Documentos de Académico
Documentos de Profesional
Documentos de Cultura
Firefly Perimeter Release Notes
Cargado por
velramsenDerechos de autor
Formatos disponibles
Compartir este documento
Compartir o incrustar documentos
¿Le pareció útil este documento?
¿Este contenido es inapropiado?
Denunciar este documentoCopyright:
Formatos disponibles
Firefly Perimeter Release Notes
Cargado por
velramsenCopyright:
Formatos disponibles
Release Notes: Junos OS Release
12.1X47-D20 for Firefly Perimeter Release
Notes
Release 12.1X47-D20
6 March 2015
Revision 1
The Firefly Suite is designed to address the need for compelling and robust security for
diverse virtualized environments by bringing together three products Firefly Perimeter,
Firefly Host, and Junos Space Virtual Director. These release notes accompany Release
12.1X47-D20 for Firefly Perimeter. They describe supported features and known issues
with Firefly Perimeter.
For the latest, most complete information about outstanding and resolved issues with
Firefly Perimeter, see the Juniper Networks online software defect search application at
http://www.juniper.net/prsearch.
You can also find these release notes on the Firefly Perimeter Documentation webpage,
which is located at https://www.juniper.net/techpubs/firefly-perimeter.
Contents Release Notes for Firefly Perimeter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 3
Upgrading from Prior Releases of Firefly Perimeter . . . . . . . . . . . . . . . . . . . . . . 3
Instructions for Validating Security Signatures . . . . . . . . . . . . . . . . . . . . . . . . . 3
Validating the Firefly Perimeter OVA Image . . . . . . . . . . . . . . . . . . . . . . . . 4
Validating the Firefly Perimeter JVA Image using Linux commands . . . . . 6
Supported Features for Firefly Perimeter 12.1X47-D20 . . . . . . . . . . . . . . . . . . . 8
Licensing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 11
Firefly Perimeter Evaluation License Installation Process . . . . . . . . . . . . . 12
Firefly Perimeter License Installation Process . . . . . . . . . . . . . . . . . . . . . . 12
Updating Firefly Perimeter Licenses . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 14
Firefly Perimeter Feature License Models . . . . . . . . . . . . . . . . . . . . . . . . . 15
Features Supported on Firefly Perimeter . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 15
Known Behavior . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 41
Outstanding Issues in Release 12.1X47-D20 for Firefly Perimeter . . . . . . . . . . 41
Flow and Processing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 41
Chassis Cluster . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
Copyright 2015, Juniper Networks, Inc. 1
Release Notes for Firefly Perimeter
Outstanding Issues in Release 12.1X47-D15 for Firefly Perimeter . . . . . . . . . . 42
Flow and Processing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
Outstanding Issues in Release 12.1X47-D10 for Firefly Perimeter . . . . . . . . . . 42
Chassis Cluster . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
Flow and Processing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
Interfaces and Routing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
IPS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 42
Resolved Issues in Release 12.1X47-D20 for Firefly Perimeter . . . . . . . . . . . . . 42
IPS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
Flow and Processing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
Resolved Issues in Release 12.1X47-D15 for Firefly Perimeter . . . . . . . . . . . . . 43
Chassis Cluster . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
Flow and Processing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
Resolved Issues in Release 12.1X47-D10 for Firefly Perimeter . . . . . . . . . . . . . 43
Chassis Cluster . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 43
Flow and Processing . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 44
IPS . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 44
Junos OS Documentation and Release Notes . . . . . . . . . . . . . . . . . . . . . . . . . . . . 45
Documentation Feedback . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 45
Requesting Technical Support . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 46
Self-Help Online Tools and Resources . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 46
Opening a Case with JTAC . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 46
Revision History . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 47
2 Copyright 2015, Juniper Networks, Inc.
Release Notes for Firefly Perimeter
Release Notes for Firefly Perimeter
Firefly Perimeter is a virtual security appliance that provides security and networking
services at the perimeter in virtualized private or public cloud environments. It runs as a
virtual machine (VM) on a standard x86 server and enables advanced security and routing
at the network edge in a multitenant virtualized environment.
Firefly Perimeter is built on Junos OS and delivers similar security and networking features
available on branch SRX Series devices.
These release notes include:
Upgrading from Prior Releases of Firefly Perimeter on page 3
Instructions for Validating Security Signatures on page 3
Supported Features for Firefly Perimeter 12.1X47-D20 on page 8
Features Supported on Firefly Perimeter on page 15
Known Behavior on page 41
Outstanding Issues in Release 12.1X47-D20 for Firefly Perimeter on page 41
Outstanding Issues in Release 12.1X47-D15 for Firefly Perimeter on page 42
Outstanding Issues in Release 12.1X47-D10 for Firefly Perimeter on page 42
Resolved Issues in Release 12.1X47-D20 for Firefly Perimeter on page 42
Resolved Issues in Release 12.1X47-D15 for Firefly Perimeter on page 43
Resolved Issues in Release 12.1X47-D10 for Firefly Perimeter on page 43
Upgrading from Prior Releases of Firefly Perimeter
You can upgrade to Firefly Perimeter Release 12.1X47D20 from Release 12.1X46-D10 or
later, using the 12.1X47-D20 TGZ image. For new installations you can use the OVA or
JVA images.
Instructions for Validating Security Signatures
This section includes instructions for validating security signatures.
CAUTION: During the Firefly Perimeter installation or upgrade process, do
not modify the filename of the software image that you download from the
Juniper Networks support site. If you modify the filename, then the installation
or upgrade will fail.
Validating the Firefly Perimeter OVA Image
Validating the Firefly Perimeter JVA Image using Linux commands
Copyright 2015, Juniper Networks, Inc. 3
Release Notes for Firefly Perimeter
Validating the Firefly Perimeter OVA Image
Starting with Firefly Perimeter 12.1X47D20 and later, the Firefly Perimeter Open
Virtualization Format Archive (OVA) image is securely signed. You can validate the OVA
image, if necessary. However, you can install or upgrade Firefly Perimeter without
validating the OVA image. Before you validate the OVA image, ensure that the Linux/UNIX
PC on which you are performing the validation has the following utilities available: tar,
openssl, and ovftool You can download the VMware Open Virtualization Format (OVF)
tool from the following location: https://my.vmware.com/web/vmware/details?
productId=353&downloadGroup=OVFTOOL351
To validate the OVA image:
1. Download the Firefly Perimeter OVA image and the Juniper Networks Root certificate
file (JuniperRootRSACA.pem) from the Firefly Perimeter downloads page at
https://www.juniper.net/support/downloads/?p=firefly#sw
NOTE: You only need to download the Juniper Networks Root certificate
file once; you can use the same file to validate OVA images for future
releases of Firefly Perimeter.
2. (Optional) If you downloaded the OVA image and the certificate file to a PC running
Windows, copy the two files to a temporary directory on a PC running Linux or UNIX.
You can also copy the OVA image and the certificate file to a temporary directory
(/var/tmp or /tmp) on a Firefly Perimeter node.
Ensure that the OVA image file and the Juniper Networks Root certificate file are not
modified during the validation procedure. You can do this by providing write access
to these files only to the user performing the validation procedure. This is especially
important if you use an accessible temporary directory, such as /tmp or /var/tmp,
because such directories can be accessed by several users. Take precautions to ensure
that the files are not modified by other users during the validation procedure.
3. Navigate to the directory containing the OVA image.
4. Unpack the OVA image by running the following command:
tar xf ova-filename
where ova-filename is the filename of the previously downloaded OVA image.
5. Verify that the unpacked OVA image contains a certificate chain file (certchain.pem)
and a signature file (vsrx.cert ).
6. Validate the signature in the unpacked OVF file (extension .ovf) by running the following
command:
ovftool ovf-filename
where ovf-filename is the filename of the unpacked OVF file contained within the
previously downloaded OVA image.
4 Copyright 2015, Juniper Networks, Inc.
Instructions for Validating Security Signatures
7. After the unpacked OVF file is validated, validate the signing certificate with the Juniper
Networks Root CA file by running the following command:
openssl verify -CAfile JuniperRootRSACA.pem -untrusted Certificate-Chain-File
Signature-file
where JuniperRootRSACA.pem is the Juniper Networks Root CA file,
Certificate-Chain-File is the filename of the unpacked certificate chain file (extension
.pem) and Signature-file is the filename of the unpacked signature file (extension
.cert).
If the validation is successful, a message indicating that the validation is successful
is displayed.
A sample of the validation procedure is as follows:
-bash-4.1$ ls
JuniperRootCA.pem junos-vsrx-12.1X47-D20.4-domestic.ova
-bash-4.1$ mkdir tmp
-bash-4.1$ cd tmp
-bash-4.1$ tar xf ../junos-vsrx-12.1X47-D20.4-domestic.ova
-bash-4.1$ ls
certchain.pem junos-vsrx-12.1X47-D20.4-domestic.cert
junos-vsrx-12.1X47-D20.4-domestic-disk1.vmdk junos-vsrx-12.1X47-D20.4-domestic.mf
junos-vsrx-12.1X47-D20.4-domestic.ovf
-bash-4.1$ /usr/lib/vmware-ovftool/ovftool junos-vsrx-12.1X47-D20.4-domestic.ovf
OVF version: 1.0
VirtualApp: false
Name: Firefly Perimeter
Version: JUNOS 12.1
Vendor: Juniper Networks Inc.
