B - University Question Papers
PART-B (5 × 16 = 80)
11.(a).Explain the OSI security architecture along with the services available.
(OR)
(b).(i).Given 10 bit key K=1010000010. Determine K1,K2 where
P10=3 5 2 7 4 10 1 9 8 6
P8= 6 3 7 4 8 5 10 9
by using SDES key generation method.
12.(a).(i).Perform Encryption/Decryption using RSA algorithm for the following:
p=3, q=11, e=7, m=5
(ii).What attacks are possible on RSA algorithm?
(OR)
(b).(i).Given the key 'MONARCHY' apply play fair to plain text "FACTIONALISM" to
ensure confidentiality at the destination, decrypt the ciphertext and establish authenticity.
(ii).Apply public key encryption to establish confidentiality in the message from A to
B. You are given m=67, KU={7,187}, KR={23,187}
13.(a).(i).Apply the MAC on the cryptographic checksum method to authenticate build
confidentiality of the message where the authentication is tied to message.
M=8376, K1=4892, K2=53624071
(ii).What are the properties a hash function must satisfy?
(OR)
(b).Explain MD5 message digest algorithm, with it's logic and compression function.
14.(a).Explain X.509 authentication service and it's certificates.
(OR)
(b).(i).Explain the services of PGP.
(ii).Write down the functions provided by S/MIME.
15.(a).(i).List the approaches for the intrusion detection.
(ii).Explain firewall design principles, characteristics and types of firewalls.
(OR)
(b).(i).Give the basic techniques which are in use for the password selection strategies.
(ii).Write down the four generations of antivirus software.
Prepared by P.Vasantha Kumari 322
Cryptography and Network Security Appendix B - University Question Papers
B.E/B.TECH DEGREE EXAMINATION, MAY 2008
IT1352 – CRYPTOGRAPHY AND NETWORK SECURITY
Time: 3 Hours Maximum Marks: 100
Answer All Questions
PART – A (10 × 2 = 20)
1. What is the advantage and disadvantage of one time pad encryption algorithm?
2. If a bit error occurs in plain text block p1 , how far does the error propagate in CBC mode
of DES.
3. When do we say an integer a, less than n is a primitive root of n? State the conditions for
having at least one primitive root or n.
4. What for the miller-rabin algorithm is used?
5. Draw a simple public key encryption model that provides authentication alone.
6. Identify any two applications where one way authentication is necessary.
7. Why the leading two octets of message digest are stored in PGP message along with the
encrypted message digest?
8. State any tow advantages of Oakley key determination protocol over Diffie-Hellman key
Prepared by P.Vasantha Kumari 323
Cryptography and Network Security Appendix B - University Question Papers
exchange protocol.
9. How are the passwords stored in password file in UNIX operating system?
10. What is meant by polymorphic viruses?
PART-B (5 × 16 = 80)
11. (a) (i). Discuss any four substitution cipher encryption methods and list their merits
and demerits.
(ii). How are diffusion and confusion achieved in DES.
(OR)
(b) (i). in AES, explain how the encryption key is expanded to produce keys for the 10
rounds.
(ii). Explain the types of attacks on double DES and triple DES.
12. (a) (i). How are arithmetic operations on integers carried out from their residues
modulo a set of pair wise relatively prime moduli. Give the procedure to reconstruct the
integers form the residue.
(ii). How is discrete logarithm evaluated for a number . what is the role of discrete
logarithms in the diffie hellman key exchange in exchanging the secret key among two
users.
(OR)
(b) (i). Identify the possible threats for RSA algorithm and list their counter measures.
(ii). State the requirements for the design of an elliptic curve crypto system. Using
that , explain how secret keys are exchanged and messages are encrypted.
13. (a). (i). Describe digital signature algorithm and show how signing and verification is
done using DSS.
(ii). Consider any message M of length 4120 bits ending with ABCDEF in
hexadecimal form. Construct the last block of message to be given as input for the MD5.
(OR)
(b) (i). Explain the processing of a message block of 512 bits using SHA1.
(ii). Write about the symmetric encryption approach for digital signatures.