Product URL:
http://www.juniper.net/us/en/products-services/software/security/vsrxseries/
Vendor URL: http://www.juniper.net/
Download Size: 227.29 MB
Deployment Sizes:
Flat disks: 2.00 GB
Sparse disks: 265.25 MB
Networks:
Name: VM Network
Description: The VM Network network
Virtual Machines:
Name: Juniper Virtual SRX
Operating System: freebsdguest
Virtual Hardware:
Families: vmx-07
Number of CPUs: 2
Cores per socket: 1
Memory: 2.00 GB
Disks:
Index: 0
Instance ID: 5
Copyright 2015, Juniper Networks, Inc. 5
Release Notes for Firefly Perimeter
Capacity: 2.00 GB
Disk Types: IDE
NICs:
Adapter Type: E1000
Connection: VM Network
Adapter Type: E1000
Connection: VM Network
Deployment Options:
Id: 2GvRAM
Label: 2G vRAM
Description:
2G Memory
-bash-4.1$ openssl verify -CAfile ../JuniperRootCA.pem -untrusted certchain.pem
junos-vsrx-12.1X47-D20.4-domestic.cert
junos-vsrx-12.1X47-D20.4-domestic.cert: OK
8. (Optional) If the validation is not successful, perform the following tasks:
a. Determine if the contents of the OVA image have been modified. If the contents
have been modified, download the OVA image from the Firefly Perimeter downloads
page.
b. Determine whether the Juniper Networks Root CA file is corrupted or modified. If
it was corrupted or modified, download the certificate file from the Firefly Perimeter
downloads page.
c. Retry the preceding validation steps using one or both new files.
Validating the Firefly Perimeter JVA Image using Linux commands
The Firefly Perimeter.jva format includes an embedded digital signature that can be
validated to ensure authenticity of the content. In order to do so, along with the .jva file,
you will need a copy of Juniper's root certificate. Once you have downloaded both, you
will need to run a set of commands to extract the contents within the .jva file, authenticate
the embedded signature with the signing certificate, and authenticate the signing
certificate with Juniper's root certificate.
Once you have the .jva file and Juniper root certificate file in the same directory, use the
following commands:
1. bash junos-vsrx-12.1X47-D20.4-domestic.jva -x (hit 'y' to accept the EULA)
2. ls (to show the newly created directory containing the .jva contents)
3. cd(to enter into the newly created directory containing .jva contents)
4. openssl x509 -pubkey -noout -in vsrx.cert > public.pem (this extracts the public key
from the signing certificate)
5. head -1 vsrx.cert | awk '{print $2}' | xxd -p -r > signature.binary (this converts the
hex-encoded signature to binary format)
6 Copyright 2015, Juniper Networks, Inc.
Instructions for Validating Security Signatures
6. openssl dgst -sha1 -verify public.pem -signature signature.binary vsrx.sig (This command
will validate the signature with the signing certifcate. A successful validation will result
in the message 'Verified OK'.)
7. openssl verify -CAfile ../JuniperRootCA.pem -untrusted certchain.pem vsrx.cer (This
command will validate the signing certificate with Juniper's root certificate. A successful
validation will result in message 'vsrx.cert: OK')
A sample of the JVA signature validation procedure using Linux commands is as follows:
-bash-4.1$ ls
JuniperRootCA.pem junos-vsrx-12.1X47-D20.4-domestic.jva
-bash-4.1$ bash junos-vsrx-12.1X47-D20.4-domestic.jva -x
Accept?[y/n]y
Extracting ...
Image dumped:
junos-vsrx-12.1X47-D20.4-domestic/junos-vsrx-12.1X47-D20.4-domestic.img
-rw-r--r-- 1 dkan nscn 278659072 Aug 15 10:05
junos-vsrx-12.1X47-D20.4-domestic/junos-vsrx-12.1X47-D20.4-domestic.img
-bash-4.1$ ls
JuniperRootCA.pem junos-vsrx-12.1X47-D20.4-domestic
junos-vsrx-12.1X47-D20.4-domestic.jva
-bash-4.1$ cd junos-vsrx-12.1X47-D20.4-domestic
-bash-4.1$ ls
certchain.pem junos-vsrx-12.1X47-D20.4-domestic.img vsrx.cert vsrx.sig vsrx.xml
-bash-4.1$ openssl verify -CAfile ../JuniperRootCA.pem -untrusted certchain.pem vsrx.cert
vsrx.cert: OK
-bash-4.1$ openssl x509 -pubkey -noout -in vsrx.cert > public.pem
-bash-4.1$ head -1 vsrx.cert | awk '{print $2}' | xxd -p -r > signature.binary
-bash-4.1$ openssl dgst -sha1 -verify public.pem -signature signature.binary vsrx.sig
Verified OK
Copyright 2015, Juniper Networks, Inc. 7
Release Notes for Firefly Perimeter
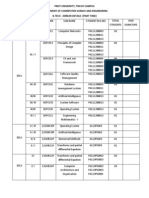
Supported Features for Firefly Perimeter 12.1X47-D20
Table 1 on page 8 lists the main features that are supported on Firefly Perimeter Release
12.1X47-D20.
Table 1: Features Supported on Firefly Perimeter
Feature Description Firefly Perimeter Platform
Unified Threat Consolidation of several security VMware and KVM
Management (UTM) features into one device,
protecting against multiple threat
types.
For more information, refer to
http://www.juniper.net/techpubs/
en_US/junos12.1x47/
information-products/
pathway-pages/security/
security-utm-index.html
Intrusion Prevention Detects and prevents attacks in VMware and KVM
System (IPS) network traffic.
For more information, refer to
http://www.juniper.net/techpubs/
en_US/junos12.1x47/
information-products/pathway-
pages/security/security-
idp-index.html
Transparent mode Filters packets that traverse the VMware and KVM
device without modifying any of
the source or destination
information in the IP packet
headers.
For more information, refer to
http://www.junos.com/techpubs/
en_US/junos12.1x45/topics/
concept/security-layer2-bridging
-transparent-mode-overview.html
IPsec VPN Provides security to IP flows VMware and KVM
through the use of authentication
and encryption.
For more information, refer to
http://www.juniper.net/techpubs/
en_US/junos12.1x47/
information-products/pathway-
pages/security/security-vpn
-ipsec.html
8 Copyright 2015, Juniper Networks, Inc.
Supported Features for Firefly Perimeter 12.1X47-D20
Table 1: Features Supported on Firefly Perimeter (continued)
Feature Description Firefly Perimeter Platform
Chassis cluster support KVM hypervisor environment KVM
for VirtIO driver supports chassis cluster using the
VirtIO driver and interfaces.
For more information, refer to
http://www.juniper.net/techpubs/
en_US/junos12.1x47/
information-products/pathway-
pages/security/security-chassis-
cluster.html
Transparent mode Supports transparent mode on VMware and KVM
chassis cluster support chassis cluster.
For more information, refer to
http://www.juniper.net/techpubs/
en_US/junos12.1x47/
information-products/
pathway-pages/security/
security-chassis-cluster.html
VMware vSphere 5.5 VMware vSphere 5.5 supported in VMware
support addition to VMware vSphere 5.0
and 5.1.
Deterministic NAT Identifies attackers and deals with VMware and KVM
abuse without NAT translation
logging for each connection or
port blocks.
For more information, refer to
http://www.juniper.net/techpubs/
en_US/junos12.1x47/
information-products/
pathway-pages/security/
security-nat.html#overview
Port Block Allocation Allocates ports to subscribers in VMware and KVM
(PBA) NAT blocks and generates logs during
block allocation or release.
For more information, refer to
http://www.juniper.net/techpubs/
en_US/junos12.1x47/
information-products/
pathway-pages/security/
security-nat.html#overview
Copyright 2015, Juniper Networks, Inc. 9
Release Notes for Firefly Perimeter
Table 1: Features Supported on Firefly Perimeter (continued)
Feature Description Firefly Perimeter Platform
Application Starting from Firefly Perimeter VMware and KVM
Identification (AppID) 12.1X47-D20, Application
Identification is supported. This
feature identifies applications as
parts of application clusters in
TCP/UDP/ICMP traffic.
Application Identification
strengthens the firewall at
different network layers using
different techniques rather than
port number and IP addresses.
Application signatures are
modified to provide security at
application levels. For more
information, refer to
http://www.juniper.net/techpubs/
en_US/junos12.1x47/information-
products/pathway-pages/security/
security-application-identification
.html
Application Quality of Starting from Firefly Perimeter VMware and KVM
Service (AppQoS) 12.1X47-D20, Application Quality
of Service (AppQoS) is supported.
Application Quality of Service
(AppQoS) is a part of the
AppSecure suite of components.
This feature expands the
capability to include marking
Differentiated Service Code Point
(DSCP) values based on Layer-7
application. Rate-Limiter, DSCP
rewrite, set loss priority, priority
and queue traffic are the
techniques used by AppQoS. For
more information, refer to
http://www.juniper.net/techpubs/
en_US/junos12.1x47/topics/concept/
security-application-qos
-understanding
.html
Application Firewall Starting from Firefly Perimeter VMware and KVM
(AppFW) 12.1X47-D20, Application Firewall
is supported. For more
information, refer to
http://www.juniper.net/techpubs/
en_US/junos12.1x47/topics/concept/
application-firewall-overview.html
10 Copyright 2015, Juniper Networks, Inc.
Supported Features for Firefly Perimeter 12.1X47-D20
Table 1: Features Supported on Firefly Perimeter (continued)
Feature Description Firefly Perimeter Platform
Dynamic Host Starting from Firefly Perimeter VMware and KVM
Configuration Protocol 12.1X47-D20, Dynamic Host
(DHCP) Configuration Protocol (DHCP) is
supported. Dynamic Host
Configuration Protocol (DHCP) is
based on BOOTP, a bootstrap
protocol that allows a client to
discover its own IP address, the IP
address of a server host, and the
name of a bootstrap file.
Licensing
Starting with Junos OS Release 12.1X47-D20 for Firefly Perimeter, licenses are required
for advanced security features such as UTM, IPS, and AppSecure.
Licenses are usually ordered when the software application is purchased, and this
information is bound to a customer ID. If you did not order the licenses when you purchased
your software application, contact your account team or Juniper Networks Customer
Care for assistance. Licenses can be procured from the Juniper Networks License
Management System (LMS). To continue using Firefly Perimeter features after an optional
30-day evaluation period (see Firefly Perimeter Evaluation License Installation Process
on page 12), you must purchase and install the license on the device. Otherwise, the
features are disabled.
Table 2 on page 11 lists the Firefly Perimeter license information.
Table 2: Firefly Perimeter License Information
License Details Description
License Type 1, 3, 5-year standalone and bundle SKUs.
License Key License authorization code issued with purchase. The key
is obtained with the authorization code.
License Key Validity License key is valid for multiple instances and contains a
customer ID.
License Key Duration Same as purchased license.
License Key Activation Activated with license key.
License Enforcement Enforced with license key.
Copyright 2015, Juniper Networks, Inc. 11
Release Notes for Firefly Perimeter
NOTE: If you are performing a software downgrade with licenses installed ,
you will see an error message in the CLI when you try to configure the licensed
features or run the command show system license status.
We recommend deleting the existing licenses before performing a software
downgrade.
Firefly Perimeter Evaluation License Installation Process
Juniper Networks provides a 30-day evaluation license for Firefly Perimeter advanced
security features. You can download the evaluation license from the Evaluation Download
link. Installation of the evaluation license is similar to the regular license installation using
the CLI. See Firefly Perimeter License Installation Process.
NOTE: The 30-day evaluation license period begins from the day you enable
the enhanced security features after installing the evaluation licenses.
Firefly Perimeter License Installation Process
You can install Firefly Perimeter licenses using the following options:
J-Web interface
Junos OS CLI
To install a license from the J-Web interface:
1. Select Maintain>Licenses on the J-Web user interface. The Licenses window is
displayed as shown in Figure 1 on page 12.
Figure 1: Licenses Window
2. Click Add. The Add License window is displayed as shown in Figure 2 on page 13.
3. Enter the full URL to the destination file containing the license key in the License File
URL box or paste the license key text, in plain-text format, in the License Key Text box.
The Add License window is displayed as shown in Figure 2 on page 13.
12 Copyright 2015, Juniper Networks, Inc.
Supported Features for Firefly Perimeter 12.1X47-D20
Figure 2: Add License Window
4. Click OK to add the license key. The License Details window is displayed as shown in
Figure 3 on page 13.
Figure 3: License Details Window
5. The license key is installed and activated on Firefly Perimeter.
To install a license from the CLI:
1. View the details of the license by entering the show system license command.
2. Install the license by entering the request system license add terminal command.
3. Enter the license key and press CTRL+D to end your input.
root@host>
root@host> show system license
License usage: Licenses Licenses Licenses Expiry
Feature name used installed needed
wf key websense ewf 1 0 1 invalid
Licenses installed: none
root@host> request system license add terminal
Copyright 2015, Juniper Networks, Inc. 13
Release Notes for Firefly Perimeter
[Type ^D at a new line to end input,
enter blank line between each license key]
E413012057 aaaaaa bbbbbb cccccc dddddd eeeeee ffffff
cccccc bbbbbb dddddd aaaaaa ffffff aaaaaa
aaaaaa bbbbbb cccccc dddddd eeeeee ffffff
cccccc bbbbbb dddddd aaaaaa ffffff
E413012057: successfully added
add license complete (no errors)
root@host> show system license
License usage: Licenses Licenses Licenses Expiry
Feature name used installed needed
wf key websense ewf 1 1 0 2015-12-31 08:00:00 CST
Licenses installed:
License identifier: E413012057
License version: 4
Software Serial Number: FFPVSRXESXCN
Customer ID: TEST-USER-SYSTEM
Features:
wf_key websense_ewf - Web Filtering EWF
date-based, 2014-11-01 08:00:00 CST - 2015-12-31 08:00:00 CST
NOTE: You can save the license key to a file and upload this file to the
Firefly Perimeter file system through File Transfer Protocol (FTP) or Secure
Copy (SCP). Install the license, and then use the show system license
command to view the updated license information.
4. The license key is installed and activated on Firefly Perimeter.
Updating Firefly Perimeter Licenses
You can update the Firefly Perimeter licenses using the following two methods.
Automatic license update using the CLI.
Manual license update using the CLI.
To enable automatic license updates from the CLI:
1. Obtain a valid license.
2. Configure a valid update server at https://ae1.juniper.net.
3. Contact your account team or Juniper Networks Customer Care for assistance.
4. Use the following configuration to enable automatic license updates.
root@host>
system {
license {
autoupdate {
14 Copyright 2015, Juniper Networks, Inc.
Features Supported on Firefly Perimeter
url https://url.of.license.server;
}
renew before-expiration 30 interval 6;
}
}
The configuration allows Firefly Perimeter to contact the license server 30 days before
the current license expires and sends an automatic update request every 6 hours.
To manually update the license from the CLI:
1. Update the license by entering the request system license update url
https://url.of.license.server command.
2. Check the status of the license by entering the show system license.
This command sends a license update request to the license server immediately.
Firefly Perimeter Feature License Models
For information about how to purchase a software license, contact your Juniper Networks
sales representative at http://www.juniper.net/in/en/contact-us/.
The same license-key can be installed on multiple devices as long as it is not installed
on more devices than the license was purchased for. Table 3 on page 15 describes the
Firefly Perimeter features that require licenses.
Table 3: Firefly Perimeter Feature Licenses
Feature
Application Signature Update (Application Identification)
IDP Signature Update
Juniper-Sophos Antivirus
Juniper-Sophos Antispam
Juniper- Websense Enhanced Web Filter
Each license allows you to run the specified advanced software features on Firefly
Perimeter.
Features Supported on Firefly Perimeter
Firefly Perimeter inherits many features from the SRX Series product line. However,
because some SRX Series features are not directly applicable in a virtualized environment,
they have been excluded from the Firefly Perimeter product line. Table 4 on page 16
describes the available features on Firefly Perimeter as of Release 12.1X47-D20.
For feature roadmap details, contact your Juniper Networks representative.
Copyright 2015, Juniper Networks, Inc. 15
Release Notes for Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter
Feature Support on Firefly Perimeter
Address Books and Address Sets:
Address books Yes
Address sets Yes
Global address objects or sets Yes
Nested address groups Yes
Administrator Authentication:
Local authentication Yes
RADIUS Yes
TACACS+ Yes
Alarms:
Chassis alarms Yes
Interface alarms Yes
System alarms Yes
Application Layer Gateways:
DNS ALG Yes
DNS doctoring support Yes
DNS, FTP, RTSP, and TFTP ALGs (Layer 2) with chassis Yes
clustering
DSCP marking for SIP, H.323, MGCP, and SCCP ALGs Yes
FTP Yes
H.323 Yes
Avaya H.323 No
IKE Yes
MGCP Yes
PPTP Yes
RSH Yes
16 Copyright 2015, Juniper Networks, Inc.
Features Supported on Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
RTSP Yes
SCCP Yes
SIP Yes
SIP ALGNEC Yes
SQL Yes
MS RPC Yes
SUN RPC Yes
TALK Yes
TFTP Yes
Attack Detection and Prevention:
Bad IP option Yes
Block fragment traffic Yes
FIN flag without ACK flag set protection Yes
ICMP flood protection Yes
ICMP fragment protection Yes
IP address spoof Yes
IP address sweep Yes
IP record route option Yes
IP security option Yes
IP stream option Yes
IP strict source route option Yes
IP timestamp option Yes
Land attack protection Yes
Large size ICMP packet protection Yes
Copyright 2015, Juniper Networks, Inc. 17
Release Notes for Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
Loose source route option Yes
Ping of death attack protection Yes
Port scan Yes
Source IP-based session limit Yes
SYN-ACK-ACK proxy protection Yes
SYN and FIN flags set protection Yes
SYN flood protection Yes
SYN fragment protection Yes
TCP address sweep Yes
TCP packet without flag set protection Yes
Teardrop attack protection Yes
UDP address sweep Yes
UDP flood protection Yes
Unknown IP protocol protection Yes
Whitelist for SYN flood screens Yes
WinNuke attack protection Yes
Authentication with IC Series Devices:
Captive Portal Yes
Junos OS Layer 3 enforcement in UAC deployments Yes
Junos OS Layer 2 enforcement in UAC deployments No
NOTE: UAC-IPS and UAC-UTM are also not supported.