14. (a) (i). Describe the authentication dialogue used by Kerberos for obtaining services
Prepared by P.Vasantha Kumari 324
Cryptography and Network Security Appendix B - University Question Papers
from another realm.
(ii). Explain with the help of an example how a user’s certificate is obtained from
another certification authority in x509 scheme.
(OR)
(b). (i). what are the functions included in MIME in order to enchance security how are
they done.
(ii). why does PGP maintain key rings with every users. Explain how the messages
are generated and received by PGP.
15). (a) (i). Explain any tow approached for intrusion detection.
(ii). Suggest any three password selection strategies and identify their advantages
and disadvantages if any.
(OR)
(b). (i). Identify a few malicious programs that need a host program for their existence.
(ii). Describe the familiar types of firewall configurations.
B.E/B.TECH DEGREE EXAMINATION, NOV 2007
IT1352 – CRYPTOGRAPHY AND NETWORK SECURITY
Time: 3 Hours Maximum Marks: 100
Answer All Questions
PART – A (10 × 2 = 20)
1. What is avalanche effect?
2. What are the types of attacks on encrypted message?
3. Find gcd(56,86) using euclid’s algorithm.
4. Why elliptic curve cryptography is considered to be better than RSA?
5. What is masquerading?
6. Define weak collision property of a hash function.
7. What is x.509 standard?
8. Give IPSEC ESP FORMAT.
9. What are honey pots?
Prepared by P.Vasantha Kumari 325
Cryptography and Network Security Appendix B - University Question Papers
10. List down the four phases of virus.
PART-B (5 × 16 = 80)
11. (a) Discuss in detail encryption and decryption process of AES.
(OR)
(b) (i). Briefly explain design principles of block cipher.
(ii). Discuss in detail block cipher modes of operation.
12. (a) (i). Discuss in detail RSA algorithm, highlighting its computational aspect and
security.
(ii). Perform decryption and encryption using RSA algorithm with p=3 q=11 e=7 and
N=5.
(OR)
(b) Briefly explain Diffie Hellman key exchange with an example.
13. (a). (i). Explain authentication functions in detail.
(ii). What is meant by message digest give example.
(OR)
(b) (i). Briefly explain digital signature algorithm.
(ii). Discuss clearly secure hash algorithm.
14. (a) (i). What is Kerberos? Explain how it provides authenticated service.
(ii). Explain the architecture of IPSEC.
(OR)
(b). (i). Explain handshake protocol actions of SSL.
(ii). Discuss in detail secure electronic transaction.
15). (a) (i). Explain firewalls and how they prevent intrusions.
(ii). Explain the concept of reference monitor.
(OR)
(b). (i). Define intrusion detection and the different types of detection mechanisms, in
detail.
(ii). Comment on password selection strategies and their significance.
Prepared by P.Vasantha Kumari 326
También podría gustarte
- DSE4610 DSE4620 Operators ManualDocumento86 páginasDSE4610 DSE4620 Operators ManualJorge Carrasco100% (6)
- MAKAUT Question Paper Software EnggDocumento2 páginasMAKAUT Question Paper Software EnggersayantanAún no hay calificaciones
- Coa Important QuestionsDocumento5 páginasCoa Important QuestionsGanesh Babu100% (2)
- Stqa Paper Solution (Des 16)Documento33 páginasStqa Paper Solution (Des 16)RajaviAún no hay calificaciones
- Erp QuestionnaireDocumento3 páginasErp Questionnaireviji_kichuAún no hay calificaciones
- Uid Question BankDocumento3 páginasUid Question BankVinoth Ragunathan50% (2)
- VIRTUAL REALITY JNTU Previous Years Question PapersDocumento1 páginaVIRTUAL REALITY JNTU Previous Years Question PaperssrchougulaAún no hay calificaciones