Autoinstallation:
Autoinstallation Yes
Class of Service:
Classifiers Yes
18 Copyright 2015, Juniper Networks, Inc.
Features Supported on Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
Code-point aliases Yes
Egress interface shaping Yes
Forwarding classes Yes
High-priority queue on Services Processing Card No
Ingress interface policer Yes
Schedulers Yes
Simple filters Yes
Transmission queues Yes
Tunnels Yes
NOTE: GRE and IP-IP tunnels only.
Virtual channels Yes
Diagnostics Tools:
CLI terminal Yes
Flow monitoring cflowd version 5 and flow monitoring cflowd Yes
version 8
Flow monitoring cflowd version 9 No
Ping host Yes
Ping MPLS Yes
Traceroute Yes
Ping Ethernet (CFM) No
Traceroute Ethernet (CFM) No
DNS Proxy:
DNS proxy cache Yes
DNS proxy with split DNS Yes
Dynamic DNS No
Copyright 2015, Juniper Networks, Inc. 19
Release Notes for Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
Dynamic Host Configuration Protocol:
DHCPv6 client Yes
DHCPv4 client Yes
DHCPv6 relay agent Yes
DHCPv4 relay agent Yes
DHCPv6 server Yes
DHCPv4 server Yes
DHCP server address pools Yes
DHCP server static mapping Yes
Ethernet Link Aggregation:
Routing mode:
LACP in chassis cluster pair No
LACP in standalone device No
Layer 3 LAG on routed ports No
Static LAG in chassis cluster mode No
Static LAG in standalone mode No
Ethernet Link Fault Management:
Interfaces supported:
LACP in chassis cluster pair No
LACP in standalone mode No
Static LAG in chassis cluster mode No
Static LAG in standalone mode No
Physical interface (encapsulations):
ethernet-ccc No
extended-vlan-ccc No
20 Copyright 2015, Juniper Networks, Inc.
Features Supported on Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
ethernet-tcc No
extended-vlan-tcc No
Interface family:
inet Yes
mpls Yes
ccc No
tcc No
iso Yes
ethernet-switching No
inet6 Yes
Aggregated Ethernet interface:
Static LAG No
LACP enabled LAG No
Interface family:
ethernet-switching No
inet Yes
inet6 Yes
iso Yes
mpls Yes
File Management:
Clean up unnecessary files Yes
Delete backup software image Yes
Delete individual files Yes
Download system files Yes
Copyright 2015, Juniper Networks, Inc. 21
Release Notes for Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
Encrypt/decrypt configuration files Yes
Manage account files Yes
Rescue Yes
System zeroize Yes
Monitor start Yes
Archive files Yes
Calculate checksum Yes
Compare files Yes
Rename files Yes
Firewall Authentication:
Firewall authentication on Layer 2 transparent authentication Yes
LDAP authentication server Yes
Local authentication server Yes
Pass-through authentication Yes
RADIUS authentication server Yes
SecurID authentication server Yes
Web authentication Yes
Flow-Based and Packet-Based Processing:
Alarms and auditing Yes
End-to-end packet debugging No
Flow-based processing Yes
Network processor bundling No
Packet-based processing Yes
Selective stateless packet-based services Yes
22 Copyright 2015, Juniper Networks, Inc.
Features Supported on Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
Interfaces:
Physical and Virtual Interface:
Ethernet interface Yes
Gigabit Ethernet interface Yes
Services:
Aggregated Ethernet interface No
GRE interface Yes
IEEE 802.1X dynamic VLAN assignment No
IEEE 802.1X MAC bypass No
IEEE 802.1X port-based authentication control with No
multisupplicant support
Interleaving using MLFR No
Internally configured interface used by the system as a control No
path between the WXC Integrated Services Module and the
Routing Engine
Internally generated GRE interface (gr-0/0/0) Yes
Internally generated IP-over-IP interface (ip-0/0/0) Yes
Internally generated link services interface Yes
Internally generated Protocol Independent Multicast Yes
de-encapsulation interface
Internally generated Protocol Independent Multicast Yes
encapsulation interface
Link fragmentation and interleaving interface Yes
Link services interface Yes
Loopback interface Yes
Management interface Yes
PPP interface No
Copyright 2015, Juniper Networks, Inc. 23
Release Notes for Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
PPPoE-based radio-to-router protocol No
PPPoE interface No
Promiscuous mode on interfaces Yes
NOTE: Promiscuous mode needs to be enabled on hypervisor.
Secure tunnel interface Yes
IP Monitoring:
IP monitoring with route failover (for standalone devices and Yes
redundant Ethernet interfaces)
IP monitoring with interface failover (for standalone devices) Yes
Track IP enhancements (IP Monitoring using RPM) No
IP Security:
Acadia - Clientless VPN No
Alarms and auditing Yes
Antireplay (packet replay attack prevention) Yes
Authentication Yes
Authentication Header (AH) Yes
Autokey management Yes
Automated certificate enrollment using SCEP Yes
Automatic generation of self-signed certificates Yes
Bridge domain and transparent mode Yes
Certificate - Configure local certificate sent to peer Yes
Certificate - Configure requested CA of peer certificate Yes
Certificate - Encoding: PKCS7, X509, PEM, DERs Yes
Certificate - RSA signature Yes
24 Copyright 2015, Juniper Networks, Inc.
Features Supported on Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
Chassis clusters (active/backup and active/active) Yes
NOTE: VMware platform only.
Class of service Yes
CRL update at user-specified interval Yes
Config Mode (draft-dukes-ike-mode-cfg-03) Yes
Dead peer detection (DPD) Yes
Diffie-Hellman (PFS) Group 1 Yes
Diffie-Hellman (PFS) Group 2 Yes
Diffie-Hellman (PFS) Group 5 Yes
Diffie-Hellman Group 1 Yes
Diffie-Hellman Group 2 Yes
Diffie-Hellman Group 5 Yes
Digital signature generation Yes
Dynamic IP address Yes
Dynamic IPsec VPNs No
Encapsulating Security Payload (ESP) protocol Yes
Encryption algorithms 3DES Yes
Encryption algorithms AES 128, 192, and 256 Yes
Encryption algorithms DES Yes
Encryption algorithms NULL (authentication only) Yes
Entrust, Microsoft, and Verisign certificate authorities (CAs) Yes
External Extended Authentication (Xauth) to a RADIUS server Yes
for remote access connections
Group Encrypted Transport (GET VPN) No
Group VPN with dynamic policies No
Copyright 2015, Juniper Networks, Inc. 25
Release Notes for Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
Hard lifetime limit Yes
Hardware IPsec (bulk crypto) Cavium/RMI No
Hash algorithms MD5 Yes
Hash algorithms SHA-1 Yes
Hash algorithms SHA-2 (SHA-256) Yes
Hub & spoke VPN Yes
Idle timers for IKE Yes
Improvements in VPN debug capabilities Yes
Initial contact Yes
Invalid SPI response Yes
IKE Diffie-Hellman Group 14 support Yes
IKE Phase 1 Yes
IKE Phase 1 lifetime Yes
IKE Phase 2 Yes
IKE Phase 2 lifetime Yes
IKE and IPsec predefine proposal sets to work with dynamic No
VPN client
IPsec tunnel termination in routing-instances Yes
IKE support Yes
IKEv1 Yes
IKEv1 authentication, preshared key Yes
IKEv2 Yes
Local IP address management - VPN XAuth support Yes
Local IP address management support for DVPN No
26 Copyright 2015, Juniper Networks, Inc.
Features Supported on Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
Manual installation of DER-encoded and PEM-encoded CRLs Yes
Manual key management Yes
Manual proxy-ID (Phase 2 ID) configuration Yes
NHTB - Next Hop Tunnel Binding Yes
New IPsec Phase 2 authentication algorithm Yes
Online CRL retrieval through LDAP and HTTP Yes
Package dynamic VPN client No
Policy-based VPN Yes
Preshared key (PSK) Yes
Prioritization of IKE packet processing Yes
Reconnect to dead IKE peer Yes
Remote access Yes
Remote access user IKE peer Yes
Remote access user-group IKE peer - group IKE ID Yes
Route-based VPN Yes
SHA-2 IPsec support Yes
Soft lifetime Yes
Static IP address Yes
Suites: standard, compatible, basic, and custom-created Yes
Support for NHTB when the st0.x interface is bound to a routing Yes
instance
Support for remote access peers with shared IKE identity + Yes
mandatory XAuth
Support group IKE IDs for dynamic VPN configuration No
TOS/DSCP honoring/coloring (inner/outer) Yes
Copyright 2015, Juniper Networks, Inc. 27
Release Notes for Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
Tunnel mode with clear/copy/set Don't Fragment bit Yes
UAC Layer 3 enforcement Yes
Virtual router support for route-based VPNs Yes
VPN monitoring (proprietary) Yes
X.509 encoding for IKE Yes
XAuth (draft-beaulieu-ike-xauth-03) Yes
IPv6 Support:
Flow-based forwarding and security features:
Advanced flow Yes
DS-Lite concentrator (aka AFTR) No
DS-Lite initiator (aka B4) No
Firewall filters Yes
Forwarding option: flow mode Yes
Multicast flow Yes
Screens Yes
Security policy (firewall) Yes
Security policy (IPS) Yes
Security policy (user role firewall) No
Zones Yes
IPv6 ALG support for FTP: Yes
Routing, NAT, NAT-PT support
IPv6 ALG support for ICMP: Yes
Routing, NAT, NAT-PT support
IPv6 NAT: Yes
NAT-PT, NAT support
28 Copyright 2015, Juniper Networks, Inc.
Features Supported on Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
IPv6 NAT64 Yes
IPv6-related protocols: Yes
BFD, BGP, ECMPv6, ICMPv6, ND, OSPFv3, RIPng
IPv6 ALG support for TFTP Yes
System services: Yes
DHCPv6, DNS, FTP, HTTP, ping, SNMP, SSH, syslog, Telnet,
traceroute
Packet-based forwarding and security features:
Class of service Yes
Firewall filters Yes
Forwarding option: packet mode Yes
Chassis Cluster
Chassis Cluster Support on VMware:
Active-active Yes
Active-passive Yes
Multicast flow Yes
ALGs Yes
Chassis cluster formation Yes
Control plane failover Yes
Dampening time between back-to-back redundancy group Yes
failover
Data plane failover Yes
Dual control links No
Dual fabric links Yes
In-band cluster upgrade No
Junos OS flow-based routing functionality Yes
Copyright 2015, Juniper Networks, Inc. 29
Release Notes for Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
Layer 2 Ethernet switching capacity No
Layer 2 LAG No
Layer 3 LAG No
LACP support for Layer 2 No
LACP support for Layer 3 No
Low-impact cluster upgrade (ISSU Light) No
Low latency firewall No
Multicast routing Yes
PPPoE over redundant Ethernet interface No
Redundant Ethernet interfaces Yes
Redundant Ethernet interface LAGs No
Redundant Ethernet or aggregate Ethernet interface monitoring Yes
Redundancy group 0 (backup for Routing Engine) Yes
Redundancy group 1 through 128 Yes
Stateful Failover - IPSec VPN (Policy based) Yes
Stateful Failover - IPSec VPN (Route based) Yes
Upstream device IP address monitoring Yes
Upstream device IP address monitoring on a backup interface Yes
Chassis Management
Chassis management (support on VMware) Yes
Chassis cluster support on KVM:
Chassis cluster for VirtIO driver Yes
NOTE: For VirtIO interfaces, link status update is not supported.
The link status of VirtIO interfaces is always reported as UP.
Therefore the Firefly Perimeter implementation using VirtIO and
chassis cluster cannot receive link up and link down messages
from VirtIO interfaces.
30 Copyright 2015, Juniper Networks, Inc.
Features Supported on Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
IPv6 IP Security:
4in4 and 6in6 policy-based site-to-site VPN, AutoKey IKEv1 Yes
4in4 and 6in6 policy-based site-to-site VPN, manual key Yes
4in4 and 6in6 route-based site-to-site VPN, AutoKey IKEv1 Yes
4in4 and 6in6 route-based site-to-site VPN, manual key Yes
Log File Formats:
System (control plane) log file formats:
Binary format (binary) No
Structured syslog (sd-syslog) Yes
Syslog (syslog) Yes
WebTrends Enhanced Log Format (WELF) No
Security (data plane) log file formats:
Binary format (binary) Yes
Structured syslog (sd-syslog) Yes
Syslog (syslog) Yes
WebTrends enhanced log format (WELF) Yes
MPLS:
CCC and TCC No
CLNS Yes
Interprovider and carrier-of-carriers VPNs Yes
Layer 2 VPNs for Ethernet connections Yes
NOTE: Promiscuous mode
needs to be enabled on
hypervisor.
Layer 3 MPLS VPNs Yes
LDP Yes
Copyright 2015, Juniper Networks, Inc. 31
Release Notes for Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
MPLS VPNs with VRF tables on provider edge routers Yes
Multicast VPNs Yes
OSPF and IS-IS traffic engineering extensions Yes
P2MP LSPs Yes
RSVP Yes
Secondary and standby LSPs Yes
Standards-based fast reroute Yes
Multicast:
Filtering PIM register messages Yes
IGMP Yes
PIM RPF routing table Yes
Primary routing mode (dense mode for LAN and sparse mode Yes
for WAN)
Protocol Independent Multicast Static RP Yes
Session Announcement Protocol (SAP) Yes
SDP Yes
Multicast VPN:
Basic multicast features in C-instance Yes
Multicast VPN membership discovery with BGP Yes
P2MP LSP support Yes
P2MP OAM - P2MP LSP ping Yes
Reliable multicast VPN routing information exchange Yes
Network Address Translation:
Destination IP address translation Yes
Disabling source NAT port randomization Yes
32 Copyright 2015, Juniper Networks, Inc.
Features Supported on Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
Interface source NAT pool port Yes
NAT address pool utilization threshold status Yes
NAT traversal (NAT-T) for site-to-site IPsec VPNs (IPv4) Yes
Persistent NAT Yes
Persistent NAT binding for wildcard ports Yes
Persistent NAT hairpinning Yes
Maximize persistent NAT bindings No
Pool translation Yes
Proxy ARP (IPv4) Yes
Proxy NDP (IPv6) Yes
Removing persistent NAT query bindings Yes
Rule-based NAT Yes
Rule translation Yes
Source address and group address translation for multicast Yes
flows
Source IP address translation Yes
Static NAT Yes
Deterministic NAT Yes
PBA NAT Yes
Network Operations and Troubleshooting:
Event policies Yes
Event scripts Yes
Operation scripts Yes
XSLT commit scripts Yes
Network Time Protocol:
Copyright 2015, Juniper Networks, Inc. 33
Release Notes for Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
NTP support Yes
NOTE: VMware recommends
using NTP and disabling time
synchronization in the VMware
Tools.
Packet Capture:
Packet capture Yes
NOTE: Packet capture, in this context, refers to standard
interface packet capture. It is not part of the IPS. Packet capture
is supported only on physical interfaces and tunnel interfaces;
for example, gr, ip, st0.Packet capture is not supported on
redundant Ethernet interfaces (reth).
Real-Time Performance Monitoring Probe
RPM probe Yes
One-way timestamps Yes
Routing:
BGP Yes
BGP extensions for IPv6 Yes
BGP Flowspec No
Compressed Real-Time Transport Protocol (CRTP) No
ECMP flow-based forwarding No
Internet Group Management Protocol (IGMP) Yes
IPv4 options and broadcast Internet diagrams Yes
IPv6 routing, forwarding, global address configuration, and Yes
Internet Control Message Protocol (ICMP)
IS-IS Yes
Multiple virtual routers Yes
Neighbor Discovery Protocol (NDP) and Secure NDP Yes
OSPF v2 Yes
OSPF v3 Yes
34 Copyright 2015, Juniper Networks, Inc.
Features Supported on Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
RIP next generation (RIPng) Yes
RIP v1, v2 Yes
Static routing Yes
Virtual Router Redundancy Protocol (VRRP) Yes
Secure Web Access:
CAs Yes
HTTP Yes
HTTPS Yes
Security Policy Support:
Address books/address sets Yes
Custom policy applications Yes
Global policy Yes
Policy application timeouts Yes
Policy applications and application sets Yes
Policy hit-count tracking Yes
Schedulers Yes
Security policies for self-traffic Yes
SSL proxy No
User role firewall No
Common predefined applications Yes
Shadow policy Yes
Security Zone:
Functional zone Yes
Security zone Yes
Session Logging:
Copyright 2015, Juniper Networks, Inc. 35
Release Notes for Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
Accelerating security and traffic logging Yes
Aggressive session aging Yes
Getting information about sessions Yes
Logging to a single server Yes
Session logging with NAT information Yes
SMTP:
SMTP support Yes
SNMP:
SNMP support Yes
Stateless Firewall Filters:
Stateless firewall filters (ACLs) Yes
Stateless firewall filters (simple filter) No
System Log Files:
Archiving system logs Yes
Configuring system log messages Yes
Disabling system logs Yes
Filtering system log messages Yes
Multiple system log servers (control-plane logs) Yes
Sending system log messages to a file Yes
Sending system log messages to a user terminal Yes
Viewing data plane logs Yes
Viewing system log messages Yes
IDP/IPS
For SRX Series IDP/IPS configuration details, see:
https://www.juniper.net/techpubs/en_US/
junos12.1x46/information-products/
pathway-pages/security/security-idp-index.html.
36 Copyright 2015, Juniper Networks, Inc.
Features Supported on Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
Access Control on IPS audit log Yes
IPS alarms and auditing Yes
IPS application identification No
IPS application DDoS rule base No
Differentiated Services code point (DSCP) marking No
IPS cryptographic key handling No
IPS and UAC coordinated threat Yes
IPS class-of-service action Yes
IPS in an active/active chassis cluster Yes
IPS operational mode - inline tap No
IPS logging Yes
IPS monitoring and debugging Yes
IPS policy Yes
IPS security packet capture Yes
IPS signature database Yes
IPS SSL inspection No
IPS rule base Yes
Jumbo frames Yes
Nested application identification No
Performance and capacity tuning for IPS No
SNMP MIB for IPS monitoring Yes
Transparent Mode:
For information on configuring transparent mode Firefly Perimeter, see
http://www.juniper.net/techpubs/en_US/
junos12.1x46/information-products/pathway-pages/
security/security-layer2-bridging-transparent-mode.pdf.