- CNS 3-1 Lab ManualDocumento34 páginasCNS 3-1 Lab Manualsadweep100% (2)
- String Review Question and AnswersDocumento2 páginasString Review Question and AnswersAarohi Sharma100% (1)
- OS Question Bank - All Modules - II ND YearDocumento8 páginasOS Question Bank - All Modules - II ND YearVamshidhar Reddy100% (1)
- Laboratory Manual: Object Oriented Software EngineeringDocumento58 páginasLaboratory Manual: Object Oriented Software Engineeringrsingh1987Aún no hay calificaciones
- Arvr QBDocumento5 páginasArvr QBHari DeivasigamaniAún no hay calificaciones
- ST (2 & 16 Mark Question Bank)Documento23 páginasST (2 & 16 Mark Question Bank)AnithaAún no hay calificaciones
- Computer Architecture Question BankDocumento7 páginasComputer Architecture Question BankSalma Mehajabeen ShajahanAún no hay calificaciones
- Infosys ps-2Documento15 páginasInfosys ps-2saieswar4uAún no hay calificaciones
- Distributed Computing Question PaperDocumento2 páginasDistributed Computing Question Paperatul211988Aún no hay calificaciones
- EC8392-DE Question Bank With Answers 1Documento44 páginasEC8392-DE Question Bank With Answers 1shanthiantony100% (1)
- CS3491 - AIML Lab RecordDocumento79 páginasCS3491 - AIML Lab RecordVASANTH MAún no hay calificaciones
- 18cse381t - Cryptography Question Bank CseDocumento33 páginas18cse381t - Cryptography Question Bank CsealgatesgiriAún no hay calificaciones
- EC6018 MULTIMEDIA COMPRESSION AND COMMUNICATION Question BankDocumento28 páginasEC6018 MULTIMEDIA COMPRESSION AND COMMUNICATION Question BankbalabaskerAún no hay calificaciones
- UNIT 5 ProgramingDocumento6 páginasUNIT 5 Programingsuhas kolliparaAún no hay calificaciones
- Iot Questions For AssignmentsDocumento1 páginaIot Questions For AssignmentsKumar ChaitanyaAún no hay calificaciones
- IT8076 Software Testing Unit1&2 - MCQDocumento24 páginasIT8076 Software Testing Unit1&2 - MCQsyed sabaAún no hay calificaciones
- DAA Lab Manual (New Format)Documento41 páginasDAA Lab Manual (New Format)natty singhAún no hay calificaciones
- MUltimedia Compression Techniques Question PaperDocumento2 páginasMUltimedia Compression Techniques Question PaperPurush Jayaraman100% (1)
- IT8601-Computational Intelligence PDFDocumento12 páginasIT8601-Computational Intelligence PDFOviAún no hay calificaciones
- Toc Important QuestionsDocumento2 páginasToc Important QuestionsKeerthanaAún no hay calificaciones
- Python Tuples, Lists and Dictionary MCQ CS 12Documento12 páginasPython Tuples, Lists and Dictionary MCQ CS 12Anirudh100% (3)
- All MCQ of Software Engineering Unit 1,2,3,4,5.docx Answer KeyDocumento24 páginasAll MCQ of Software Engineering Unit 1,2,3,4,5.docx Answer KeyRaj Gangwar50% (2)
- SRM Valliammai Engineering College (An Autonomous Institution)Documento12 páginasSRM Valliammai Engineering College (An Autonomous Institution)sakthisubi100% (1)
- CS8581 Networks Lab ManualDocumento67 páginasCS8581 Networks Lab ManualTamilvanan S100% (2)
- Computer Graphics Lab ManualDocumento107 páginasComputer Graphics Lab ManualFemilaGoldy79% (14)
- STLD Question BankDocumento11 páginasSTLD Question BankSatish BojjawarAún no hay calificaciones
- Flat Question PapersDocumento2 páginasFlat Question Papersannepu divakarAún no hay calificaciones
- Mobile Computing - Lecture Notes, Study Material and Important Questions, AnswersDocumento4 páginasMobile Computing - Lecture Notes, Study Material and Important Questions, AnswersM.V. TVAún no hay calificaciones
- IT2024-User Interface Design QuestionsDocumento5 páginasIT2024-User Interface Design QuestionsKannan GopalrajAún no hay calificaciones
- Regular Expressions (RE) 3.1Documento53 páginasRegular Expressions (RE) 3.1priyankapothala100% (3)
- 5th Sem Dbms Lab ProgramsDocumento22 páginas5th Sem Dbms Lab ProgramsPrajwal R Prasad33% (3)
- USN CS822: B. E. Degree (Autonomous) Eighth Semester End Examination (SEE), May 2020/june 2020Documento2 páginasUSN CS822: B. E. Degree (Autonomous) Eighth Semester End Examination (SEE), May 2020/june 2020gokulAún no hay calificaciones
- Application of Soft Computing Question Paper 21 22Documento3 páginasApplication of Soft Computing Question Paper 21 22Mohd Ayan BegAún no hay calificaciones
- Mobile Computing Question Paper For JntuDocumento4 páginasMobile Computing Question Paper For JntuBonam SandeepAún no hay calificaciones
- M.tech Mid Question Paper CPLD & FpgaDocumento2 páginasM.tech Mid Question Paper CPLD & Fpgakanavath100% (3)
- Ada Lab ManualDocumento57 páginasAda Lab ManualManohar NVAún no hay calificaciones
- 18CSO106T Data Analysis Using Open Source Tool: Question BankDocumento26 páginas18CSO106T Data Analysis Using Open Source Tool: Question BankShivaditya singhAún no hay calificaciones
- Vlsi - Objective-Questions PDFDocumento9 páginasVlsi - Objective-Questions PDFvmspraneethAún no hay calificaciones
- MCAN201 Data Structure With Python Questions For 1st InternalDocumento2 páginasMCAN201 Data Structure With Python Questions For 1st InternalDr.Krishna BhowalAún no hay calificaciones
- Multi - Core Architectures and Programming - Lecture Notes, Study Material and Important Questions, AnswersDocumento49 páginasMulti - Core Architectures and Programming - Lecture Notes, Study Material and Important Questions, AnswersM.V. TV0% (1)
- AI Practical ListDocumento2 páginasAI Practical ListShalin SirwaniAún no hay calificaciones
- Logical Ability 2Documento10 páginasLogical Ability 2Yella Reddy0% (1)
- Iot MCQ Unit IDocumento21 páginasIot MCQ Unit IMadhubala SivajiAún no hay calificaciones
- r05311201 Automata and Compiler DesignDocumento6 páginasr05311201 Automata and Compiler DesignSrinivasa Rao G100% (3)
- Question Paper Code:: Anna University, Polytechnic & SchoolsDocumento2 páginasQuestion Paper Code:: Anna University, Polytechnic & SchoolsDr.R.MurugadossAún no hay calificaciones
- University QuestionsDocumento24 páginasUniversity QuestionsVasantha KumariAún no hay calificaciones
- NS Summer 16Documento1 páginaNS Summer 1624210134Aún no hay calificaciones
- (CS6701 PTCS6701)Documento3 páginas(CS6701 PTCS6701)Russian CarxgameAún no hay calificaciones
- 07TE762Documento2 páginas07TE762Shiva ShankarAún no hay calificaciones
- It 1352-Cryptography and Network Security Question PaperDocumento2 páginasIt 1352-Cryptography and Network Security Question Paper11dreamerAún no hay calificaciones
- QP16 Network SecurityDocumento2 páginasQP16 Network SecurityreshmapdscemailboxAún no hay calificaciones
- Assignment-1 Is PDFDocumento2 páginasAssignment-1 Is PDFVinayak NadarAún no hay calificaciones
- (WWW - Entrance-Exam - Net) - DOEACC B Level-Network Management & Information Security Sample Paper 1Documento2 páginas(WWW - Entrance-Exam - Net) - DOEACC B Level-Network Management & Information Security Sample Paper 1DEBLEENA VIJAYAún no hay calificaciones
- QP10 CNS QPDocumento2 páginasQP10 CNS QPreshmapdscemailboxAún no hay calificaciones
- Information Assurance & Network Security: B.E. (Computer Engineering) Seventh Semester (CBS)Documento2 páginasInformation Assurance & Network Security: B.E. (Computer Engineering) Seventh Semester (CBS)YashaswiAún no hay calificaciones