Copyright 2015, Juniper Networks, Inc. 37
Release Notes for Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
Application DoS (AppDDoS) No
Application Firewall (AppFW) Yes
Application QoS (AppQoS) Yes
Application Tracking (AppTrack) Yes
Bridge domain and transparent mode Yes
Chassis clusters (active/backup and active/active) Yes
Class of service Yes
IPv6 flows Yes
IPv6 security mode No
User role firewall No
UTM Yes
Public Key Infrastructure (PKI)
Certificate chaining (8-deep) Yes
UTM
For SRX Series UTM configuration details, see:
https://www.juniper.net/techpubs/en_US/junos12.1x46/information-products/
pathway-pages/security/security-utm-index.html.
For SRX Series UTM Series Antispam configuration details, see:
https://www.juniper.net/techpubs/en_US/junos12.1x46/information-products/
pathway-pages/security/security-utm-antispam.html.
Anti-spam (AS) Yes
AV Full No
AV Sophos Yes
Content filtering (CF) Yes
Web filtering (WF) Yes
EWF Yes
38 Copyright 2015, Juniper Networks, Inc.
Features Supported on Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
WELF logging Yes
Chassis cluster Yes
Transparent mode No
Express Antivirus (Express AV) No
AppSecure Yes
Ipsec Yes
Upgrading and Rebooting:
Autorecovery No
Boot device configuration No (N.A.)
Boot device recovery No (N.A.)
Chassis components control Yes
Chassis restart Yes
Download manager Yes
Dual-root partitioning No
In-band cluster upgrade No
Low-impact cluster upgrades No
Software upgrades and downgrades Yes
User Interfaces:
CLI Yes
J-Web user interface Yes
Junos XML protocol Yes
Network and Security Manager No
Junos Space Security Director Yes
SRC application No
Copyright 2015, Juniper Networks, Inc. 39
Release Notes for Firefly Perimeter
Table 4: Features Supported on Firefly Perimeter (continued)
Feature Support on Firefly Perimeter
Junos Space Virtual Director Yes
Note: Supported on VMware
only and not on KVM.
VPLS:
Filtering and policing (Packet-Based) Yes
Table 5 on page 40 lists additional features that are not supported on Firefly Perimeter.
Table 5: Firefly Perimeter Feature Support Information
Feature Firefly
Application Identification (Junos OS) Yes
Dynamic VPN (DVPN) No
General Packet Radio Service No
Group VPN No
Hardware Acceleration No
In-Service Software Upgrade (for all VPN and non-VPN features) No
Logical Systems No
Multicast for AutoVPN No
Network Management and Analysis (Suite B implementation No
for IPsec VPN)
Power over Ethernet No
Remote Device Access No
BGP Route Reflector No
Services Offloading No
USB Modem No
Voice over Internet Protocol with Avaya No
Wireless Local Area Network No
40 Copyright 2015, Juniper Networks, Inc.
Known Behavior
Known Behavior
The known behavior in Firefly Perimeter are as follows:
On Firefly Perimeter, maximum performance can be achieved using two vNICs. If you
add more vNICs you can expect a decrease in the total performance due to the interface
driver overhead. The performance behavior is applicable to both VMware and KVM
environments.
On Firefly Perimeter with a KVM chassis cluster, the secondary mode crashes into
database (db) mode after startup and synchronizing with the primary mode.
On Firefly Perimeter, the system halts after the login prompt from the virsh console or
the vnc console. It is unable to ping/ssh/telnet to an interface or a service. Ideally, the
system should start without a halt.
Firefly Perimeter requires a configuration with 2 vCPUs, up to 10 vNICs, 2GB RAM, and
2 GB disk space. When using IPS or UTM, the required memory size is 3 GB RAM.
Firefly Perimeter supports VMware ESXi 5.0, 5.1, and 5.5. For KVM, Firefly Perimeter
supports CentOS 6.3, Ubuntu 14.04, and Contrail 1.0.
VM hardware version cannot be upgraded through vSphere client.
On Firefly Perimeter, family ethernet-switching and services unified-access-control are
not supported.
On Firefly Perimeter, configuring an interface to do traffic loopback is not supported
due to VMware e1000 NIC emulation limitation.
On Firefly Perimeter, configuring XAuth with AutoVPN secure tunnel (st0) interfaces
in point-to-multipoint mode and dynamic IKE gateways is not supported.
Outstanding Issues in Release 12.1X47-D20 for Firefly Perimeter
The following problems currently exist in Juniper Networks Firefly Perimeter. The identifier
following the description is the tracking number in the Juniper Networks Problem Report
(PR) tracking system.
Flow and Processing
Performance on VMware 5.5 update 2 or 3 can degrade significantly (25%) from
previous versions because of an e1000 driver issue. [PR 1052025]
On Firefly Perimeter, the generic routing encapsulation (GRE) interface is down when
ge-0/0/0 is set in the routing instance. [PR 1035957]
On Firefly Perimeter, there is a problem while handling large labels if the remote provider
edge (PE) router disables the vrf-label-label command. [PR 974942]
For a Firefly Perimeter running on Ubuntu 14.04, the commit operation time is slow.
[PR 1060459]
On Firefly Perimeter, while using Network Configuration Protocol (NETCONF) the
commit fails with error UI_NETCONF_ERROR: NETCON. [PR 1060646]
Copyright 2015, Juniper Networks, Inc. 41
Release Notes for Firefly Perimeter
Chassis Cluster
On Firefly Perimeter with a chassis cluster, proxy-ndp on a reth interface fails if the
IPv6 multicast is set to 33:33:0:0:0:0. [PR 993888]
On Firefly Perimeter, cluster connection is unstable over a control or fabric link. [PR
1066969]
Outstanding Issues in Release 12.1X47-D15 for Firefly Perimeter
The following problems currently exist in Juniper Networks Firefly Perimeter. The identifier
following the description is the tracking number in the Juniper Networks Problem Report
(PR) tracking system.
Flow and Processing
On Firefly Perimeter with KVM VirtIO Interface, packet distribution is not evenly
processed for all queues. [PR 925300]
On Firefly Perimeter, the UDP throughput for 2vNICs on 16 VSRX more then 2 vNICs in
a Single VSRX device. [PR 930500]
Outstanding Issues in Release 12.1X47-D10 for Firefly Perimeter
The following problems currently exist in Juniper Networks Firefly Perimeter. The identifier
following the description is the tracking number in the Juniper Networks Problem Report
(PR) tracking system.
Chassis Cluster
In a Firefly Perimeter Layer 2 chassis cluster, when the ping command is used to retrieve
self-traffic details, a 100% packet loss is displayed. [PR 964069]
Flow and Processing
On Firefly Perimeter, RT_IDS logging fails. The issue is related to an IPv6 extension
header introduced in Junos OS Release 12.1X46. [PR 959922]
Interfaces and Routing
On Firefly Perimeter, RADIUS authentication fails if the management interface in a
routing instance is configured with a default route to the management network. [PR
949530]
IPS
Resolved Issues in Release 12.1X47-D20 for Firefly Perimeter
The following problems are resolved in Juniper Networks Firefly perimeter.
42 Copyright 2015, Juniper Networks, Inc.
Resolved Issues in Release 12.1X47-D15 for Firefly Perimeter
IPS
On Firefly Perimeter, the permitted range of values to be entered in the CLI command
set security idp sensor-configuration detector protocol-name TELNET tunable-name
sc_telnet_failed_logins tunable-value incorrectly ranges from 33554432 to 1677721600.
The appropriate range is 2 to 100. This results in commit check error out of range when
a value in the appropriate range has been configured. This issue is fixed. [PR 954372]
Flow and Processing
On Firefly Perimeter, TCP packet re-ordering causes traffic issues when sub-interfaces
on reth are used. This issue is fixed. [PR 1026130]
On Firefly Perimeter, after sending telnet traffic, some incorrect source ports and
destination ports are populating in the log messages. This issue is fixed. [PR 1058838]
Resolved Issues in Release 12.1X47-D15 for Firefly Perimeter
The following problems are resolved in Juniper Networks Firefly perimeter.
Chassis Cluster
On Firefly Perimeter with VMware, there is an issue with the chassis cluster set up in
the VMware 5.5 environment. This issue is fixed. [PR 936992]
On Firefly Perimeter, source MAC learning might fail in Layer 2 mode if redundancy
group failover occurs immediately after an RG0 failover. Waiting 3 to 5 minutes fixed
this issue. [PR 962905]
Flow and Processing
On Firefly Perimeter, transferring UDP traffic from the same source and destination
results in a loop for further forwarding sessions. This issue is fixed. [PR 981170]
On Firefly Perimeter, source MAC learning might fail when there is a failover in node
RG0. This issue is fixed. [PR 972358]
On Firefly Perimeter, proxy-ndp is inactive on the reth interface. This issue is fixed.[PR
985093]
Resolved Issues in Release 12.1X47-D10 for Firefly Perimeter
The following problems are resolved in Juniper Networks Firefly Perimeter.