- (All India Tour Operator & Travel Agent) : Samyuktha Tours & Travels (Regd)Documento6 páginas(All India Tour Operator & Travel Agent) : Samyuktha Tours & Travels (Regd)Vasantha KumariAún no hay calificaciones
- On Theory of Computation Session Schedule B R E A K L U N C H B R E A KDocumento2 páginasOn Theory of Computation Session Schedule B R E A K L U N C H B R E A KVasantha KumariAún no hay calificaciones
- Unit 4Documento30 páginasUnit 4Vasantha KumariAún no hay calificaciones
- System Software LabDocumento63 páginasSystem Software LabVasantha KumariAún no hay calificaciones
- Department of CSE Department of CSEDocumento1 páginaDepartment of CSE Department of CSEVasantha KumariAún no hay calificaciones
- C. Inserting XML Documents in An Integer ColumnDocumento19 páginasC. Inserting XML Documents in An Integer ColumnVasantha KumariAún no hay calificaciones
- Data Structures and Object Oriented Programming in C++: Unit-IDocumento40 páginasData Structures and Object Oriented Programming in C++: Unit-IVasantha KumariAún no hay calificaciones
- Ec 2202 Data Structures and Object Oriented Programming in C++ Unit Iii Data Structures & Algorithms 3.1. AlgorithmDocumento36 páginasEc 2202 Data Structures and Object Oriented Programming in C++ Unit Iii Data Structures & Algorithms 3.1. AlgorithmVasantha KumariAún no hay calificaciones
- Data Structures and Object Oriented Programming in C++ Unit - Ii Advanced Object Oriented ProgrammingDocumento32 páginasData Structures and Object Oriented Programming in C++ Unit - Ii Advanced Object Oriented ProgrammingVasantha KumariAún no hay calificaciones
- Confirmation Mail (TOC)Documento3 páginasConfirmation Mail (TOC)Vasantha KumariAún no hay calificaciones
- Ex3 FCFS SJF PS RRDocumento9 páginasEx3 FCFS SJF PS RRVasantha KumariAún no hay calificaciones
- 12 File AllocationDocumento6 páginas12 File AllocationVasantha KumariAún no hay calificaciones
- DB2 Associate Mock Test Time Duration: 1 Hr. 30 Min. Passing Percentage: 60Documento11 páginasDB2 Associate Mock Test Time Duration: 1 Hr. 30 Min. Passing Percentage: 60Vasantha KumariAún no hay calificaciones
- Exam Centre: Direct Recruitment To The Post of Ae Elec/ Mech/Civil Hall TicketDocumento1 páginaExam Centre: Direct Recruitment To The Post of Ae Elec/ Mech/Civil Hall TicketVasantha KumariAún no hay calificaciones
- Implementation of System CallsDocumento5 páginasImplementation of System CallsVasantha KumariAún no hay calificaciones
- Implementation of Producer-Consumer Problem Using Semaphores ProgramDocumento2 páginasImplementation of Producer-Consumer Problem Using Semaphores ProgramVasantha KumariAún no hay calificaciones
- 15 06 24 09 43 12 3306 RajkumarDocumento40 páginas15 06 24 09 43 12 3306 RajkumarVasantha KumariAún no hay calificaciones
- Ex1 &2 Commands and ShellDocumento28 páginasEx1 &2 Commands and ShellVasantha KumariAún no hay calificaciones
- Ex-6Implement Threading & Synchronization ApplicationsDocumento2 páginasEx-6Implement Threading & Synchronization ApplicationsVasantha KumariAún no hay calificaciones
- Implement All File Organization TechniquesDocumento12 páginasImplement All File Organization TechniquesVasantha KumariAún no hay calificaciones
- Program: (Fifo) : 10) A) Program To Implement Fifo Page Replacement AlgorithmDocumento7 páginasProgram: (Fifo) : 10) A) Program To Implement Fifo Page Replacement AlgorithmVasantha KumariAún no hay calificaciones
- Ex - No:9 Paging Technic of Memory ManagementDocumento2 páginasEx - No:9 Paging Technic of Memory ManagementVasantha KumariAún no hay calificaciones