Chassis Cluster
On Firefly Perimeter with a KVM chassis cluster, one of the interface cards shows
offline. The issue occurs because of a control link failure. This issue is fixed. [PR 966469]
On Firefly Perimeter with a KVM chassis cluster, when the secondary node is rebooted
after a manual failure, the flowd fabric monitor or interface displays a link status as
Down. This issue is fixed. [PR 973945]
Copyright 2015, Juniper Networks, Inc. 43
Release Notes for Firefly Perimeter
On Firefly Perimeter, with a VMware ESXi chassis cluster, a core file is generated during
a failover. This issue is fixed. [PR 976757]
On Firefly Perimeter, the system is unable to capture the attack packets. This issue is
fixed. [PR 980858]
Flow and Processing
On Firefly Perimeter, the secondary node might print SIGTERM or exit information in
the console and crash into db mode. This issue is fixed. [PR 971280]
On Firefly Perimeter, the reth port looses its aggregate physical interface. In this case,
no traffic is able to transit the physical interface. This issue is fixed. [PR 978546]
IPS
On Firefly Perimeter, Application Identification (AI) is not supported. [PR 957639]
44 Copyright 2015, Juniper Networks, Inc.
Junos OS Documentation and Release Notes
Junos OS Documentation and Release Notes
For a list of related Junos OS documentation, see
http://www.juniper.net/techpubs/software/junos/.
If the information in the latest release notes differs from the information in the
documentation, follow the Junos OS Release Notes.
To obtain the most current version of all Juniper Networks technical documentation,
see the product documentation page on the Juniper Networks website at
http://www.juniper.net/techpubs/.
Juniper Networks supports a technical book program to publish books by Juniper Networks
engineers and subject matter experts with book publishers around the world. These
books go beyond the technical documentation to explore the nuances of network
architecture, deployment, and administration using the Junos operating system (Junos
OS) and Juniper Networks devices. In addition, the Juniper Networks Technical Library,
published in conjunction with O'Reilly Media, explores improving network security,
reliability, and availability using Junos OS configuration techniques. All the books are for
sale at technical bookstores and book outlets around the world. The current list can be
viewed at http://www.juniper.net/books.
Documentation Feedback
We encourage you to provide feedback, comments, and suggestions so that we can
improve the documentation. You can send your comments to
techpubs-comments@juniper.net, or fill out the documentation feedback form at
https://www.juniper.net/cgi-bin/docbugreport/ . If you are using e-mail, be sure to include
the following information with your comments:
Document or topic name
URL or page number
Software release version (if applicable)
Copyright 2015, Juniper Networks, Inc. 45
Release Notes for Firefly Perimeter
Requesting Technical Support
Technical product support is available through the Juniper Networks Technical Assistance
Center (JTAC). If you are a customer with an active J-Care or JNASC support contract,
or are covered under warranty, and need post-sales technical support, you can access
our tools and resources online or open a case with JTAC.
JTAC policiesFor a complete understanding of our JTAC procedures and policies,
review the JTAC User Guide located at
http://www.juniper.net/us/en/local/pdf/resource-guides/7100059-en.pdf.
Product warrantiesFor product warranty information, visit
http://www.juniper.net/support/warranty/.
JTAC hours of operationThe JTAC centers have resources available 24 hours a day,
7 days a week, 365 days a year.
Self-Help Online Tools and Resources
For quick and easy problem resolution, Juniper Networks has designed an online
self-service portal called the Customer Support Center (CSC) that provides you with the
following features:
Find CSC offerings: http://www.juniper.net/customers/support/
Search for known bugs: http://www2.juniper.net/kb/
Find product documentation: http://www.juniper.net/techpubs/
Find solutions and answer questions using our Knowledge Base: http://kb.juniper.net/
Download the latest versions of software and review release notes:
http://www.juniper.net/customers/csc/software/
Search technical bulletins for relevant hardware and software notifications:
https://www.juniper.net/alerts/
Join and participate in the Juniper Networks Community Forum:
http://www.juniper.net/company/communities/
Open a case online in the CSC Case Management tool: http://www.juniper.net/cm/
Opening a Case with JTAC
You can open a case with JTAC on the Web or by telephone.
Use the Case Management tool in the CSC at http://www.juniper.net/cm/.
Call 1-888-314-JTAC (1-888-314-5822 toll-free in the USA, Canada, and Mexico).
For international or direct-dial options in countries without toll-free numbers, see
http://www.juniper.net/support/requesting-support.html.
46 Copyright 2015, Juniper Networks, Inc.
Requesting Technical Support
Revision History
5 March 2015Revision 1, Firefly Perimeter - Release 12.1X47-D20.
Copyright 2015, Juniper Networks, Inc. All rights reserved.
Juniper Networks, Junos, Steel-Belted Radius, NetScreen, and ScreenOS are registered trademarks of Juniper Networks, Inc. in the United
States and other countries. The Juniper Networks Logo, the Junos logo, and JunosE are trademarks of Juniper Networks, Inc. All other
trademarks, service marks, registered trademarks, or registered service marks are the property of their respective owners.
Juniper Networks assumes no responsibility for any inaccuracies in this document. Juniper Networks reserves the right to change, modify,
transfer, or otherwise revise this publication without notice.
Copyright 2015, Juniper Networks, Inc. 47
También podría gustarte
- A Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryDe EverandA Heartbreaking Work Of Staggering Genius: A Memoir Based on a True StoryCalificación: 3.5 de 5 estrellas3.5/5 (231)
- The Sympathizer: A Novel (Pulitzer Prize for Fiction)De EverandThe Sympathizer: A Novel (Pulitzer Prize for Fiction)Calificación: 4.5 de 5 estrellas4.5/5 (119)
- Never Split the Difference: Negotiating As If Your Life Depended On ItDe EverandNever Split the Difference: Negotiating As If Your Life Depended On ItCalificación: 4.5 de 5 estrellas4.5/5 (838)
- Devil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaDe EverandDevil in the Grove: Thurgood Marshall, the Groveland Boys, and the Dawn of a New AmericaCalificación: 4.5 de 5 estrellas4.5/5 (265)
- The Little Book of Hygge: Danish Secrets to Happy LivingDe EverandThe Little Book of Hygge: Danish Secrets to Happy LivingCalificación: 3.5 de 5 estrellas3.5/5 (399)
- Grit: The Power of Passion and PerseveranceDe EverandGrit: The Power of Passion and PerseveranceCalificación: 4 de 5 estrellas4/5 (587)
- The World Is Flat 3.0: A Brief History of the Twenty-first CenturyDe EverandThe World Is Flat 3.0: A Brief History of the Twenty-first CenturyCalificación: 3.5 de 5 estrellas3.5/5 (2219)
- The Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeDe EverandThe Subtle Art of Not Giving a F*ck: A Counterintuitive Approach to Living a Good LifeCalificación: 4 de 5 estrellas4/5 (5794)
- Team of Rivals: The Political Genius of Abraham LincolnDe EverandTeam of Rivals: The Political Genius of Abraham LincolnCalificación: 4.5 de 5 estrellas4.5/5 (234)
- Rise of ISIS: A Threat We Can't IgnoreDe EverandRise of ISIS: A Threat We Can't IgnoreCalificación: 3.5 de 5 estrellas3.5/5 (137)
- Shoe Dog: A Memoir by the Creator of NikeDe EverandShoe Dog: A Memoir by the Creator of NikeCalificación: 4.5 de 5 estrellas4.5/5 (537)
- The Emperor of All Maladies: A Biography of CancerDe EverandThe Emperor of All Maladies: A Biography of CancerCalificación: 4.5 de 5 estrellas4.5/5 (271)
- The Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreDe EverandThe Gifts of Imperfection: Let Go of Who You Think You're Supposed to Be and Embrace Who You AreCalificación: 4 de 5 estrellas4/5 (1090)
- Her Body and Other Parties: StoriesDe EverandHer Body and Other Parties: StoriesCalificación: 4 de 5 estrellas4/5 (821)
- The Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersDe EverandThe Hard Thing About Hard Things: Building a Business When There Are No Easy AnswersCalificación: 4.5 de 5 estrellas4.5/5 (344)
- Hidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceDe EverandHidden Figures: The American Dream and the Untold Story of the Black Women Mathematicians Who Helped Win the Space RaceCalificación: 4 de 5 estrellas4/5 (890)