- Exp# 5d Shared Memory Aim: CS2257 Operating System LabDocumento4 páginasExp# 5d Shared Memory Aim: CS2257 Operating System LabVasantha KumariAún no hay calificaciones
- 7 .8bank and DeadlockDocumento6 páginas7 .8bank and DeadlockVasantha KumariAún no hay calificaciones
- Unit I: 1.2 Characteristics of ComputerDocumento51 páginasUnit I: 1.2 Characteristics of ComputerVasantha KumariAún no hay calificaciones
- Cultures of The West A History, Volume 1 To 1750 3rd PDFDocumento720 páginasCultures of The West A History, Volume 1 To 1750 3rd PDFtonnyAún no hay calificaciones
- Tawjihi 7Documento55 páginasTawjihi 7api-3806314Aún no hay calificaciones
- Pit Viper 351Documento6 páginasPit Viper 351Sebastian Robles100% (2)
- Ibps RRB Po Scale - I Prelims Model Mock Test - 8Documento7 páginasIbps RRB Po Scale - I Prelims Model Mock Test - 8Sanjay DasAún no hay calificaciones
- Guide: Daily ReferenceDocumento8 páginasGuide: Daily ReferenceGalina TodorovaAún no hay calificaciones
- Engineering Data: Wireway SelectionDocumento3 páginasEngineering Data: Wireway SelectionFidel Castrzzo BaeAún no hay calificaciones
- Reducing Motor Vehicle Crashes in B.C.Documento260 páginasReducing Motor Vehicle Crashes in B.C.Jeff NagelAún no hay calificaciones
- Nickel 200 201 PDFDocumento20 páginasNickel 200 201 PDFwdavid81Aún no hay calificaciones
- Win Darab V7 DatasheetDocumento3 páginasWin Darab V7 DatasheetPatrick StivénAún no hay calificaciones
- Amended August 8 2016Documento31 páginasAmended August 8 2016lux186Aún no hay calificaciones
- Led Matrix A-788bsDocumento5 páginasLed Matrix A-788bsjef fastAún no hay calificaciones
- Principles of Public ExpenditureDocumento1 páginaPrinciples of Public ExpenditureNikhil Shenai100% (1)
- Classical Mechanics MCQ GamecampuscoDocumento3 páginasClassical Mechanics MCQ GamecampuscoFaryal TalibAún no hay calificaciones
- Subject-Verb AgreementDocumento10 páginasSubject-Verb AgreementLouie Jay Cañada AbarquezAún no hay calificaciones
- WRhine-Main-Danube CanalDocumento6 páginasWRhine-Main-Danube CanalbillAún no hay calificaciones
- Science 10 FINAL Review 2014Documento49 páginasScience 10 FINAL Review 2014Zara Zalaal [Student]Aún no hay calificaciones
- Form ConstructionDocumento36 páginasForm ConstructionYhoga DheviantAún no hay calificaciones
- Social and Professional Issues Pf2Documento4 páginasSocial and Professional Issues Pf2DominicOrtegaAún no hay calificaciones
- Iecex Bas 13.0069XDocumento4 páginasIecex Bas 13.0069XFrancesco_CAún no hay calificaciones
- BIO SCI OsmosisDocumento10 páginasBIO SCI OsmosisJoy FernandezAún no hay calificaciones
- Proplanner Assembly Planner PFEPDocumento5 páginasProplanner Assembly Planner PFEPAya MdimeghAún no hay calificaciones
- Resume Of: Name: Kingshuk Saha Address: Mobile: E-MailDocumento2 páginasResume Of: Name: Kingshuk Saha Address: Mobile: E-MailKingshuk Saha PalasAún no hay calificaciones
- Imamsha Maharaj Na Parcha NewDocumento16 páginasImamsha Maharaj Na Parcha NewNARESH R.PATELAún no hay calificaciones
- Zielinski AnArcheology For AnArchivesDocumento10 páginasZielinski AnArcheology For AnArchivesPEDRO JOSEAún no hay calificaciones
- Autonomic Nervous SystemDocumento21 páginasAutonomic Nervous SystemDung Nguyễn Thị MỹAún no hay calificaciones
- Module 1-Mathematics As A Language: Maribel D. Cariñ0Documento4 páginasModule 1-Mathematics As A Language: Maribel D. Cariñ0KhalidAún no hay calificaciones
- Business ProblemsDocumento5 páginasBusiness ProblemsMaureen GarridoAún no hay calificaciones