- Elon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureDe EverandElon Musk: Tesla, SpaceX, and the Quest for a Fantastic FutureCalificación: 4.5 de 5 estrellas4.5/5 (474)
- The Unwinding: An Inner History of the New AmericaDe EverandThe Unwinding: An Inner History of the New AmericaCalificación: 4 de 5 estrellas4/5 (45)
- The Yellow House: A Memoir (2019 National Book Award Winner)De EverandThe Yellow House: A Memoir (2019 National Book Award Winner)Calificación: 4 de 5 estrellas4/5 (98)
- The Perks of Being a WallflowerDe EverandThe Perks of Being a WallflowerCalificación: 4.5 de 5 estrellas4.5/5 (2099)
- CCNP Security Firewall NotesDocumento44 páginasCCNP Security Firewall NotesdwthomasAún no hay calificaciones
- On Fire: The (Burning) Case for a Green New DealDe EverandOn Fire: The (Burning) Case for a Green New DealCalificación: 4 de 5 estrellas4/5 (73)
- Bishop Owen - Exploring ForthDocumento183 páginasBishop Owen - Exploring ForthbcflyersAún no hay calificaciones
- Unit Wise Java Important Questions1Documento3 páginasUnit Wise Java Important Questions1honaday945100% (5)
- Integrating With Oracle HCM CloudDocumento432 páginasIntegrating With Oracle HCM CloudsjawadAún no hay calificaciones
- (Synthesis Lectures On Digital Circuits & Systems) Steven F. Barrett - Arduino V - Machine Learning-Springer (2023)Documento213 páginas(Synthesis Lectures On Digital Circuits & Systems) Steven F. Barrett - Arduino V - Machine Learning-Springer (2023)Prashantha KumarAún no hay calificaciones
- CCNA Security Lab 7 - Using ACLs To Secure Access To Cisco IOS Routers - CLIDocumento12 páginasCCNA Security Lab 7 - Using ACLs To Secure Access To Cisco IOS Routers - CLIvelramsenAún no hay calificaciones
- CCNA Security Lab 16 - Cisco IOS Auto Secure - CLIDocumento10 páginasCCNA Security Lab 16 - Cisco IOS Auto Secure - CLIvelramsenAún no hay calificaciones
- CCNA Security Lab 12 - Catalyst Switch STP and DTP Security - CLI PDFDocumento13 páginasCCNA Security Lab 12 - Catalyst Switch STP and DTP Security - CLI PDFvelramsenAún no hay calificaciones
- Networking Fundamentals SolutionsDocumento14 páginasNetworking Fundamentals SolutionsEVAN MARSHALLAún no hay calificaciones
- Model Commissioning Plan (Sample)Documento5 páginasModel Commissioning Plan (Sample)Anurag KumbhareAún no hay calificaciones
- Business Value OpenshiftDocumento22 páginasBusiness Value OpenshiftAlex KarasuluAún no hay calificaciones
- QOS Lab GuideDocumento170 páginasQOS Lab Guidekzarne735Aún no hay calificaciones
- CCNA Security Lab 14 - Cisco IOS SYSLOG and SNMP Configuration - CLIDocumento12 páginasCCNA Security Lab 14 - Cisco IOS SYSLOG and SNMP Configuration - CLIvelramsenAún no hay calificaciones
- CPS B6Documento5 páginasCPS B6velramsenAún no hay calificaciones
- CPS B6Documento5 páginasCPS B6velramsenAún no hay calificaciones
- CPS B5Documento8 páginasCPS B5velramsenAún no hay calificaciones
- CPS B7Documento1 páginaCPS B7velramsenAún no hay calificaciones
- CPS B2Documento7 páginasCPS B2velramsenAún no hay calificaciones
- FortiGate 80C LENC QuickStartDocumento2 páginasFortiGate 80C LENC QuickStarteswaranslmAún no hay calificaciones
- CCIE RS v5 TS - B1 Variant Configuration ErrorsDocumento8 páginasCCIE RS v5 TS - B1 Variant Configuration ErrorsvelramsenAún no hay calificaciones
- CCNA Security Lab 7 - Using ACLs To Secure Access To Cisco IOS Routers - CLIDocumento12 páginasCCNA Security Lab 7 - Using ACLs To Secure Access To Cisco IOS Routers - CLIvelramsenAún no hay calificaciones
- CPS B3Documento8 páginasCPS B3velramsenAún no hay calificaciones
- CCNA Security Lab 17 - Cisco SDM One-Step Lockdown - SDMDocumento13 páginasCCNA Security Lab 17 - Cisco SDM One-Step Lockdown - SDMvelramsenAún no hay calificaciones
- FGT Overview and DesignDocumento11 páginasFGT Overview and DesignUmAiR AAún no hay calificaciones
- CCNA Security Lab 3 - Cisco Context-Based Access Control - CLIDocumento10 páginasCCNA Security Lab 3 - Cisco Context-Based Access Control - CLIvelramsenAún no hay calificaciones
- MPLST 20 S 06 L 00Documento2 páginasMPLST 20 S 06 L 00velramsenAún no hay calificaciones
- CCNA Security Lab 18 - Cisco IOS Zone-Based Policy Firewall - SDMDocumento22 páginasCCNA Security Lab 18 - Cisco IOS Zone-Based Policy Firewall - SDMvelramsenAún no hay calificaciones
- CcieDocumento14 páginasCcievelramsenAún no hay calificaciones
- CP R77.10 QoS AdminGuideDocumento95 páginasCP R77.10 QoS AdminGuideMSAún no hay calificaciones
- mplst20lg FMDocumento1 páginamplst20lg FMvelramsenAún no hay calificaciones
- MPLST 20 S 05 L 00Documento2 páginasMPLST 20 S 05 L 00velramsenAún no hay calificaciones
- CCIE R&S Lab Exam Version 5.0 ChecklistDocumento10 páginasCCIE R&S Lab Exam Version 5.0 ChecklistvelramsenAún no hay calificaciones
- mplst20SG FM Vol 2Documento1 páginamplst20SG FM Vol 2velramsenAún no hay calificaciones
- MPLS VPN ChecklistDocumento4 páginasMPLS VPN ChecklistvelramsenAún no hay calificaciones
- MPLST 20 S 01 L 99Documento4 páginasMPLST 20 S 01 L 99velramsenAún no hay calificaciones
- mplst20lg FMDocumento1 páginamplst20lg FMvelramsenAún no hay calificaciones
- MPLST v2.0 TOC Vol 1Documento8 páginasMPLST v2.0 TOC Vol 1velramsenAún no hay calificaciones
- Shader FundamentalsDocumento154 páginasShader FundamentalsAlaa ZainAún no hay calificaciones
- CXCI Cordex 2v0 Quick RefDocumento2 páginasCXCI Cordex 2v0 Quick RefGuillermo OvelarAún no hay calificaciones
- Distributed Database DesignDocumento22 páginasDistributed Database DesignAmit Vashisht100% (2)
- ResumeDocumento1 páginaResumechirag m oAún no hay calificaciones
- Mr. Salamudeen Alhassan Department of Computer Sc. UDS, Navrongo, GhanaDocumento15 páginasMr. Salamudeen Alhassan Department of Computer Sc. UDS, Navrongo, GhanaAziz RahimAún no hay calificaciones
- Intune Implementation TMINUSDocumento61 páginasIntune Implementation TMINUSSouleymane TraoréAún no hay calificaciones
- This OVF Package Requires Unsupported Hardware .Virtualbox-2.2Documento5 páginasThis OVF Package Requires Unsupported Hardware .Virtualbox-2.2bakieAún no hay calificaciones
- Mainframe230 Blogspot inDocumento4 páginasMainframe230 Blogspot inArunachalam NarayananAún no hay calificaciones
- Introducing the Vertica Analytic Database - Query Data 214x Faster on 90% Less HardwareDocumento10 páginasIntroducing the Vertica Analytic Database - Query Data 214x Faster on 90% Less HardwareRamprasadh KottapalliAún no hay calificaciones
- GridWorld AP CompScienceDocumento129 páginasGridWorld AP CompScienceJoseph VandegriftAún no hay calificaciones
- Examen Analista FuncionalDocumento7 páginasExamen Analista FuncionalAlexia HaedoAún no hay calificaciones
- System Admin QuestionsDocumento9 páginasSystem Admin QuestionsNagaraju KasaAún no hay calificaciones
- WhitePaper Riverbed TechRequirements RFPDocumento9 páginasWhitePaper Riverbed TechRequirements RFPKevin WhitneyAún no hay calificaciones
- A Framework To Effectively Develop Insider Threat Controls: Randy Trzeciak Dan CostaDocumento35 páginasA Framework To Effectively Develop Insider Threat Controls: Randy Trzeciak Dan CostaJeya Shree Arunjunai RajAún no hay calificaciones
- EJB 3.0 Final PreparedDocumento243 páginasEJB 3.0 Final PreparedjayavardhankotiAún no hay calificaciones
- MK4009GALTechnicalNotes RevADocumento4 páginasMK4009GALTechnicalNotes RevAАлександр КарповAún no hay calificaciones
- 8051 Lab ManualDocumento35 páginas8051 Lab ManualVenkat BalajiAún no hay calificaciones
- Instructions To Candidates: Y10 HL P1 Dave WalkerDocumento18 páginasInstructions To Candidates: Y10 HL P1 Dave WalkerSaira AliAún no hay calificaciones
- ROBOMAC 208 NG Programming Manual - EnglishDocumento73 páginasROBOMAC 208 NG Programming Manual - EnglishVASILE ISAILAAún no hay calificaciones
- Fdocuments - in - Verilog HDL BasicsDocumento69 páginasFdocuments - in - Verilog HDL BasicsChristina josephine malathiAún no hay calificaciones
- Prist University, Trichy Campus Department of Comnputer Science and Engineering B.Tech - Arrear Details (Part Time)Documento2 páginasPrist University, Trichy Campus Department of Comnputer Science and Engineering B.Tech - Arrear Details (Part Time)diltvkAún no hay calificaciones
- Checkmarx Open Source Analysis (OSA)Documento2 páginasCheckmarx Open Source Analysis (OSA)maria dianaAún no hay calificaciones
- Zynq Petalinux Boot LogDocumento5 páginasZynq Petalinux Boot LogHeshsham BasitAún no hay calificaciones